Patch now to protect, say researchers
Two vulnerabilities in open source monitoring platform Zabbix could allow an attacker to bypass authentication and execute arbitrary code on a targeted server.
The security flaws were found in Zabbix Web Frontend, a platform used to collect, centralize. and track metrics such as CPU load and network traffic across entire infrastructures.
Researchers from SonarSource, who discovered the bugs, noted that Zabbix is a high-profile target for threat actors due to its popularity, features, and its “privileged position in most company’s networks”.
Issues
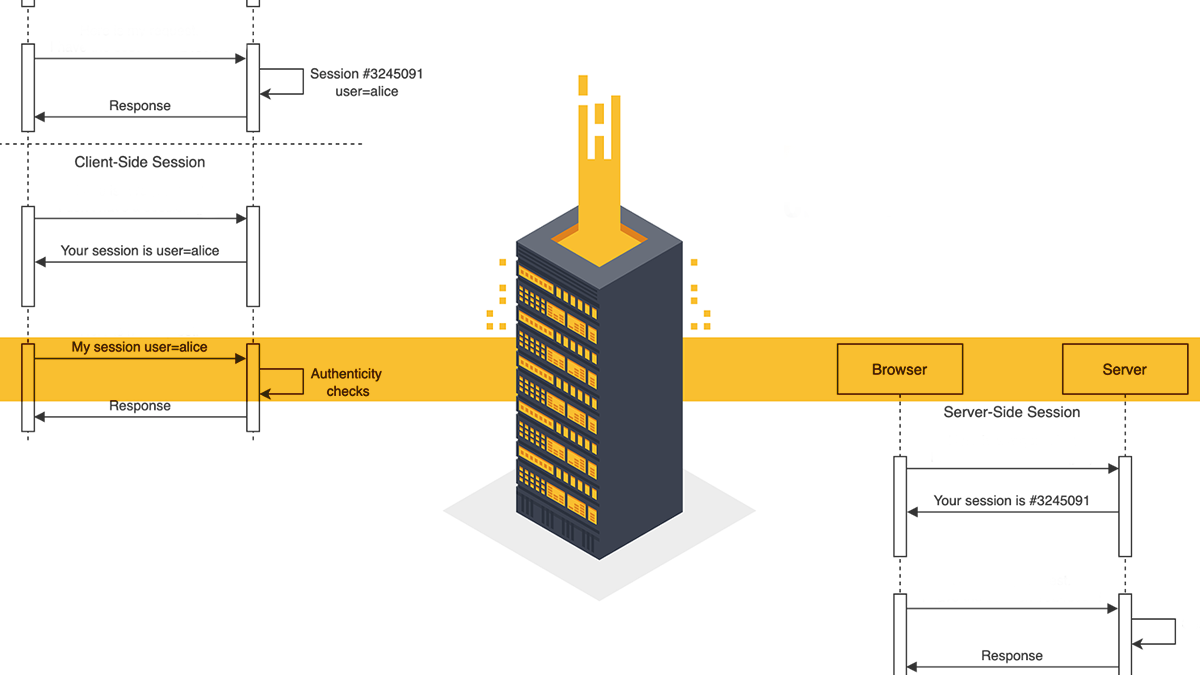
The first vulnerability, tracked as CVE-2022-23131, which was given a severity of 9.1, is unsafe client-side session storage leading to authentication bypass/instance takeover via Zabbix Frontend with configured SAML.
In the case of instances where the SAML SSO authentication is enabled (non-default), session data can be modified by a malicious actor, because a user login stored in the session was not verified.
A malicious unauthenticated actor could exploit this issue to escalate privileges and gain admin access to the Zabbix Frontend.
YOU MAY LIKE Lagging behind? New study highlights weaknesses in open source patch process
A caveat to this is that to perform the attack, SAML authentication is required to be enabled, and the assailant has to know the username of Zabbix user (or use the guest account, which is disabled by default), a security advisory from Zabbix notes.
The second vulnerability found by SonarSource, tracked as CVE-2022-23134, is rated as medium severity and allows some steps of setup.php file to be reachable not only by super-administrators, but by unauthenticated users as well.
A malicious actor could pass step checks and potentially change the configuration of Zabbix Frontend, an advisory notes.
Patch now
In a blog post from SonarSource, the researchers said that when writing and reviewing code related to important security features, “it is easy to make the same assumptions as the original developer who introduced the vulnerability”.
They wrote: “Here, there were no integration tests related to the client-side session storage that could have spotted this behavior.
“Always provide access to sensible services with extended internal accesses (e.g. orchestration, monitoring) over VPNs or a restricted set of IP addresses, harden filesystem permissions to prevent unintended changes, remove setup scripts, etc.”
Finally, the researchers recommended upgrading all instances running a Zabbix Web Frontend to 6.0.0beta2, 5.4.9, 5.0.19, or 4.0.37.
RECOMMENDED Poisoned pipelines: Security researcher explores attack methods in CI environments






