Developers are issuing hotfix

UPDATED Brave, the privacy-focused web browser, is exposing users’ activity on Tor’s hidden servers – aka the ‘dark web’ – to their internet service providers, it has been confirmed.
Brave is shipped with a built-in feature that integrates the Tor anonymity network into the browser, providing both security and privacy features that can help obscure a user’s activity on the web.
Tor is also used to access .onion websites, which are hosted on the dark net.
Earlier today (February 19), a blog post from ‘Rambler’ claimed that Brave was leaking DNS requests made in the Brave browser to a user’s ISP.
Read more of the latest privacy news
DNS requests are unencrypted, meaning that any requests to access .onion sites using the Tor feature in Brave can be tracked – a direct contradiction to its purpose in the first place.
The blog post reads: “Your ISP or DNS provider will know that a request made to a specific Tor site was made by your IP. With Brave, your ISP would know that you accessed somesketchyonionsite.onion.”
Following the disclosure, well-known security researchers including PortSwigger Web Security’s James Kettle independently verified the issue using the Wireshark packet analysis tool.
“I just confirmed that yes, Brave browsers Tor mode appear to leak all the .onion addresses you visit to your DNS provider,” Kettle tweeted, providing a screenshot for evidence.
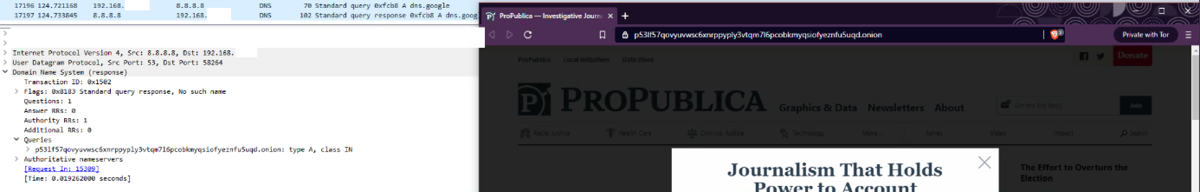 Security researcher James Kettle independently verified the Brave browser privacy issue
Security researcher James Kettle independently verified the Brave browser privacy issue
User response
Considering that the Tor Browser was specifically built to hide a users’ internet browsing from their ISP, the news has provoked a vociferous response online.
“Privacy my ass,” wrote Twitter user @s_y_m_f_m, while other called the findings “appalling”.
The issue has been present in the stable release since November 2020, and was reported “in mid January”, a Brave developer told The Daily Swig.
A fix has since been issued and is available for download here.
INSIGHT Tor security: Everything you need to know about the anonymity network
A spokesperson for Brave told The Daily Swig: “In mid-January 2021, we were made aware of a bug that would allow a network attacker to see DNS requests that were made in a private window in Brave with Tor connectivity.
“The root cause was a new adblocking feature called CNAME adblocking which initiated DNS requests that did not go through Tor in order to check if a domain should be blocked.
“This bug was discovered and reported by xiaoyinl on HackerOne. We responded immediately to the report and included a fix for this vulnerability in the February 4, 2021 in the nightly update.
“As is our usual process for bug fixes, we have been testing the changes in nightly to make sure that they didn't cause regressions or other bugs before releasing to the stable channel.”
They added: “We encourage people to continue to report bugs like this on HackerOne so we can fix them as quickly as possible.
“We also want to remind our community that using a private window with Tor connectivity through Brave is not the same as using the Tor Browser.
“If your personal safety depends on remaining anonymous, we highly recommend using Tor Browser instead of Brave Tor windows.”
This article has been updated to include comment from Brave and further information. An earlier version stated that the issue has been present since 2019, this has been corrected to 2020.
YOU MAY ALSO LIKE BIND implements DNS-over-HTTPS to offer enhanced privacy






