Banking credentials are currently pricing at $70 to $500, depending on the ‘quality and timeliness’ of information

More than 15 billion usernames and passwords for internet services including bank, video streaming and social media accounts are offer to cybercriminals, according to new research from Digital Shadows.
The threat intel firm found that the number of stolen and exposed credentials has risen fourfold (up 300%) over the last two years, as the result of more than 100,000 separate data breaches.
Digital Shadows’ study, ‘From Exposure to Takeover’, found the number of compromised credentials in circulation across cybercriminal marketplaces, many on the dark web, represent the equivalent of more than two for every person on the planet.
Of these, more than five billion were assessed to be ‘unique’ – meaning that they have not been advertised more than once on criminal forums.
Account takeover as-a-service
Account takeover has never been easier (or cheaper) to carry out for cybercriminals. Traditional DIY approaches that rely on credential-stealing malware and phishing campaigns have been supplemented with newer services and products.
For one thing, a myriad of brute-force tools and account checkers are available on criminal marketplaces – and can be used with little technical expertise – for an average cost of just $4.
Rather than buying a compromised credential, criminals can ‘rent’ an identity for a given period, thanks to the growth of so-called account takeover as-a-service offerings from various underground markets.
These services offer fingerprint data (such as cookies or IP addresses) from a target individual – information that makes it easier to ensure that transactions go through unnoticed or otherwise abuse compromised login details.
READ MORE Europol launches financial crime unit as crooks exploit Covid-19 pandemic
Underground bazaars such as Genesis Market offer compromised account leases for starting prices of as little as $10 per account.
“Such is the popularity of these services that users on forums are desperate to acquire invite codes to this market,” Digital Shadows reports.
Alex Guirakhoo, threat research team lead at Digital Shadows, said that the coronavirus pandemic has had a mixed effect on cybercrime markets.
“Some threat actors, such as those involved in the criminal travel industry or those involved in shipping fraud, have seen their business decline,” Guirakhoo told The Daily Swig.
“On the other hand, some have taken advantage of Covid-19 and developed new fraud schemes.
“Multiple forums have had to recruit new staff members to deal with the enormous increases in activity levels,” he added.
 Digital Shadows has reported a huge increase in the number of stolen credentials being sold online
Digital Shadows has reported a huge increase in the number of stolen credentials being sold online
Trading index
Many account details are offered free of charge, but of those on sale banking and financial accounts were the most expensive, trading at an average cost of £56 ($70.91).
Depending on the quality and timeliness of information this price can be much higher, reaching upwards of £395 ($500), according to Digital Shadows.
These high-value banking and financial accounts accounted for a quarter of all the advertisements analyzed by the UK-based threat intelligence firm.
INSIGHT Web application attacks rise to account for almost half of all data breaches
Accounts for streaming and takeout services are just as popular, but with the lower-level sites. Subscriptions to VPNs and adult websites represented other popular compromised credential sale categories.
US-based accounts were advertised most frequently on criminal forums and marketplaces, followed close behind by Canada, Australia, the United Kingdom, and Germany.
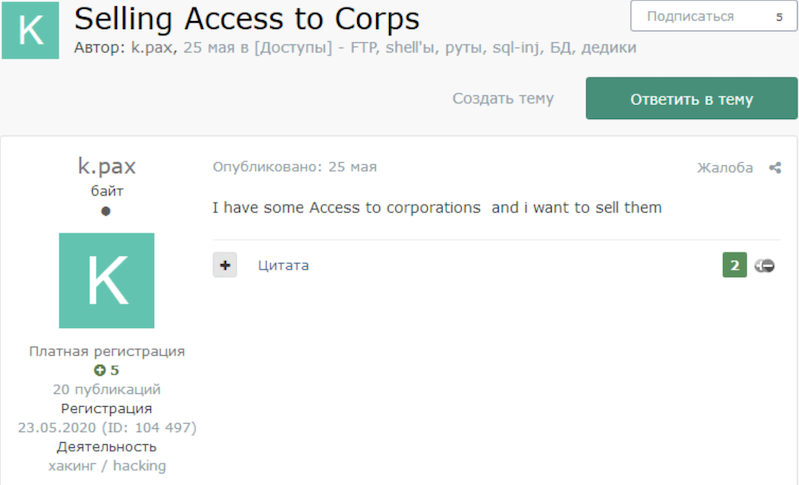
Business-related listings made up another staple of advertisement on underground forums.
Dozens of advertisements for domain admin access for prices ranging from £395 ($500) to £95,000 ($120,000).
Usernames with “invoice” or “invoices” were by far the most common advertised business credentials and made up 66% of the two million usernames assessed.
“Partners” and “payments” came in a distant second and third place, both with 10% each.
Maturing market
Commenting on the cybercrime research, Rick Holland, CISO and vice president of strategy at Digital Shadows, said: “The sheer number of credentials available is staggering.
“In just over the past 1.5 years, we’ve identified and alerted our customers to some 27 million credentials – which could directly affect them.
“Some of these exposed accounts can have (or have access to) incredibly sensitive information. Details exposed from one breach could be re-used to compromise accounts used elsewhere,” he added.
Guirakhoo told The Daily Swig that he had no expectation that the marketplace for stolen credentials would diminish anytime soon.
“The companies that fall victim to credential theft span almost every sector and geography,” he said.
“Cybercriminals appear to be realizing that no matter what type or size of company, it will hold some monetizable information (either account details themselves or data on systems that can be obtained by logging on using stolen credentials).”
YOU MIGHT ALSO LIKE Strategies for combating increased cyber threats tied to coronavirus






