Researchers pull focus on image transfer protocol used by DSLR cameras

Security vulnerabilities that left a popular line of Canon digital cameras open to ransomware attacks may also impact other camera brands, new research reveals.
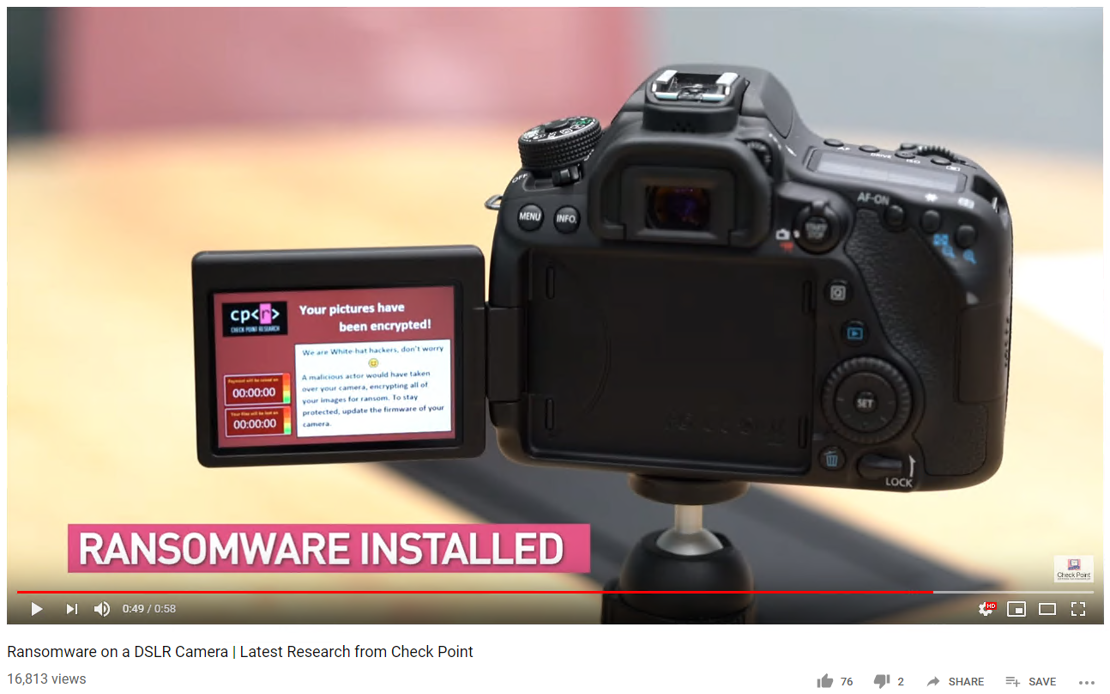
Israeli security firm Check Point caught news headlines around the world this week, as the company demonstrated how the Canon EOS 80D digital single-lens reflex (DSLR) camera had been susceptible to a ransomware exploit that could encrypt all images and render the device unusable.
In a technical blog post published on Sunday, Check Point researcher Eyal Itkin explained how the (now-patched) vulnerabilities in the WiFi-enabled camera were due, in part, to shortcomings in Canon’s implementation of the Picture Transfer Protocol (PTP).
“Simulating attackers, we want[ed] to find implementation vulnerabilities in the protocol, hoping to leverage them in order to take over the camera,” Itkin said, explaining how these flaws could be leveraged to hijack the camera via a rogue WiFi point.
“Such a remote code execution (RCE) scenario will allow attackers to do whatever they want with the camera, and infecting it with ransomware is only one of many options.”
Speaking on the sidelines of Black Hat 2019 last week, Itkin told The Daily Swig that the Canon EOS 80D was simply used as a test case, due to the company’s large market share and the camera’s dual USB and WiFi capabilities.
“We worked closely with Canon, as part of responsible disclosure,” the researcher said. “They fixed all of the vulnerabilities in this specific model and are working on fixing other models as well.”
Importantly, however, while Canon has addressed the flaws in the EOS 80D, Itkin said the PTP vulnerabilities may impact WiFi-connected DSLR cameras from other manufacturers.
“The protocol itself is quite complex,” he said. “We do believe that similar vulnerabilities could be found in cameras by other vendors.”
According to documentation from the Society for Imaging Science and Technology, PTP is a “widely supported” protocol for transferring images from digital cameras to other devices.
“Since its standardization in 2000, PTP has been widely implemented in digital imaging products, such as digital cameras, and personal computer operating systems,” the organization states.
While PTP was developed to enable photographers to transfer their images to other devices, Itkin said more work is needed to ensure the protocol is implemented in a secure manner.
“We want to raise awareness for this specific protocol,” he said. “It should contain some encryption or authentication. Today, you just connect to the camera and that’s it.
“Our research shows that any ‘smart’ device, in our case a DSLR camera, is susceptible to attacks. The combination of price, sensitive contents, and widespread consumer audience makes cameras a lucrative target for attackers.”
RELATED Ancient technique tears a hole through modern web stacks at Black Hat 2019