Currently in first release, the tool will have a raft of new features added in the coming months

A new open source tool makes it easier to use Hashcat, the powerful password-cracking, command-line tool that uses the power of graphics cards to find the plaintext equivalent of hashed passwords.
CrackQ provides a REST API and a JavaScript graphical user interface (GUI) to interact with Hashcat.
Dan Turner, the developer of CrackQ and a career penetration tester, told The Daily Swig that the goal of CrackQ was to help improve the efficiency of Hashcat, which has become very popular among penetration testers, red teams, and other offensive security researchers.
Results dashboard
CrackQ is not the first GUI tool written for Hashcat, but it has several characteristics that make it unique. The tool is written in Python and interfaces with Hashcat through the libhashcat library.
Python also has many great data science libraries, which make it easier to add analysis and reporting features to Hashcat.
CrackQ can generate various analysis reports and dashboards from Hashcat results, including timing and speed, insecure password patterns, and heatmaps of common city names used in passwords.
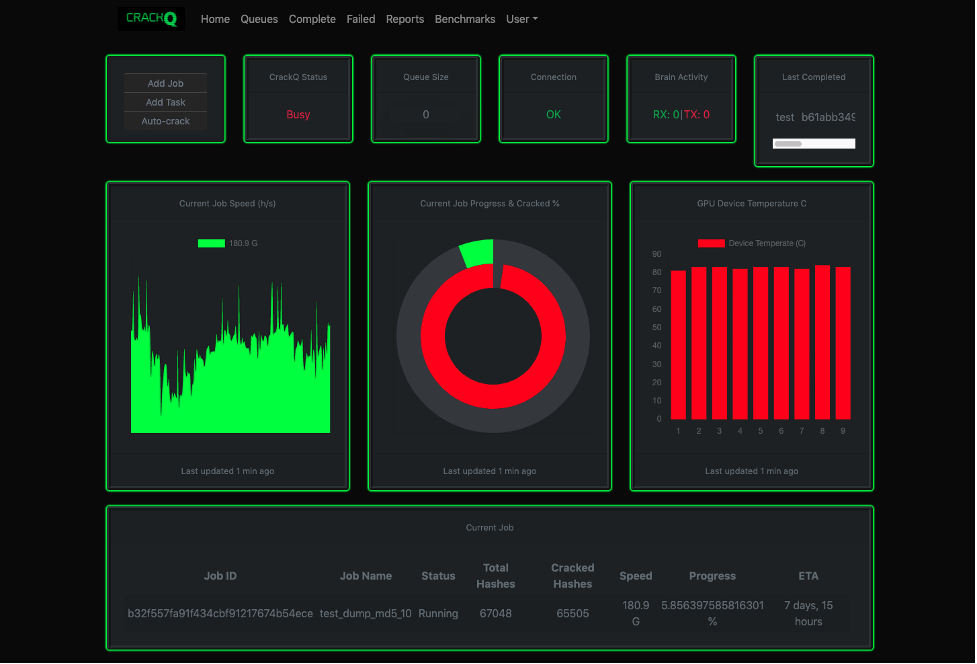 CrackQ provides a GUI for the Hashcat password-cracking tool
CrackQ provides a GUI for the Hashcat password-cracking tool
Other Hashcat tools use distributed computing, where they share the load among several computers. CrackQ, on the other hand, uses a server/client architecture, with all commands running on the server.
“Pen test/red teams commonly use dedicated GPU servers or custom-built rigs, which are then shared by the team,” Turner says.
“However, the application is built using Docker containers. This means that it’s a simple process to quickly create a cloud instance, if that is more suitable for you.”
Single sign-on
CrackQ uses SAML2 authentication, which allows users to offload credential management to an identity provider such as Active Directory and to use multi-factor authentication.
“I needed something I could integrate with single sign-on (SSO) to avoid managing user numbers approaching 100 accounts,” Turner says.
READ MORE Latest hacking tools – Q4 2020
CrackQ is currently in first release. Turner will be expanding the feature set in the coming months.
“This first version was all about setting up a good base, ensuring it’s a very stable application and making it more accessible to everyone,” he said.
“I’m looking forward to the next steps, which will involve adding a lot of automation and improving the analysis/reporting, which will also increase the usability for blue teams.”
RECOMMENDED Meet urlhunter, the URLTeam companion and shortened URL search engine






