New hacking technique allows threat actors to evade some of the most effective phishing countermeasures

A new way of carrying out phishing attacks is being adopted by criminal groups – and it could make threat actors virtually undetectable, security researchers warn.
The technique involves using ‘reverse tunnel’ services and URL shorteners to launch large-scale phishing attacks. What’s more, the groups using these techniques leave no trace.
Instead, threat actors can use their local machines to host phishing pages on random URLs. These can help evade detection by URL scanning services. The groups can then further mask their identities using URL shortener services.
Down the hole
The attackers are not exploiting a vulnerability in the technical sense. Instead, they are misusing off-the-shelf, legitimate services to bypass anti-phishing measures. Services associated with the technique include bit.ly, Ngrok, and Cloudflare’s Argo Tunnel.
The attack was detected by security researchers at CloudSEK, who found that the method was being used to target customers of Indian banks.
Here, phishing attacks were attempting to dupe customers into handing over their banking details, Aadhaar (Indian national identity) number, and other sensitive information.
CATCH UP Apple showcases next-gen security tech at WWDC 2022
“We discovered it when we were monitoring the internet for our client-related assets, impersonations, and data,” Darshit Ashara, principal threat researcher at CloudSEK, told The Daily Swig.
“During the regular course of our research, we started noticing patterns of such abuse of multiple reverse tunnel services.”
Although CloudSEK detected phishing attempts against Indian bank clients, the technique has also been used in the US, the UK, and Europe.
“Reverse tunnel attacks have become quite common these days,” Ashara added. “The modus operandi of threat actors using reverse tunneling includes sending SMS-based spam with phishing URLs shortened using popular URL shortening services.
“We have observed this technique being used to target most major brands and organizations.”
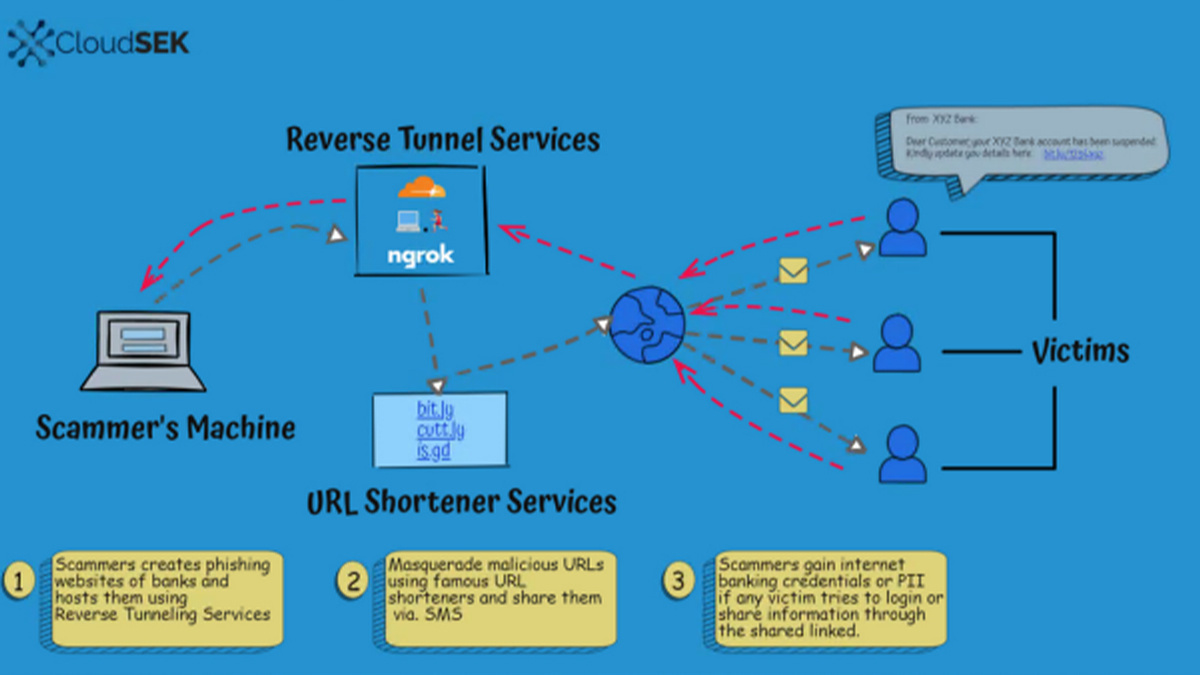 The reverse tunneling and URL shortening attack in action (Image: CloudSEK)
The reverse tunneling and URL shortening attack in action (Image: CloudSEK)
Hiding in the shadows
Reverse tunnels allows criminal groups to evade some of the most effective countermeasures.
One way phishing groups are caught is through their reliance on hosting providers, and their use of domains that, CloudSEK says, “impersonate targeted companies or keywords”.
Even where there is not enough evidence for law enforcement to go after the phishing groups, hosting providers will take down the spoof domains.
Read more of the latest infosec research from around the world
Using domains with “random or generic” keywords provides some protection for the attackers, as they cannot be reported for brand infringement. But cybercriminals are able to use reverse tunnels to bypass hosting completely by storing the phishing binaries on nothing more than a local PC.
Adding URL shortening on top makes it even harder to trace the attack and can make victims more likely to fall for the scams. Add to this the fact that most reverse tunnel URLs are temporary – typically operating for just 24 hours – and attribution and prosecution becomes far harder still.
Improved monitoring
CloudSEK is calling for improved monitoring of reverse tunnel services. Ngrok, for example, now requires its users to disclose their IP addresses, and to register before hosting HTML content, while Cloudflare requires users to create an account.
URL shortening is harder to police, as there is no actual malicious activity: they simply point users to a website. CloudSEK concedes, though, that discovering attacks depends on third-party monitoring.
Targeted firms may, then, have to rely on user education to tackle this attack vector.
“Effectively, this is another channel for phishing attacks – the key difference is attribution,” said Chris Preece, head of cyber operations at digital risk management consultancy Protection Group International.
“If a domain is registered with a hosting provider, they can respond to complaints and take down a website, but with reverse tunnels, the reverse tunnel provider has no accountability for that, which means it’s potentially harder to take down. Combine that with a URL shortener, it can be very effective.
“It’s going to sound clichéd, but the advice we have is to double down on phishing awareness to lessen the likelihood of someone clicking on a malicious link.”
YOU MIGHT ALSO LIKE Chinese cyber threat actors are widely abusing well-known attacks to infiltrate networks






