The vulnerability has since been fixed
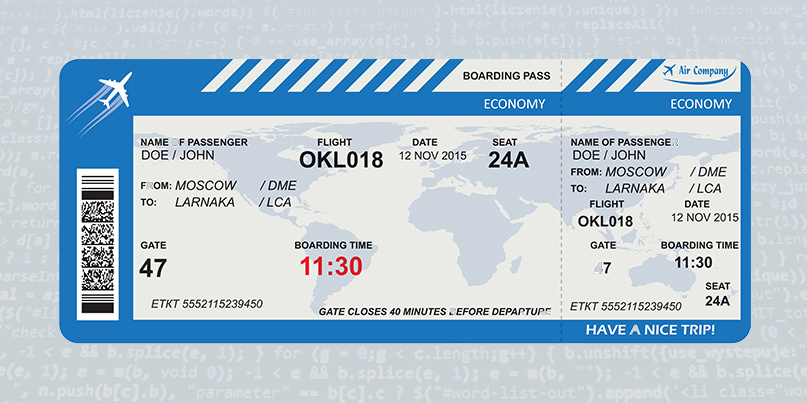
A security vulnerability in a flight check-in application made it possible to download the boarding passes of other airline passengers until the issue was resolved earlier this week.
The problem – discovered by David Stubley, a security researcher at 7 Elements – arose from an Insecure Direct Object Reference weakness within an application maintained by Amadeus, a company providing IT services for the airline industry.
Insecure Direct Object Reference (IDOR) vulnerabilities happen when an application provides direct access to objects based on user-supplied input, bypassing authentication and user access controls in the process.
Exploitation in this case involved first intercepting a request to generate a boarding pass, prior to changing to the ID parameter in order to access a boarding pass not associated with the user.
The security flaw was patched by Amadeus less than a week after Stubley flagged the problem, which he reported to the company via airline operator Flybe on July 8.
An example of a link to a boarding pass not belonging to the user can be found in Stubley’s advisory.
The Daily Swig has approached Amadeus for comment.






