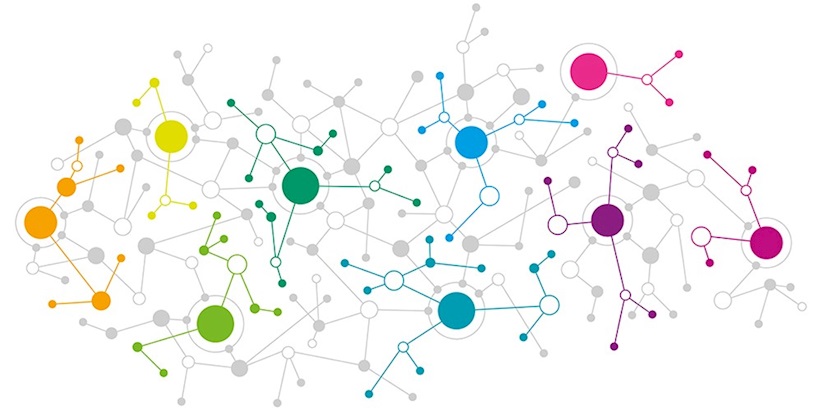
Advanced network architecture utilizes custom-built P2P communication
A new botnet that uses custom-built peer-to-peer (P2P) communication to exploit IoT devices and develop its infrastructure is growing rapidly around the world, researchers have discovered.
The bot – dubbed ‘Hide ‘N Seek’ – was first spotted by Bitdefender on January 10. After fading away in the following days, the botnet reemerged on January 20 in a “significantly improved form”.
According to Bitdefender’s Bogdan Botezatu, the botnet communicates in a complex and decentralized manner and uses multiple anti-tampering techniques to prevent a third party from hijacking or poisoning it.
“The bot can perform web exploitation against a series of devices via the same exploit as Reaper,” said Botezatu. “[It] embeds a plurality of commands such as data exfiltration, code execution and interference with a device’s operation.
The samples identified in the researchers’ honeypot systems on January 10 revolved around IP cameras manufactured by a Korean company.
“These devices seemed to play a major role in the botnet as, out of the 12 IP addresses hardcoded in the sample, 10 used to belong to Focus H&S devices,” Botezatu said. “The new version, observed on January 20, dropped the hardcoded IPs.”
By January 24, Hide ‘N Seek had taken control of 18,000 devices. However, as of 11:00am today, this figure had grown to 32,000.
Fortunately, like other IoT botnets, Hide ‘N Seek cannot achieve persistence, and a reboot brings compromised devices back to their clean state.
“It is the second known IoT botnet to date, after the notorious Hajime botnet, that has a decentralized, peer-to-peer architecture,” said Botezatu.
“However, if in the case of Hajime, the P2P functionality was based on the BitTorrent protocol, here we have a custom-built P2P communication mechanism.”






