Age-old font-manipulation technique being used to bypass Office 365 security scans
A crafty but dated technique is being leveraged once again to successfully bypass Microsoft phishing scanners and deploy attacks on unsuspecting victims.
Microsoft Office 365 uses natural language processing scans to identify fake or fraudulent emails and alert the receiver.
It identifies phishing emails by searching for signs of impersonation – for example, if an email contains the sign-off ‘Microsoft Corporation’, but hasn’t come from the company.
Malicious actors have now found a way to get around this issue, by using an old attack that was previously used to bypass spam filters.
The attack was recently coined ‘ZeroFont’ by security research team Avanan, who wrote a blog post about the method.
ZeroFont involves inserting hidden words and letters into an email which can trick Microsoft, and are also invisible to the reader.
For example, an attacker can insert random words into a sentence and in the HTML code, set the font size to zero – meaning the words won’t be visible within the email.
But because Microsoft scans the plain text regardless of font size, these words and letters can trick the scanner.
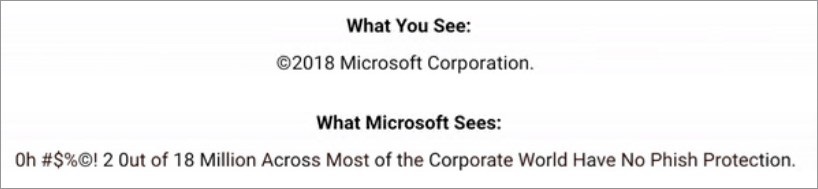
So while the end user reads: ‘Microsoft Corporation’, Outlook’s scanners see a different text, such as: ‘Microantsotreeft Cocatrporatabletion’.
Of course, for this phishing technique to be successful in exploiting the end user, the link or attachment would have to be clicked or downloaded.
But the simplicity of the attack does raise concern about whether natural language processing is enough to block phishing scams from reaching their victims.
The post read: “Natural language processing is a vital and powerful tool in the prevention of email phishing attacks.
“The ZeroFont method is just one way that attackers use to present one email to the security filters and another to the user.”






