Account takeover issue flagged through bug bounty platform’s own bug bounty program

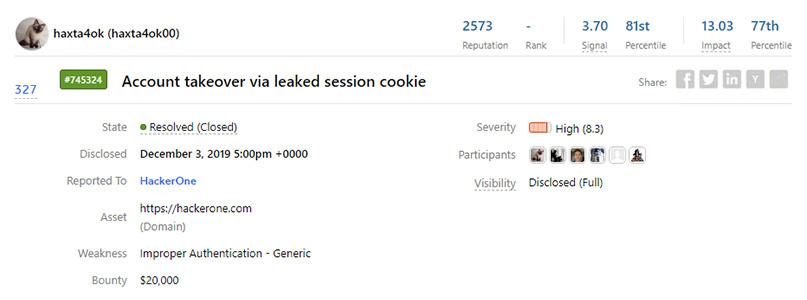
Bug bounty platform HackerOne this week paid out a $20,000 bounty after a researcher was able to access other users’ vulnerability reports.
Haxta4ok00, a HackerOne community member who apparently has a track record of discovering vulnerabilities in the bug bounty platform, was engaged in a conversation with one of HackerOne’s security analysts.
In one message, the analyst copied a cURL command from a browser console and sent it to the hacker.
The analyst accidentally included a valid session cookie that gave the ability to read the data that they had access to. This included report titles, a certain amount of metadata, and some report contents.
“Less than five per cent of HackerOne programs were impacted, and within two hours of receiving the vulnerability report, the risk was eliminated and additional preventative measures were deployed shortly after,” a HackerOne spokesperson tells The Daily Swig.
“All customers impacted were notified the same day.”
However, it took HackerOne two hours to read the report, thanks to lower staffing levels over the weekend.
The $20,000 cookie
Haxta4ok00 reported the vulnerability, which was treated as ‘critical’, on November 24. The bounty was awarded three days later.
“The team looked into the amount of sensitive information that could have been accessed by the account and took that under advisement when deciding on the bounty amount,” HackerOne explains in its incident report.
“This led to the decision to treat the submission as a critical vulnerability and award a $20,000 bounty.”
HackerOne says it’s carried out an audit, and that this is the first time that session cookies have been leaked.
It’s also released an update that limits HackerOne employees and HackerOne security analyst sessions to the IP address that they started the session with – a move that should prevent similar incidents in future.
Read more of the latest bug bounty news from The Daily Swig
“We’re also planning to roll out a number of smaller changes, such as warning the user when a comment seems to contain sensitive information and clarification in our policy about what to do when someone gains access to other people their account,” explains HackerOne co-founder Jobert Abma.
Craig Young, senior security researcher at Tripwire, was one of those to be informed that their reports had been disclosed.
“While I commend HackerOne for their response, this incident is yet another reminder of a distinct risk organizations take by using managed vulnerability reporting services like Bugcrowd or HackerOne,” he says.
“The consolidation of valuable data by such vendors creates a hugely attractive attack target for intelligence agencies – or even criminal actors – to fill their arsenal.”
Though perhaps better known for facilitating bug bounty payouts on behalf of other organizations, HackerOne is no stranger to the vulnerability disclosure process.
Since going live in November 2013, the organization has awarded more than $330,000 in bounties through its own bug bounty program.
READ MORE Bug Bounty Radar // November 2019