The Daily Swig examines how the credit broker has recovered from its massive 2017 data breach

More than a year has passed since a security breach at Equifax saw around 145.5 million people’s data compromised by the credit broking service.
On September 7, 2017, Equifax announced that an unknown party had hacked into its servers, making off with sensitive data and financial information.
Names, social security numbers, birth dates, addresses, driver’s licenses, and credit card numbers were taken in what has been regarded as one of the biggest data breaches in corporate history.
Though it was reported in September, it later transpired that the security breach actually happened in mid-May and wasn’t spotted until July 29.
In the time since, Equifax has stepped up to prove it takes cybersecurity seriously, by hiring and firing staff, investing in security tools and training, and making a number of groveling statements.
But for its victims, the financial implications and risk of fraud could last a lifetime.
The Daily Swig consulted a number of experts in the cybersecurity and financial fields to examine what happened, what has been learned, and how big an impact this costly breach really made.
What went wrong
There were undeniably a number of failures on Equifax’s part, which the company later blamed on one IT employee.
On March 8, the US Computer Emergency Readiness Team (US-CERT) issued a warning about a vulnerability in Apache Struts, urging all users to patch their systems.
An outdated email list, however, meant that not everyone who needed to see the alert did so – as a result, not all of Equifax’s servers were patched.
The hackers later exploited the same vulnerability within the company’s dispute portal to gain access.
In another faux pas, the malicious actors were able to send 9,000 unauthorized queries to Equifax databases without being detected by security staff.
Equifax also wrongly estimated the number of people impacted.
It first reported that 143 million users’ details were compromised, later admitting that the figure was around 145.5 million – close to almost half of the US population.
How Equifax reacted
When Equifax finally did react, two months late, it made a number of key changes to its structure.
Firstly, CEO Rick Smith left the company in late September to be replaced by interim CEO Paulino do Rego Barros Jr.
It also fired chief information officer Jun Ying before he was charged by the Securities and Exchange Commission for insider trading, after allegedly selling his company shares in the time between finding out about the breach and the news being made public.
Equifax as also signed a customer “consent deal” with the banking regulators of eight US states, avoiding huge fines by doing so.
How others reacted
Shortly after the hack was announced, US Senator Elizabeth Warren launched an investigation into the scandal.
In March, she released a scathing report on her findings, warning that Equifax wasn’t being honest with its customers.
She also recommended a bill was introduced to impose penalties on companies who have breached information.
Senator Warren wrote: “Equifax can't be trusted. Their mistakes allowed the breach to happen, their response has been a failure, and they still can't level with the public.
“Enough is enough. We have to start holding the credit reporting industry accountable.”
Last week on the anniversary of the event, Senator Warren released an updated review which can be read here.
Since the March report, Equifax has hired a new head of computer security in a move to prevent further breaches.
In July 2018, Jamil Farschi joined Equifax as its new CISO and has so far impressed with his plan to integrate a more robust security practice among all levels.
Trend Micro’s Mark Nunnikhoven told The Daily Swig: “Mr Farschi has an excellent reputation and has set out to improve the security culture at the company. This combined with the consent decree signed with several states, should mean that the company will continue to improve its security posture.”
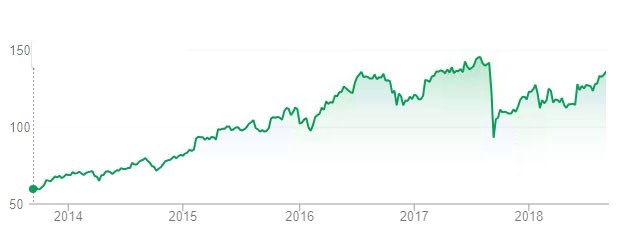
He added: “From the outside, Equifax seems to have recovered. The stock has steadily climbed after an initial hit and is trading near the same level as it was before the breach.
“Beyond the executive turn over due to the breach, it appears to be business as usual for the company.”
Recovery
Indeed, by looking at Equifax’s share prices it could be argued that last year’s incident did little to affect its reputation.
Days after the security breach was announced, shares plummeted to 92.98 – a full 47.72 down from the share price of 140.70 on September 1.
But on September 7 this year, Equifax boasted a share price of 135.91 – almost fully recovering and cementing its position back in the New York Stock Exchange.
Jim Reilly, founder of Stonepine Advisors, told The Daily Swig: “Equifax has only had its business impacted slightly by the breach. Their July earnings were pretty strong and the path their stock has taken has mirrored the overall Nasdaq market since the breach.
“Investors, quite frankly, seem to have forgotten about the breach. Strong market + strong earnings = stock price rebound.”
Reilly cited the recovery of US retail chain Target, which breached 41 million customers’ details in 2013, as another huge company whose reputation has remained intact.
He added: “The real question investors focus on is, “What is the business impact?” In the periods after Target and Equifax, there don't seem to be lasting negative impacts.”
What can be done
Worldwide, data protection laws and reporting guidelines such as Europe’s recently-implemented GDPR are ensuring that organizations that practice poor security are held to account.
But in the US, where Equifax is based, legislation to protect personal information proves a little trickier.
Of course, any company – European or not – that processes the data of an EU-based customer is held accountable to GDPR.
But for customers in the US, while there are some privacy protection bills, there is no over-arching federal bill that punishes companies in the event of a data breach.
Some US states have implemented cybersecurity regulations, especially in the financial industry.
But for some firms – especially SMEs or start-ups – the cost of staying compliant to these rules is sometimes too high.
Jessica Robinson is CEO of Purepoint International, a New York-based cybersecurity firm that works with companies to prevent data breaches.
Robinson told The Daily Swig: “There is a new cybersecurity regulation in New York, for example, which is the most rigorous in the United States. It is comprehensive, but still leaves a lot of room for ambiguity.
“Other states are implementing these regulations as well. There is a new regulation in South Carolina regarding data security and Rhode Island, Colorado, and California's new Data Privacy regulations are not far behind.
“When you combine this with GDPR, it can be quite challenging for an organization to respond quickly especially depending on the size of the company.
“Organizations that are compliant to these regulations may not have an adequate budget to meet the full requirement.”
Billion-dollar enterprise Equifax, says Robinson, was not subject to these kind of challenges – its choice not to patch systems did not come from a lack of funds.
She added: “Now in the case of Equifax, they are a large robust enterprise. As a publicly traded company, they are a $3.4 billion organization.
“They have more than enough financial resources to meet their security requirements. Storing and transmitting that type of data – SSN, birthdays, addresses, credit card numbers – it’s not an option for them to stay up to date, it’s an expectation.
“There is no ambiguity regarding what the expectations are for them from a security perspective.”
What’s next?
In a statement sent by Equifax to The Daily Swig, a spokesperson said that protecting the data entrusted to Equifax is their “number one priority”.
The company highlighted the investment it has made in cybersecurity this year and said it has been conducting regular briefings to update customers on the “lessons learned”.
A spokesperson added: “In the past year we have undertaken a host of security, operational, and technological improvements, including hardening our data security perimeter to dramatically improve detection and response rates, and strengthening our data security protocols and controls.
“In fact, in 2018 alone, we will increase our investment in security and technology by more than $200 million.
“We recognize that cybersecurity impacts not just us, but the entire industry.”






