Nightwatch becomes first security team to reap rewards of Google Play bug bounty
Duolingo, the company behind the world’s most downloaded education app, has patched a vulnerability in its flashcard learning tool, Tinycards, after researchers found it could be injected with malicious content by a man-in-the-middle attacker.
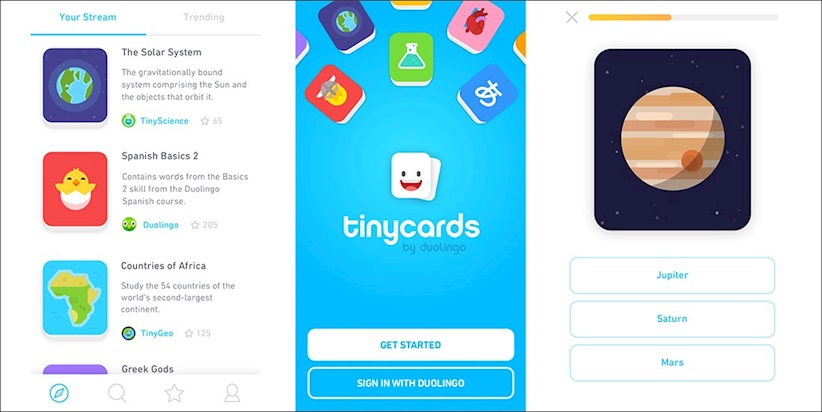
Launched as an iOS-only app in 2016, Tinycards gamifies the learning process by presenting users with hundreds of illustrated flashcard decks covering a range of subjects, from languages and biology to ideal wine pairings and Game of Thrones characters.
The free-to-download app landed on the Google Play Store back in August, and while the rollout was welcomed by knowledge-hungry Android users around the world, security researchers at Nightwatch Cybersecurity were quick to identify a flaw that left the app exposed to remote code execution (RCE).
“While monitoring network traffic of a test device running Android, we observed that during application startup an initial HTTP call is made to a non-HTTPS site, which then redirects to an HTTPS version,” the researchers explained.
“Further research revealed that the application is essentially a thin browser wrapper using Android’s WebView around a web application loaded remotely.”
According to Nightwatch, because the initial call is performed without HTTPS, it is possible for a man-in-the-middle attacker to intercept this traffic and inject their own content.
“Since this is a web app, this can result in RCE within the application since all the content is web-based,” they said.
After being alerted to the vulnerability in October, Duolingo changed the initial URL for web content being loaded within the Tinycards app to use SSL.
“The vendor has fixed this issue in v1.0 that was released via the Google Play Store on November 20, 2017, and users should install the latest version,” Nightwatch said.
Although Duolingo does not offer bug bounties, the company’s Android apps now fall under the new Google Play Security Reward Program, which was launched in October.
After flagging the Tinycards vulnerability, Nightwatch has become the first security team to receive a bounty under the initiative, with the researchers netting $1,000.
Google has previously stated that additional apps may be brought into its Play Store Security Program over time.
Indeed, it seems the tech giant would do well to follow through with its own suggestions, as the inclusion of Duolingo and its associated properties into the bug bounty initiative led to the discovery of a flaw that might otherwise have flown under the radar.
“We tested Tinycards because of the Google Play Security Reward program,” a Nightwatch spokesperson told The Daily Swig.






