Cybercrooks are still showing love for leaked NSA code

The widespread disruption to systems during the opening ceremony of the PyeongChang Winter Olympics was caused by malicious actors leveraging the Eternal Romance exploit, security researchers have confirmed.
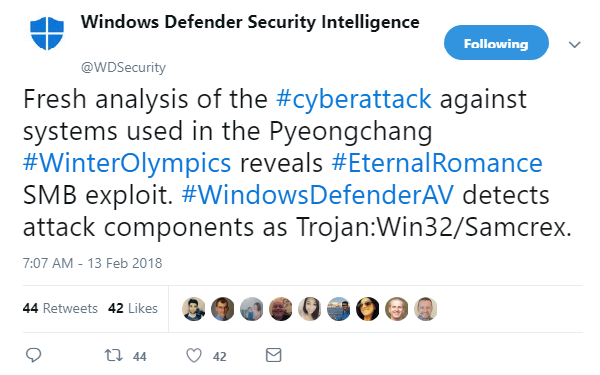
Issuing a statement this morning, the Windows Defender Security Intelligence team said their analysis of the Winter Olympics cyber-attack – which crippled on-site WiFi and internet access during the opening ceremony and also forced the official PyeongChang 2018 website offline – revealed the Eternal Romance Server Message Block (SMB) exploit was to blame.
Although officials have refused to confirm the source of the hack, Matthieu Suiche, founder of cybersecurity firm Comae Technologies, said the use of Eternal Romance demonstrates that last year’s leaked National Security Agency (NSA) exploits are “still being repackaged by malicious actors”.
Eternal Romance bypasses security over Microsoft’s SMB file-sharing connections, enabling remote execution of instructions on Windows clients and servers.
The exploit, along with Eternal Blue and Eternal Champion, was purportedly developed by the NSA’s secretive Tailored Access Operations (TAO) unit before being leaked by the Shadow Brokers hacking group last year.Since their release, the NSA exploits have been linked to numerous high-profile cyber-attacks, including Bad Rabbit, NotPetya, and WannaCry.
While Microsoft’s latest announcement shines some light on the workings of the Winter Olympics systems hack, Paul Johnston, researcher at PortSwigger Web Security, said the discovery of Eternal Romance raises as many questions as it does answers.
“The NSA malware, while often implicated in lateral escalation, isn’t normally suitable for an initial compromise, as SMB is typically blocked by firewalls,” Johnston said. “This leaves unanswered the question of how hackers initially penetrated the firewall.”