A stark blue-red dichotomy can cause tunnel vision in researchers
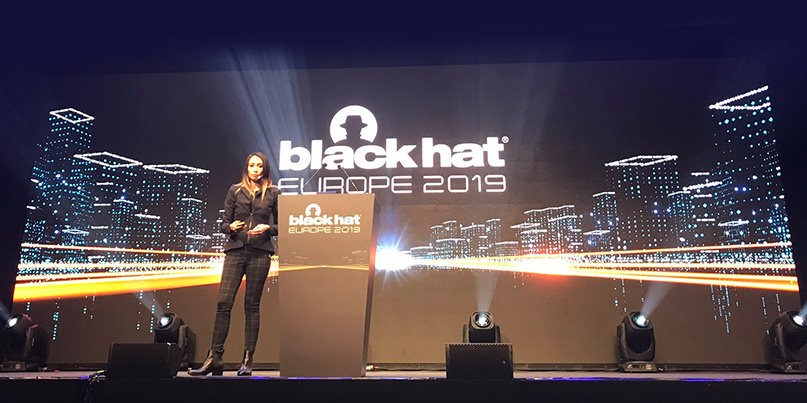
Facebook red teamer Amanda Rousseau lamented an incipient hyper-specialization among infosec professionals during her keynote address at Black Hat Europe 2019 today (December 4).
Rousseau, a former forensic technician for the US government and malware researcher in the private sector, observed a worrying shortage of industry generalists, likening a role in infosec to diving down Alice in Wonderland’s proverbial rabbit hole.
“In our reality, [there] are many rabbit holes,” she told delegates at the conference in London.
“There’s so many that there’s not enough of us to go down all of them – and they keep changing over time.”
Rousseau’s talk on traversing the blue-red infosec spectrum – spanning defensive and offensive teams – was framed by three best-practice principles: looking beyond the surface layer, breaking out of arbitrary team colors, and effectively driving impact.
Broadly sharing the same skillset, the blue (defensive) and red (offensive) teams are effectively “sparring partners” that must collaborate closely, said Rousseau.
To infosec newcomers, championing an “adversarial mindset” might therefore seem contradictory. But in the cybersecurity context, being adversarial – which Rousseau said cannot be “learned in institutions” – is about thinking outside the box and challenging assumptions.
Rousseau, a former blue teamer, said a stark blue-red dichotomy can cause tunnel vision in researchers, characterized by rigid assumptions about how detection works and whitelisting applications too early.
Read more of the latest news from Black Hat Europe 2019
Citing a successful blue-red collaboration at Facebook, Rousseau recalled conducting cryptocurrency mining on thousands of servers – an exercise that included making a Linux rootkit to hide within internal servers and working with insiders to ensure stability.
Scenarios must span a range of difficulty levels, she recommended.
For instance, eating pancakes for free at a chain restaurant could be achieved simply with a “dine and dash”, while a complex approach might involve fake currency. Setting off a fire alarm or threatening staff, meanwhile, would classify as extreme methods.
Attack plans must also be realistic, said Rousseau. Redundancy, access to threat intelligence, legality, and emotional exploitation – “Would you make someone cry to get what you want?” – are the key variables here.
She advised her audience to resist the urge to extrapolate from small datasets. A 100% detection rate from 100 attack cases isn’t compelling, Rousseau said.
“Maybe 100,000 or even a million should be your baseline.”
She added: “You need more data on outliers as you never know how things will be deployed in the environment.”
Anyone justifying a course of action on “instinct” is swiftly rebuffed by Rousseau: “Where is your supporting data – how do you know it will work?”
Imprecision from red teamers – “you should add more monitoring” being one lazy example – is a recipe for engendering apathy in their blue counterparts.
The latter’s willingness to act on the former’s remedial recommendations is also undermined by a lack of follow-through from red teamers, added Rousseau.
The Daily Swig will be back with more news from Black Hat Europe throughout the week.
RELATED WHID Elite: Weaponized USB gadgets boast multiple features for the stealthy red teamer






