XSS to RCE made easy
Akamai’s Daniel Abeles today walked Black Hat attendees through version 2.0 of JSShell – a free-to-install web tool that aims to make XSS-to-RCE exploitation easier than ever.
JSShell is an interactive multi-user web-based JavaScript shell that was initially created in order to debug esoteric browsers during experiments and research.
The tool can also be attached to a cross-site scripting (XSS) payload to achieve browser remote code execution (RCE), similar to the Browser Exploitation Framework (BeEF) project.
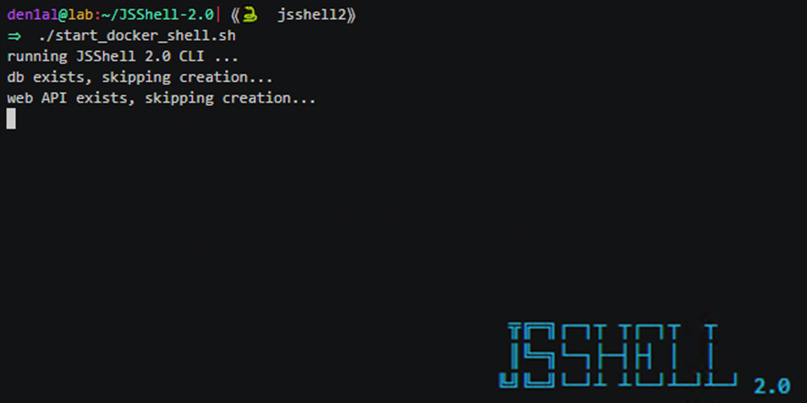
Launched in December last year, version 2.0 of JSShell has been created entirely from scratch, bringing new features and improved stability.
“Version 2.0 was officially released late December 2018,” Abeles, a senior security researcher at Akamai, told The Daily Swig ahead of his Black Hat Arsenal presentation.
“It introduced a couple of exciting features: First, I rewrote the entire framework from scratch. Now the shell component itself is written with pluggability in mind, offering users [the ability] to write their own plugins and implement them easily into the framework.
“Even the library that I’m using for the shell component has stated JSShell to be one of the open source projects using the library.”
Abeles added: “Furthermore, JSShell now offers deployment through Docker, making the [setup] a breeze, even for beginners.”
TLS for XSS
In addition to these new features, Abeles said JSShell now offers one of the most requested upgrades: TLS support.
“This feature was crucial to many users, since most of the websites won’t allow [you] to load scripts over HTTP if the origin is loaded over HTTPS,” he explained.
“There are a couple of new exciting features that are being developed as we speak, hopefully to be released in the next couple of months.”
“Currently, I’m planning to develop a web interface that could complement the command-line interface.”
“Besides that, I’m looking into adding more ways to send the data, like web sockets communication, and generally adding more options to the framework.”
Those interested in learning more about the tool should check out the JSShell GitHub repo and accompanying tutorial video.






