Top infosec trends in the social media spotlight this week

The big news on everyone’s radar this week was the arrest of WikiLeaks founder Julian Assange in London.
Assange, who has been living in the Ecuadorian embassy for more than seven years, was forcibly removed by London’s Metropolitan Police on Thursday to face charges related to skipping bail in 2010.
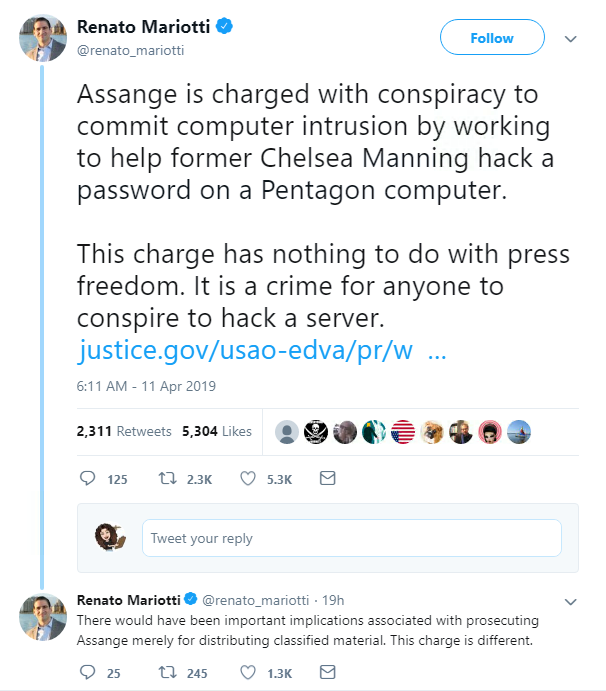
It was later reported that Assange has also been arrested on a US extradition warrant, where he is accused of computer intrusion crimes related to the 2010 cable leaks by former US Army intelligence analyst Chelsea Manning.
Australian citizen Assange is accused of agreeing to hack a password in a US government classified computer.
The US Department of Justice alleges that during discussions with Manning, during which she told Assange she had no more documents left to share, he replied: “Curious eyes never run dry in my experience.”
You can read the full indictment here.
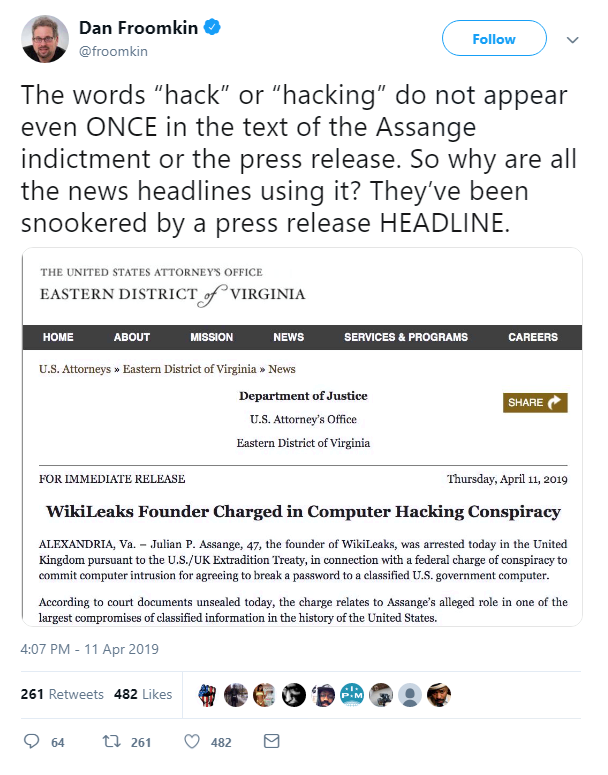
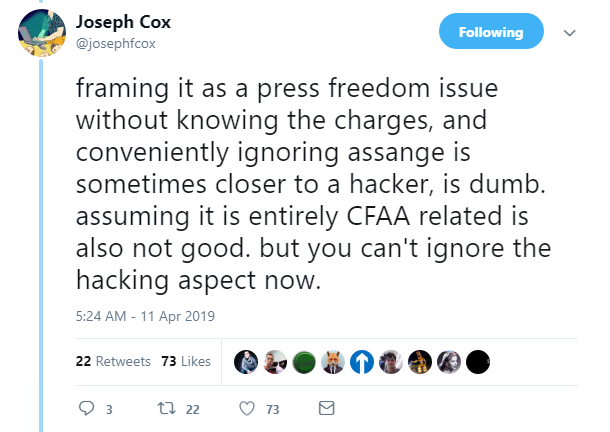
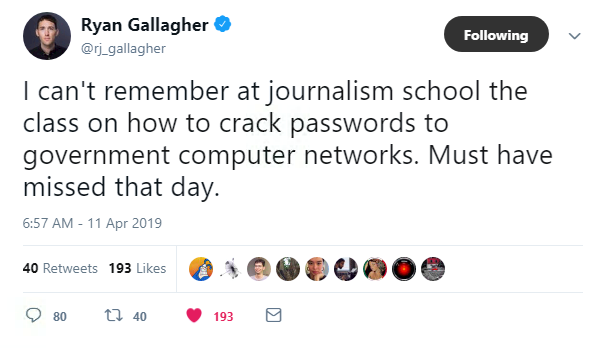
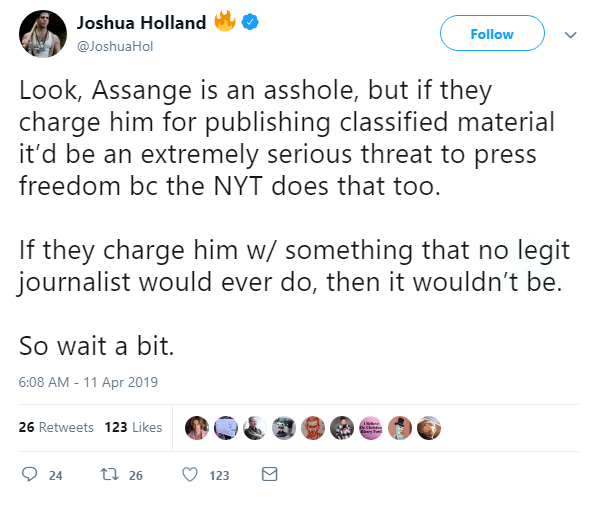
His detention by London police sparked a furious debate online, with his supporters in outcry over the “violation of press freedom”.
Others, however, dismissed notions that Assange is classed as a journalist, arguing that cracking hashed passwords isn’t in a reporter’s job description.
So what’s the truth? Well, here’s what we know.
Assange denied failing to surrender to UK courts but was found guilty by a judge – he faces up to 12 months in prison.
On May 2, he will appear via video link at Westminster Magistrates Court in London in relation to his extradition case. He will later have the opportunity to lodge an appeal.
There’s no way of knowing whether he will be extradited to face the computer crimes accusations.
In the meantime, here’s one sensible piece of advice: just wait a bit.
Elsewhere in the US, it’s been a busy week for cybersecurity news.
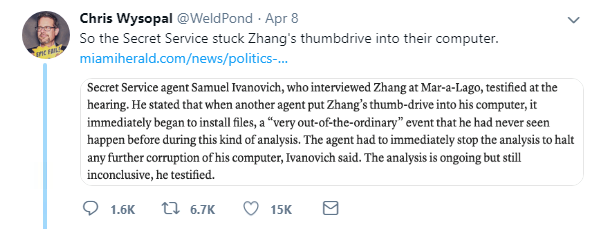
Remember when Chinese citizen Yujing Zhang was arrested at Trump’s Mar-a-Lago club in Florida with suspect items including multiple phones, two passports, and a USB stick laden with malware?
Well it turns out the US Secret Service – trained security professionals – plugged the USB into one of their computers. We’re not making this up.
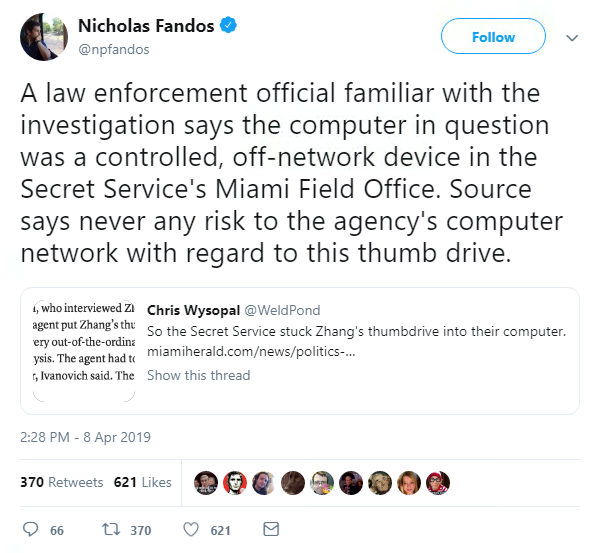
The US government claims the USB was plugged into a “controlled, off-network device”, according to The New York Times reporter Nicholas Fandos.
Even so, it’s a good time to remember that plugging a USB stick into any device when you don’t know what’s on it is definitely *not* a good idea.
In other US government news, Homeland Security secretary Kirstjen Nielsen quit this week after her relationship with President Trump allegedly turned sour.
This wasn’t great news for the government’s stance on cybersecurity, considering Nielsen was a specialist in the field.
Trump has yet to appoint a new secretary, but Customs and Border Protection Commissioner Kevin McAleenan will occupy the post temporarily – signaling Trump’s priorities for the department.
One US lawmaker bringing citizen’s digital protections to the forefront is Senator Elizabeth Warren, who this week called for companies who leak private data to be held criminally liable.
Warren proposed a bill that would see CEOs of companies generating an excess of $1 billion in annual revenue handed a year’s prison sentence for a first time offense.
She was lauded online for her dedication to cybersecurity – even if her supporters are sceptical that it will pass.
You can read more about Warren’s proposition in this piece by Catherine Chapman for The Daily Swig.
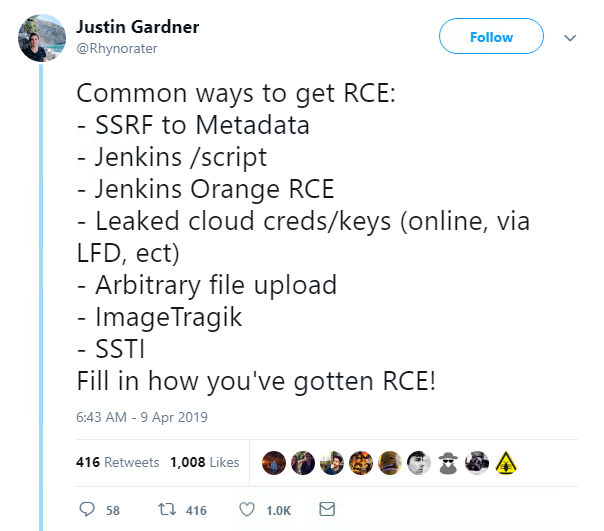
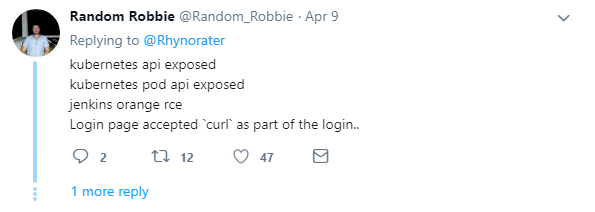
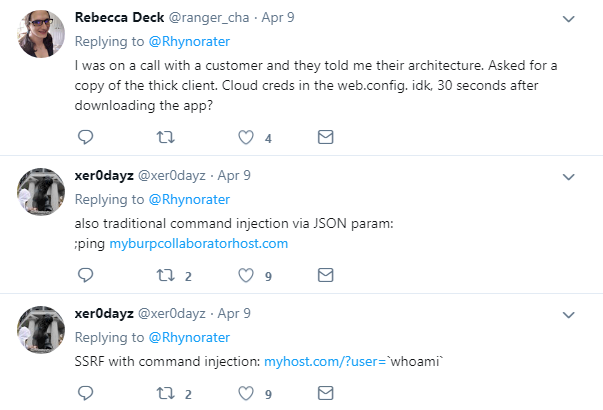
Finally, researchers shared their tips and tricks to achieve remote code execution (RCE) this week on a handy Twitter thread sparked by @Rhynorater.
@Rhynorater – aka security bod Justin Gardner – listed a number of common ways to achieve RCE and asked others for their input.
It was widely shared and contains useful advice, as well as success stories from researchers across the globe.