Middle Eastern state recognized for continued commitment to protecting national infrastructure
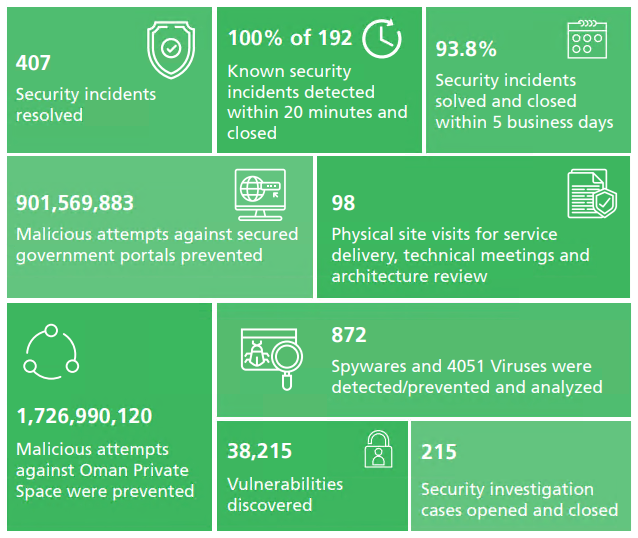
Oman continues to live up to its reputation as a regional cybersecurity heavyweight, after it was revealed that the country thwarted more than 2.6 billion malicious attempts to access its public and private systems in 2018 – at least three times as many as in 2017.
More than 900 million attacks specifically targeted government websites, according to the Information Technology Authority’s 2018 Annual Report (PDF), while 1.7 billion attacks were aimed at private organisations.
The ITA says it also prevented and analyzed 872 spyware incidents and 4,051 viruses during 2018. More than 90% of these security incidents were solved and closed within five business days, it said.
The figures reinforce the country’s strong security record, with the latest International Telecommunications Union (ITU) Global Cybersecurity Index (PDF) ranking it second in the Middle East for its commitment to protecting its national infrastructure
“The thing they are doing right is understanding risks and impacts of cyber threats at a country level and implications of the potential damage – reputational, theft, sabotage, etc – that a cyber-attack could have on Oman,” Bharat Mistry, principal security strategist at Trend Micro, told The Daily Swig.
“The biggest threats the country faces are espionage and theft of intellectual property, sabotage of critical infrastructure, and equipment that fuels the Oman economy, such as industrial control systems that are used in the oil industry. Fake news is also a high factor, as political tension among the Gulf states continues.”
Last year, Oman moved to improve the protection of its energy infrastructure by embarking on a cybersecurity audit of its industrial control systems.
Other recent initiatives from the state’s Information Security Division – which is responsible for the security of government entities – include the introduction of firewalls, real-time dashboards for global threats such as cryptocurrency mining and internet-wide scanners, and the launch of an open source, graph-based security analytics and visualization tools.
Meanwhile, the Oman Computer Emergency Readiness Team (OCERT), which analyzes risks and raises public awareness, has continued its national security campaign, organized a ‘threat hunters’ competition, and held dozens of consumer-focused education events.
Oman is also working to increase cybersecurity training. “Traditionally, in Gulf state countries where any STEM-based career is seen as a male-only profession, that [skills] gap has been significantly higher than the global average,” says Mistry.
As the Middle East has digitized, it has become more attractive to cybercriminals – and those attackers are increasingly looking to profit, says Mistry. This means they are becoming more professional.
“Traditionally, the underground marketplaces in the Middle East aren’t profit driven like Russia’s or China’s – there’s much more a culture of sharing than other regions. It’s been common practice amongst threat actors to readily hand out codes, instruction manuals, and malware for free,” he says.
“However, over the past year, the monetization of cyber-attacks has increased, and many cybercriminals are now starting to charge for their services.”






