Manufacturer complacency ‘translates into an unacceptable risk for consumers’, warns security expert
IoT vendors are making slow progress in making it easy for security researchers to report security bugs, with only 27.1% of suppliers offering a vulnerability disclosure policy.
The figure, based on the latest annual report from the IoT Security Foundation (IoTSF), compares to the 9.7% of IoT (Internet of Things) vendors that were reported to have a disclosure policy in the 2018 edition of the same study.
BACKGROUND IoT Security Foundation launches vulnerability disclosure platform for smart device vendors
Vulnerability management ought to be a cornerstone of connected product security, widely recommended in 30 cybersecurity guidance initiatives including the IoTSF’s IoT Security Assurance Framework.
Straightforward reporting of security issues is essential for security lifecycle maintenance, and vendors risk falling foul of newly enacted UK regulations if they ignore best practice mandates.
The UK’s Product Security and Telecoms Infrastructure – which became law in early December 2022 – requires that IoT manufacturers, importers, and distributors offer a vulnerability disclosure policy, with suppliers who breach this risking potential sanctions including penalties of up to £20,000 per day in the most severe cases.
Catch up on the latest vulnerability disclosure policy news
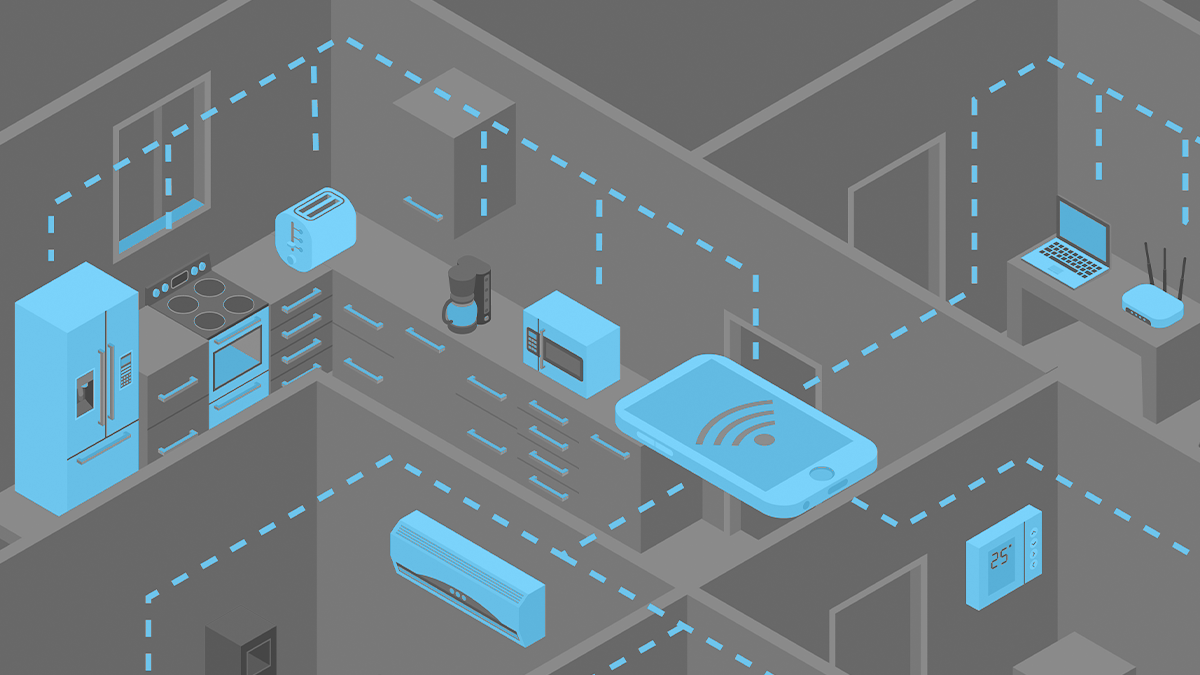
The IoTSF’s latest study was based on a review of practice of 332 companies who sell consumer-focused IoT products. The review, carried out by mobile and IoT security consultancy Copper Horse, covered security practices tied to a range of products ranging from tablets and routers to smart home lighting controls and smart speakers.
Vendors from Asia tended to be better at establishing vulnerability disclosure programs, with European suppliers trailing significantly behind (34.7% versus 14.5%, respectively).
Laurie Mercer, senior manager of security engineering at HackerOne, said: “Knowing about security vulnerabilities within products and services through a Vulnerability Disclosure Policy (VDP) is an important way to identify and rectify them as part of the product security lifecycle.
“It’s a best practice that customers are increasingly looking for their supplier to adopt, but this research suggests it is not yet common practice.”
Increased regulation
Lawmakers across the world are looking to introduce regulations in order to push IoT vendors into making their products more secure. For example in the US lawmakers have established the IoT Cybersecurity Improvement Act (2020).
The draft European Cyber Resilience Act covers similar ground.
David Rogers, CEO of Copper Horse, told The Daily Swig: “The trend is towards mandating it – which makes you wonder again, why aren’t companies realising this? The writing is on the wall!”
Rogers added: “Even with the threat of incoming legislation, there is complacency in manufacturers that translates into an unacceptable risk for consumers when it comes to the security of IoT devices.”
During the study, researchers identified increases in the use of the ‘/security’ contact page, the use of machine-readable ‘secuity.txt’ files and a small decline in PGP key usage for secure submissions.
Other trends uncovered were an increase in the number of vendors that updated their policies and a rise in the number of companies using a third-party ‘proxy service’ to host and maintain their policies.
Best practice
It’s not all doom and gloom, however, as the report did highlight examples of good practice by some vendors.
Rogers explained: “Some companies and industries are starting to act in a much better way – there are some examples in the car industry such as Volkswagen Group where they have completely transformed their approach, in a positive way.
“I think these companies can set a good example to their peers in showing that you can work with the security research community without all the brinksmanship.”
Vendors would do well to have a safe harbor policy, a legal framework that allows ethical hackers to look for flaws in systems with risking legal threats or potential prosecution. LG, for example, operates a safe harbor policy for its IoT products.
Looking more broadly, the IoTSF report commends 34 vendors that “meet or exceed what will be required by legislation” based on a review of their policies by security researchers from Copper Horse. Firms listed include Bosch, BT, Canon, Huawei, LG, Logitech, Microsoft, Peloton, Samsung, and Wink.
YOU MAY ALSO LIKE WAGO fixes config export flaw threatening data leak from industrial devices






