Eight people face charges for their alleged role in global cybercrime operation
Collaboration between cybersecurity firms, tech organizations, and law enforcement has resulted in the take-down of a major ad fraud operation.
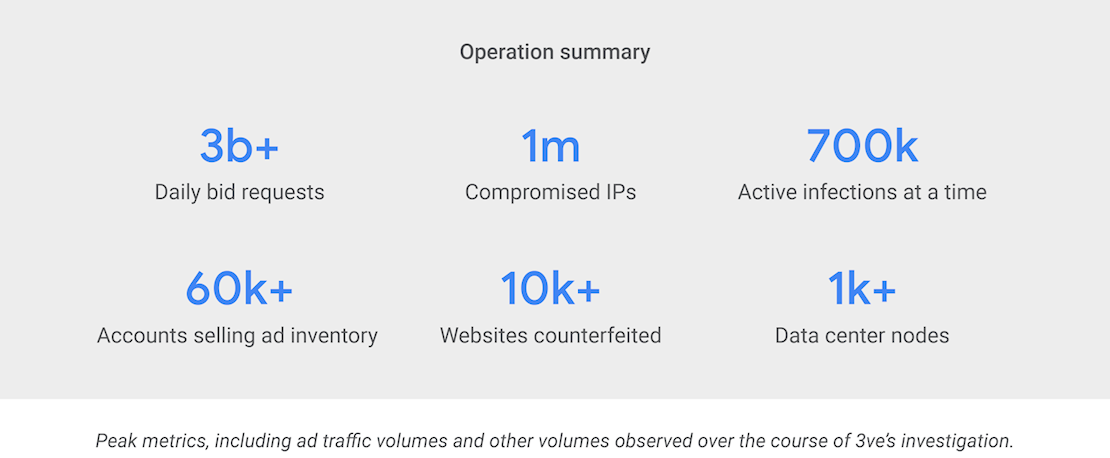
At its peak, the cybercrime network known by the US government as ‘3ve’ had control of more than 1.7 million unique IPs, as it abused devices that had been infected with Boaxxe and Kovter malware, as well as BGP-hijacked IP addresses.
The complex and ever-changing network of bots underpinned a massive ad fraud operation involving 10,000 counterfeit websites and up to 12 billion requests per day to generate fake ad views and clicks, defrauding legitimate advertisers in the process.
Kovter and Boaxxe
Providing an overview of the operation in a recent technical alert, US-CERT explained how 3ve directed vast amounts of internet traffic towards ads they controlled in order to reap the rewards of fraudulently obtained digital ad revenues.
Kovter malware is spread through email attachments and drive-by downloads. The ad scam worked by running hidden Chromium Embedded Framework (CEF) browser on the infected machine.
“A C2 server tells the infected machine to visit counterfeit websites,” said the CERT. “When the counterfeit webpage is loaded in the hidden browser, requests are made for ads to be placed on these counterfeit pages. The infected machine receives the ads and loads them into the hidden browser.”
While Boaxxe malware also spread through email attachments and drive-by downloads, the ad fraud scheme that utilizes the botnet is primarily powered from a data center.
“Hundreds of machines in this data center are browsing to counterfeit websites,” US-CERT explained. “When these counterfeit webpages are loaded into a browser, requests are made for ads to be placed on these pages.
“The machines in the data center use the Boaxxe botnet as a proxy to make requests for these ads. A command and control (C2) server sends instructions to the infected botnet computers to make the ad requests in an effort to hide their true data center IPs.”
Servers and sinkholes
The campaign to cripple the 3ve network was spearheaded by New York-based cybersecurity firm White Ops, which worked in collaboration with nearly 20 prominent ad tech and security organizations, including Google, ESET, Malwarebytes, F-Secure, Oath, Facebook, and F-Secure.
Yesterday, the US Attorney’s Office for the Eastern District of New York announced the global zombie network had been shut down, as the FBI seized control of 31 internet domains and 89 servers that formed part of the botnets’ infrastructure.
Eight individuals (seven Russian nationals and one Kazakh national) have been indicted for causing “tens of millions of dollars” in losses from digital advertising fraud. Three have been arrested in various jurisdictions, where they remain the target of extradition proceedings.
The remaining defendants remain at large.
“As alleged in court filings, the defendants in this case used sophisticated computer programming and infrastructure around the world to exploit the digital advertising industry through fraud,” said Richard Donoghue, US Attorney for the Eastern District of New York.
“This case sends a powerful message that this Office, together with our law enforcement partners, will use all our available resources to target and dismantle these costly schemes and bring their perpetrators to justice, wherever they are.”
RELATED Andromeda botnet dismantled by international taskforce






