Trusted by
security professionals
security professionals

Everything you need to stay ahead
The latest AppSec news from PortSwigger

The top 10 web hacking techniques of
2025
Welcome to the next generation of Burp
Suite
Burp on Tour 2025: bringing the AppSec
community together

HTTP/1.1 Must Die: The Desync Endgame
Begins
Shadow Repeater: AI Enhanced Manual
Testing
PortSwigger and SAP strategic
partnership
Get to know the PortSwigger community
Burp Suite is trusted globally
Security resources for everyone
The PortSwigger Blog

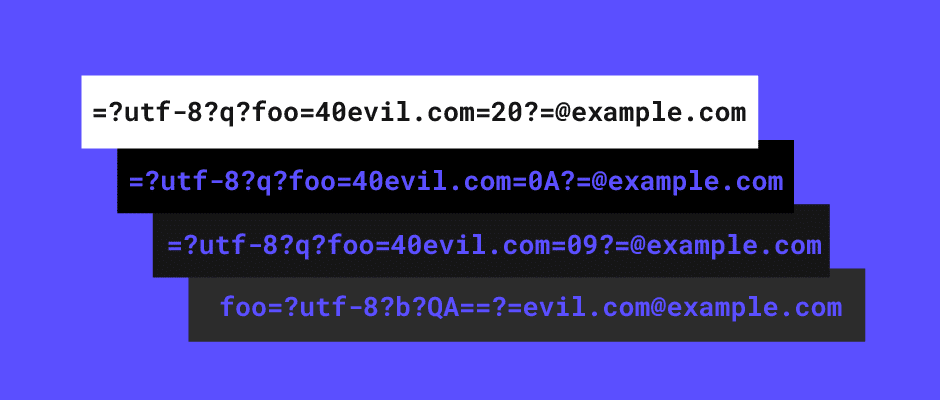
The top 10 web hacking techniques of
2024
Burp Suite DAST and Burp Suite
Professional

Become a Burp Suite Certified
Practitioner

Get started with the Web Security
Academy
Learn with PortSwigger Research