Affected web plugins had more than three million downloads combined

Data-stealing malware that hid undetected for years shows that even popular web browser extensions can be vulnerable to exploitation, security researchers from Avast Threat Labs have warned.
A blog post from Avast Threat Labs researchers contains technical details on how the malware, titled ‘CacheFlow’, went undetected for at least three years.
The malware in question, which was hidden in popular third-party web extensions, contained backdoors that downloaded and executed arbitrary JavaScript.
It attempted to steal personal information such as birth dates, email addresses, geolocations, and device activity taken from a victim’s Google account, before sending it back to the attacker’s control server.
CacheFlow also replaced links from Google, Bing, and other search engine queries with hijacked links serving phishing sites and advertisements.
YOU MAY LIKE Browser security briefing: Google and Mozilla lay the groundwork for a ‘post-XSS world’
“Anytime a user clicked on a link, the extensions sent information about the click to the attacker’s control server,” researcher Jan Vojtesek told The Daily Swig.
“This can optionally send a command to redirect the victim from the real link target to a new hijacked URL before redirecting them to the actual website they wanted to visit.”
Hidden danger
The malware was spread via dozens of malicious Chrome and Edge browser extensions that had an estimated combined three million downloads. A number of the plugins were available on the browsers’ official stores.
Affected extensions included Video Downloader for Facebook, Vimeo Video Downloader, Instagram Story Downloader, and VK Unblock.
The blog post published yesterday (February 3) details how the attackers were able to go unnoticed by a victim before the campaign was discovered in December 2020.
Interestingly, the malware itself did not trigger until three days after the extension was downloaded to avoid immediate detection.
It also avoided detection by assessing whether its victim would have the technical knowledge to spot it on their device.
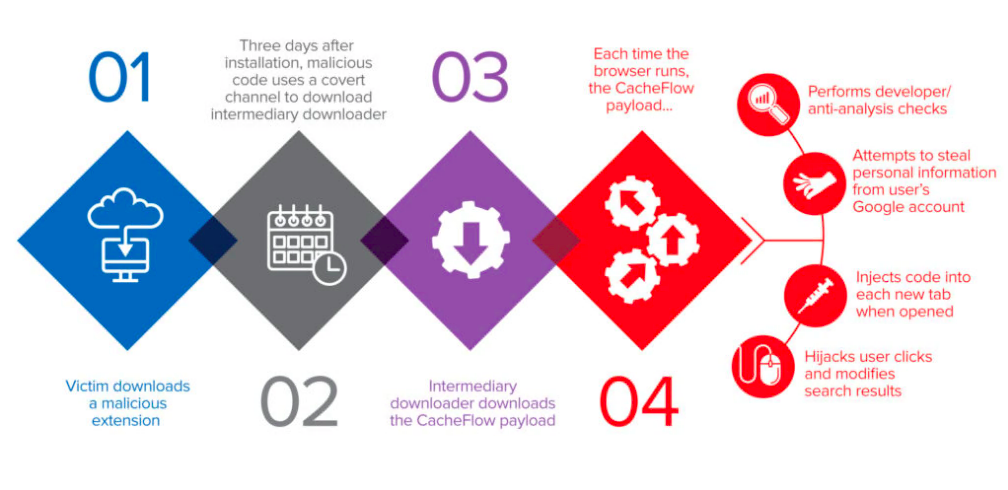 An image shows the various steps undertaken by the CacheFlow malware, courtesy of Avast Threat Labs
An image shows the various steps undertaken by the CacheFlow malware, courtesy of Avast Threat Labs
“First of all, they avoided infecting users who were likely to be web developers,” Avast Threat Labs said.
“They determined this either through the extensions the user had installed or by checking if the user accessed locally-hosted websites.”
It adds: “When the malware detected that the browser developer tools were opened, it would immediately deactivate its malicious functionality.“CacheFlow also checked every Google search query and if the user was googling for one of the malware’s command and control (C&C) domains, it reported this to its C&C server and could deactivate itself as well.”
CacheFlow was notable in particular for the way that the malicious extensions would try to hide their C&C traffic in a covert channel using the Cache-Control HTTP header of their analytics requests, noted researchers.
Researchers believe that the malicious authors were also interested in the analytics requests themselves.
Widespread problem
Avast Threat Labs researchers came across the campaign after Czech researcher Edvard Rejthar from CZ.NIC published this blog post.
On further inspection, the team found that “many other extensions were doing the same thing”.
Google Play reviews cited issues with extensions such as adware as far back as October 2017, leading the team to believe that CacheFlow has been active since at least that time.
Researchers said that the main risk to users is their personal information being exposed.
“Moreover, the extensions can download and execute arbitrary JavaScript with access to the browser extension API, even putting the victim’s payment card data at risk,” researcher Jan Rubin told The Daily Swig.
Read more of the latest news about malware
Google and Microsoft had both taken down all of the malicious plugins in their stores as of December 18, 2020.
It is unlikely that the actors will use the same malware since it is now easily detectable, the researchers said, adding that this campaign “has shown that even popular browser extensions installed from official browser stores can contain malware.
“To lower the risk of being infected by a malicious extension, we recommend that users review carefully the permissions requested by the extensions they intend to install,” Rubin added.
“It is suspicious if an extension requests a permission that is not needed for its advertised functionality.
“We also recommend reading user reviews – it might be the case that other users have already noticed that the extension is behaving suspiciously, and mentioned this in the reviews.”
READ MORE Sharkcop: Google Chrome extension uses machine learning to detect phishing URLs






