DHS intelligence analyst Charles Covel drills down into the risks posed by IoT devices and systems

It’s estimated that 50 billion Internet of Things (IoT) devices will be in operation around the world by 2020, ranging from new consumer products – such as light bulbs, televisions, and smart meters – to legacy infrastructure systems that have been in place for decades but only recently connected to the internet.
While the next generation of IoT devices are being rolled out in an effort to make our lives easier and more enjoyable, the shift towards connectivity is not without its risks – whether this is consumers having their personally identifiable information compromised or the potentially devastating damage that could be inflicted on a city’s critical infrastructure.
During a recent webcast, Charles Covel, intelligence analyst at the Department of Homeland Security’s Office of Cyber and Infrastructure Analysis (OCIA), provided an update on the burgeoning IoT market and discussed the risks these devices and systems pose to public health, the safety of the economy, and national security.
“By being connected to the internet and other devices, these physical devices now offer a new pathway for malicious actors or accidents to occur that have much broader effects than simply damaging or affecting that specific IoT device,” Covel said.
The OCIA has identified three primary groups of risks associated within the IoT: changing seams, inconsistent adoption, and increased automation. When taken together, Covel demonstrates that although the Internet of Things has marked the birth of a new technological era, today’s smart devices are also the elephant in the room when it comes to security.
Changing seams
“As more devices are connected to the internet or other systems, it becomes difficult to determine where a physical system ends and a cyber system begins.
One of the consequences and challenges with changing seams is that we are increasing the number of interdependencies and we are increasing the attack surface. Before, if I wanted to steal a vehicle I would have to physically access that vehicle.
Now, it has been shown that someone working remotely with a computer can gain access to a vehicle and potentially affect some of its systems, such as the steering or braking.
In addition, industrial control systems that may have been in place for decades are now being connected to the internet. These legacy systems were never designed to be connected.
In many cases, the objective is to make it easier for operators to use these systems and save the owners and operators money, but they are often connected without implementing all of the security safeguards that you would need to put in place if you were developing these systems from the ground up.
Whereas before, in order to access oil or natural gas SCADA system, you actually had to be physically present. And because of that, there may have been one password that 40 people would use, or potentially no passwords because you had to get through gates and go past guards in order to gain access to these systems.
Now, however, they are connected to the internet, and in some cases the operators are not putting in the safeguards such as passwords or dual-factor authentication. All of this creates new vulnerabilities.
You are also increasing the attack surface through the billions of new, unsecure devices that are being connected to the internet or other systems.
These new, unsecure technologies are being connected to critical infrastructure systems at the edges, which in some cases can potentially allow access to the critical infrastructure systems.
For example, electric power plants may be very secure, but by being able to access smart meters, there may be ways for a malicious to get into the SCADA systems.
The last way that the attack surface is increasing is that there is simply unknown communication among devices. We often do not know which devices are talking to each other. If you have a Fitbit, when you walk into a room that device is constantly sending out information and trying to get information back.
Small IoT devices tend to be cheap and, in some cases, adding cybersecurity mechanisms would actually be prohibitively costly. If you were to secure these devices, they would no longer be cost effective to manufacture, and we wouldn’t have these devices to begin with. So that’s a trade-off that both consumers and manufacturers have to consider.
IoT devices are also often designed for ease of use. I personally wouldn’t want to use a Fitbit that asked for a password or dual-factor authentication every time I wanted to see what my heart rate was. These systems are designed to be easy to use, not to be secure.”
Inconsistent adoption
“The technologies that ‘win’ will differ across cities, industries, and companies. Interoperability will critical. The technologies have to be able to communicate, or they lose much of their value.
The technologies that work in an autonomous vehicle, for example, must be able to work in all cities – not just one city or a few.
If the systems can’t talk directly to each other, translators might be needed, which introduces another attack vector. The simplest methods of connecting and talking, such as WiFi or Bluetooth, are often the most vulnerable.
There are going to be different rates of adoption among cities and individuals, which means that there’s going to be a mix of smart and dumb technologies, and this will require a complex transition period.
This isn’t necessarily a concern at the household level, but it could potentially be a significant concern at the city or company level.
There will also be varying levels of security among adoption, and this goes back to the increased attack surface. If one million people have smart meters, and all the meters are talking to each other or are communicating with a central system, it only takes one owner to fail to update their security software to create a vulnerability in the whole system.”

Increased automation
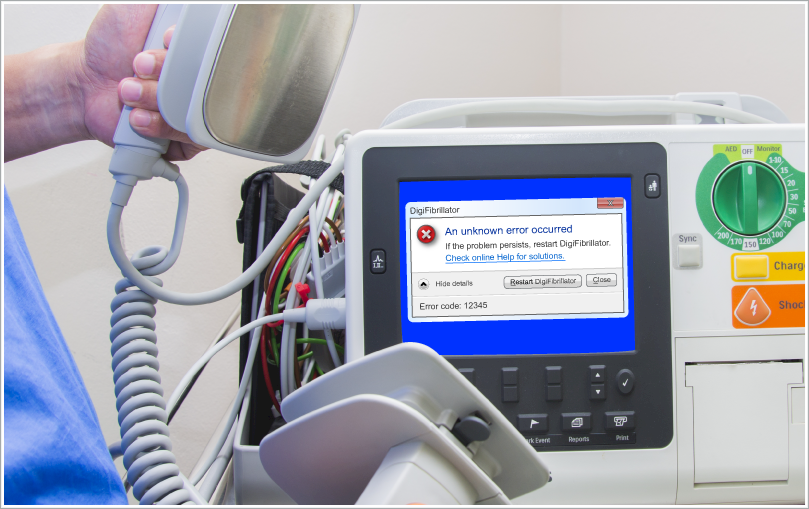
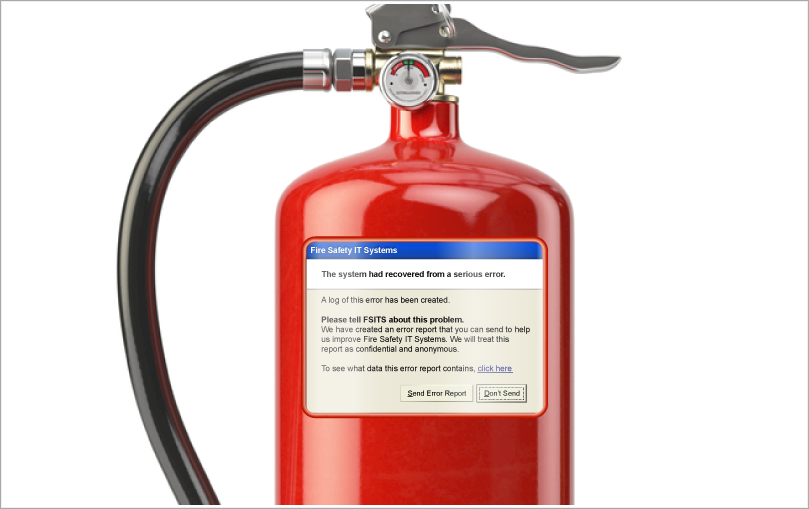
“The final overarching risk is increased automation. Skill atrophy is not just a concern for the IoT, it’s really a concern that we have seen across many emerging and evolving technologies, whether it’s artificial intelligence, robotics, or communications. Will operators still have the skills to operate physical systems in the case of a computer or internet outage?
This doesn’t need to be a malicious act. I think we’ve all experienced times when our computers are not functioning properly and we have to restart them, or we lose power and don’t have access to them anymore. Will humans still have the capability to operate these devices?
As systems become more and more automated, operators may lose the skill to operate that system because they are not regularly required to do so. There are certainly things that companies and industries can do to make sure that everybody has the training, but if you don’t use it you lose it, and that is certainly a concern.”






