DroneSploit seeks to consolidate a fragmented drone-hacking tools market

Security researchers are putting together a Metasploit-like framework tailored to drone hacking.
Progress in developing the tool, dubbed ‘DroneSploit’, was outlined by its developers, Alexandre D’Hondt and Yannick Pasquazzo, during an Arsenal session at the Black Hat Europe conference in London today (December 5).
“A Metasploit-like framework tailored to drone hacking is needed in order to streamline research in an emerging field of IoT security research,” D’Hondt told The Daily Swig.
“Drones constitute a big and motley market with various technologies involved,” he explained. “Currently, many researchers demonstrate vulnerable functionalities with their related proof-of-concept scripts, [which are] often difficult to reuse efficiently.
“As it turned out to be extremely effective and inescapable in penetration testing, it was the ideal model to design a new tool that could gather all these results – especially for drone hacking.”
WiFi-controlled drones
For now, DroneSploit is designed to target only WiFi-controlled drones and includes a set of modules (based on Aircrack-NG) that allows users to hack into poorly configured ones.
DroneSploit currently supports modules for the C-me and Flitt drones (Hobbico). New modules for other brands and models (including Parrot and DJI) are in development and due to be added shortly.
“The ultimate goal is to gather as many exploits as possible on as many drone models as possible,” Pasquazzo told The Daily Swig.
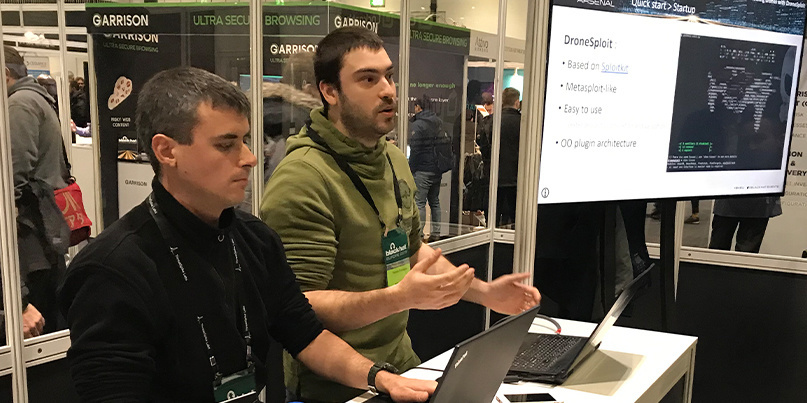 Alexandre D’Hondt and Yannick Pasquazzo presented the DroneSploit framework at Black Hat Europe
Alexandre D’Hondt and Yannick Pasquazzo presented the DroneSploit framework at Black Hat Europe
The type of drone security vulnerabilities the tool is designed to uncover are comparable to the software flaws in PCs and servers that Metasploit helps to reveal to pen testers.
“The tool is designed to work as Metasploit does, so that any user that is already interested in cybersecurity can right away feel familiar with it,” D’Hondt said, adding that a command-line interface can harness modules that automate “exploits for vulnerabilities specific to the target”.
Pasquazzo added: “Just like Metasploit does, this framework aims to gather modules that automate actions and exploits on drones that allow [checks] for vulnerable ones.
“This is then a base for building new automations of exploits for discovered vulnerabilities, like for instance a flawed update mechanism that does not perform integrity checking, whose automated exploit allows an attacker to push an evil update to the drone.”
RELATED IoT security: Bug bounties a vital last line of defense, academic study suggests
The tool is chiefly geared towards pooling knowledge in the field of drone hacking, the researchers explained.
“[The project] proposes a dedicated framework for security enthusiasts who would like to share their knowledge about drone hacking by automating actions and attacks for assessing the security of this specific kind of device,” D’Hondt said.
“This idea originates from the fact that we could find lots of small specific tools for various models of drones, but we could never find a tool gathering all these [things].”
Labor of love
Developing the CLI-based tool has been something of a labor of love, as D’Hondt explained.
“The underlying layer for creating a toolkit in Python for designing a Metasploit-like framework was surely the most laborious task in this project, but finally led to Sploitkit,” he said.
With this package, the researcher said it was then easy to build new commands and modules for DroneSploit based on the community’s analysis and the drones acquired by the researchers for testing.
Pasquazzo added that the two developers wanted to encourage other experts with an interest in programming and drone hacking to contribute towards further development of the project, which he believes is sorely needed by the IoT security research community.
“If you take two of the most popular drone brand on the market, DJI and Parrot, you can find a lot of open source hacking projects, but it still lacks a platform to gather and automate the process,” Pasquazzo explained.
“This is where we try to make a difference with our tool: gather, facilitate, inspire.”
The two researchers are also open to collaborating with drone manufacturers in the project’s ongoing development.
“Unfortunately, the drones we had available for the initial pen test at the start of this project were the Flitt and the C-me, which are both manufactured by Hobicco, who went bankrupt last year,” Pasquazzo said.
“There was very little information on those models on the internet, so we started from zero and retro-engineered the product to find our exploits, and couldn’t contact Hobicco to suggest any security patch.”
He added: “We since then acquired a Tello, produced by DJI, which has a bigger community and some exploits already available.
“We would be glad to work with them or any other interested drone company in the future,” he concluded.
Read more of the latest hacking tools and security research from Black Hat Europe 2019.
YOU MIGHT ALSO LIKE Finland launches cybersecurity seal of approval for IoT devices






