Flawed cache keys unlock a giant backdoor to your website
The potentially devastating consequences of attacks against contemporary web caches were once again pulled into stark focus at Black Hat USA this week, as security researcher James Kettle documented his ongoing study in the field.
Long gone are the days when the web simply consisted of endpoints connected directly to host web servers. Today, this content is served by a rapidly expanding, and increasingly complex, global network of caches.
Web caching – the process of storing web content and other data at various points along the delivery path – is widely employed as a means to increase site performance and scalability.
But this system is not without its flaws. Although caching can help improve site responsiveness and reduce network costs, these additional layers also serve to increase the attack surface, leaving web apps wide open to abuse.
What’s your poison?
James Kettle, head of research at PortSwigger Web Security, is no stranger to the dark arts of web cache poisoning. He first showcased his exploits using this hacking technique at Black Hat 2019.
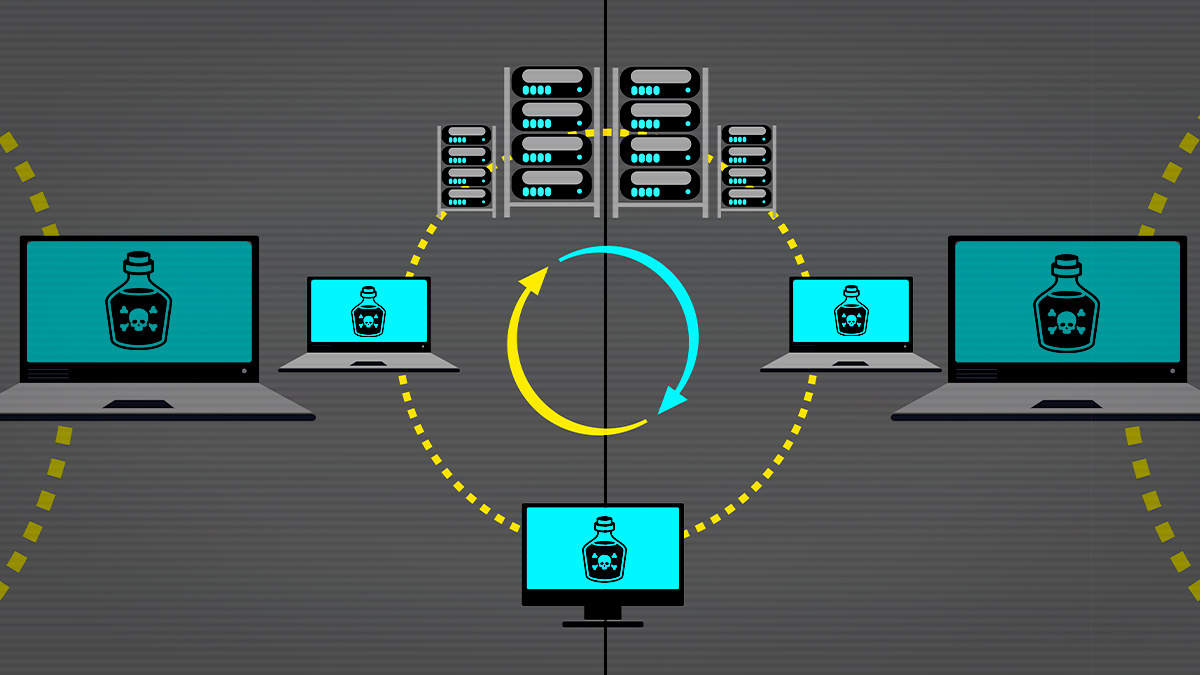
“Web cache poisoning is a general term for when you trick a cache into saving a harmful page and serving it up to users,” Kettle said. (Disclosure: PortSwigger is The Daily Swig’s parent company.)
BACKGROUND Web caching may be the backdoor in your site
In a classic web cache poisoning attack, the researcher explained, a payload is inserted into an obscure HTTP header.
Two years on, and Kettle is back with more research that continues to make short shrift of web caches – this time by exploiting misguided transformations, request line normalization, and insecurely stored cache key components.
“Any of these can cause trouble for your application,” he warned.
 Web cache poisoning involves tricking a cache into saving a harmful page and serving it up to users
Web cache poisoning involves tricking a cache into saving a harmful page and serving it up to users
Cache control
At the virtual Black Hat USA conference today (August 5), Kettle shared advanced techniques to demonstrate how some “seriously esoteric cache behaviors” could be combined to create hard-hitting exploit chains.
As detailed in the accompanying white paper, his web cache entanglement exploits included persistently poisoning every page on an online newspaper, compromising the administration interface on an internal US Department of Defense intelligence website, and disabling Firefox updates globally.
Read more of the latest news from Black Hat USA 2020
Moving on, Kettle turned his attention to the website of a cache provider, showing how it was possible to achieve persistent denial of service (DoS) on the Cloudflare login page with just one poisonous redirect request.
It doesn’t end there: Zendesk, Akamai, and the Ruby on Rails framework were all subject to distinct web cache poisoning exploits, most of which are now patched following coordinated disclosure of the vulnerabilities.
“My favorite exploit was the Firefox update DoS,” Kettle told The Daily Swig in the lead-up to his presentation. “I only discovered it because I happened to be using Firefox at the time, and the attack only requires a single-character change to a legitimate request.”
Defending your web infrastructure
Kettle’s latest research may leave many questioning the viability of today’s web cache infrastructure. Fortunately, however, there are several steps that can be taken to help protect your web apps from abuse.
“There are some broad approaches you can take to avoid the worst issues,” Kettle outlines in his technical paper.
“Firstly, avoid ever rewriting the cache key. Instead, rewrite the actual request – this achieves the same performance gains while massively reducing the likelihood of cache poisoning problems.
“Second, ensure your application doesn’t support fat GET requests. Finally, as a defense-in-depth measure, patch vulnerabilities that are deemed unexploitable due to browser constraints, like self-XSS, encoded-XSS, or input reflection in a resource file.”
To help detect these issues, Kettle has released an update to the Param Miner Burp Suite extension.
Perhaps unsurprisingly, though, these mitigations come with a hefty caveat.
“The sheer diversity of caching issues discovered during this research suggests that there are plenty of as-yet undiscovered flaws in our future,” Kettle said. “As such, I expect to see entire new classes of cache poisoning issues arise in future.”






