One critic deems the move ‘a case of throwing the baby out with the bathwater’
Pastebin has scrapped an API used by researchers to track potential data breaches and hinted that there may be a new subscription model on the horizon amid heavy criticism from the security community.
The deprecation of the API was announced via Twitter on April 15. Pastebin said the service has been subject to “active abuse by third parties for commercial purposes”.
This was said to be a clear violation of the platform’s terms of service, which stipulate that users “agree not to reproduce, duplicate, copy, sell, resell or exploit any portion of the service”.
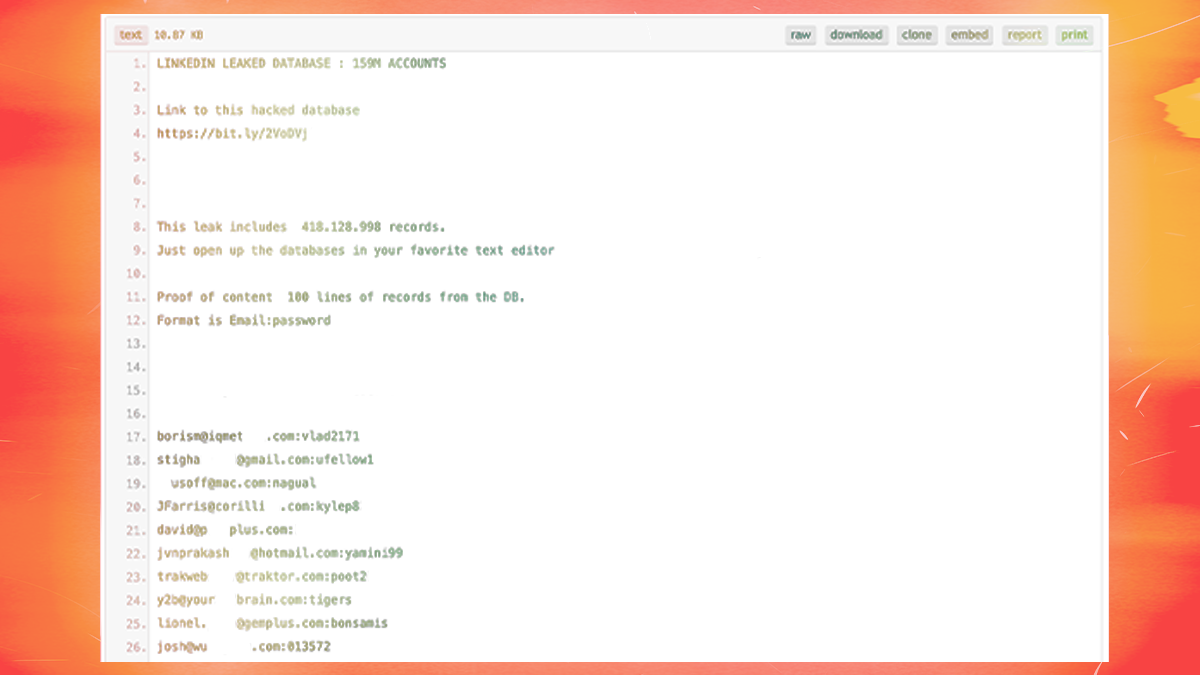
Since 2002, Pastebin has permitted anyone to upload and publish text. The platform is useful to developers but has also become a repository of unpalatable information, including stolen data, online credentials, and account record dumps pilfered by cyber-attackers.
Legitimate security teams relied on the Pastebin scraping API to stay informed of potential data breaches and to gather threat intelligence based on newly pasted content.
Companies, too, were able take advantage of the API to monitor Pastebin for any releases related to their own networks.
The tool was only available to individuals or organizations that purchased a Lifetime Pro subscription, which whitelisted user IPs to prevent them from being blocked during scrapes.
Pastebin’s terms of service used to allow researchers to scrape “public, non-personal information for research purposes”. References to scraping have since been removed.
Ctrl+C, Ctrl+V
Pastebin’s announcement was met with anger across social networks, with some users demanding a refund on their Pro subscriptions. Others expressed concern over the impact removing the API might have on the cybersecurity landscape.
It has been noted that removing the API could result in new malware campaigns going under the radar and may hamper future threat research.
“It’s understandable that Pastebin wants to curb the misuse of its API. However, removing the scraping API feels like a case of throwing the baby out with the bathwater,” Javvad Malik, KnowBe4 security awareness advocate told The Daily Swig.
“While the removal will prohibit misuse, it also takes away a legitimate security function for companies and does nothing to address attackers abusing Pastebin to host payloads.”
Anti-malware service Abuse.ch alleged that the decision was due to Pastebin platform mishandling, saying that “abuse reports became too much work for Pastebin: instead of [combating] the abuse of their platform, they simply disabled the ability to detect malicious pastes”.
Pastebin has since replied:
Security researchers are always welcome to contact us. Pastebin has [its] own security team. We have responded to your comment about abuses, and nothing has been changed on that front.
In response to such criticism and queries by Bad Packets researcher Troy Mursch, Pastebin said on April 16: “We are evaluating options and [may] develop a model for independent security researchers.”
This could indicate that researchers would need to purchase a separate subscription to access the API in the future.
API alternatives
There are alternatives to the Pastebin scraping API, with some vendors claiming to have uninterrupted access to archived and new pastes.
Tools such as Pastebin Crawler scour Pastebin archive pages and dump the results inside SQLite databases.
The Scavenger OSINT bot continues to provide potential data leak Pastebin alerts for research purposes.
Tim Mackey, principal security strategist at the Synopsys Cybersecurity Research Center, told us that Pastebin’s Developer API has stringent rate limits but maintains much of the same functionality, and therefore the decision may have been down to financing.
“Operating a popular web service is a costly proposition, and when some users dominate the resources required to reliably deliver that service, the operators are faced with hard decisions,” Mackey said.
“Presumably, Pastebin sought to control the abuse through other means but eventually concluded that any loss of business from disgruntled users was minor relative to the impact from the abusers.”
The Daily Swig has reached out to Pastebin and will update when we hear back.
READ MORE Latest web hacking tools – Q1 2020







