IBB panel will continue to reward hackers who have already submitted PHP vulnerability reports
PHP has been unceremoniously removed from the Internet Bug Bounty program – but the custodians of the open source scripting language have maintained that they were never involved in the initiative in the first place.
The Internet Bug Bounty is a high profile security bug bounty program that aims to help protect ‘core internet infrastructure’. The initiative is overseen by a global panel of vulnerability disclosure experts, with individual programs housed on the HackerOne platform.
Under the scheme, researchers are offered financial rewards for the discovery of flaws in key technologies including the Django web framework, NGINX web server software, and the OpenSSL cryptographic library – not to mention a program for ‘The Internet’ itself.
Numerous programming languages are counted among the Internet Bug Bounty’s list of targets, including Python, Ruby, and Perl.
The same, however, can no longer be said for PHP, the general-purpose scripting language that underpins a vast swath of web apps and services, after it was removed from the Internet Bug Bounty program last month.
‘Shut down indefinitely’
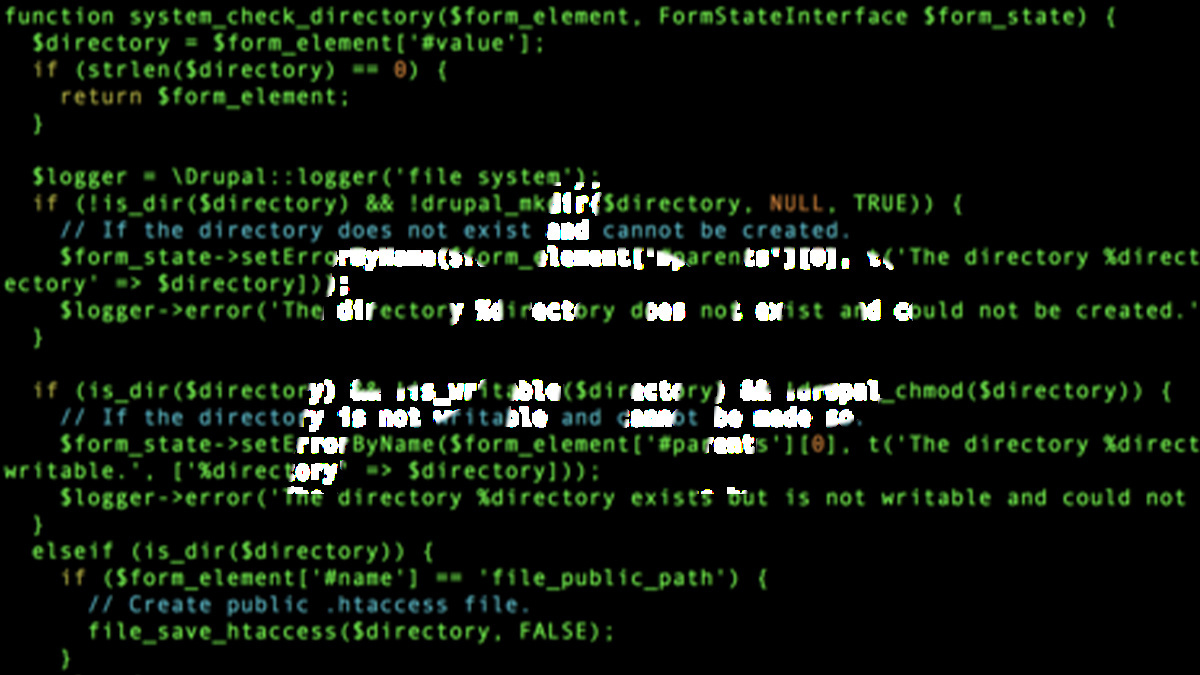
On October 12, the HackerOne triage team flicked the switch to ‘public’ on a PHP security vulnerability report (#505278) that was initially submitted in May 2019.
Although the report describes a relatively low impact (and since resolved) denial-of-service vulnerability, it was the comment thread below that commanded attention.
“On behalf of the Internet Bug Bounty panel, thank you for your continued patience on this report,” it reads. “The IBB requires that all in-scope open source projects be mutually engaged with us to ensure there is a good experience for all.
“Unfortunately, we have not been able to maintain that relationship with the upstream PHP community, and as a result, HackerOne and the IBB panel have collectively agreed to shut down the program indefinitely.”
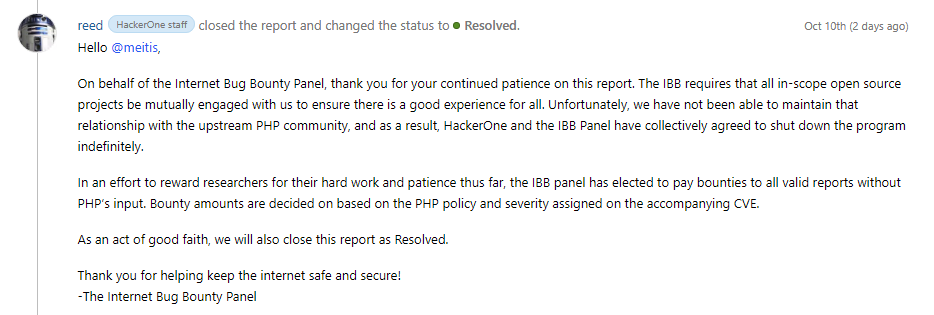 The Internet Bug Bounty comments were buried in a HackerOne vulnerability report
The Internet Bug Bounty comments were buried in a HackerOne vulnerability report
Communication breakdown?
When asked to provide more details on what appears to be a breakdown of communication, Reed Loden, chief open source security evangelist at HackerOne and lead for the Internet Bug Bounty program, said:
All projects supported by the Internet Bug Bounty agree to a certain set of standards with the goal of recognizing and rewarding security research that improves critical internet infrastructure.
As a platform, we work tirelessly to foster a mutually beneficial relationship between security teams and the researcher community.
While hackers on the PHP program were able to surface vulnerabilities through their bug bounty program for some time, we decided to discontinue our partnership for the time being.
However, when quizzed over why the open source scripting language was no longer part of the Internet Bug Bounty, a spokesperson for PHP said they had played no active role in the initiative from the outset.
“There’s no ‘breakdown’ of communication, mainly because there wasn’t much communication to begin with,” the PHP spokesperson told The Daily Swig.
“The [Internet Bug Bounty] program was run without any coordination or input from the PHP community, and the only communication from them I could find was a single email in December 2019 asking for assistance in classifying bugs and for a link from our site to their program.”
Read more of the latest bug bounty news
The spokesperson added: “As our bug classification criteria are already public and so are all bugs that are fixed, and we regularly issue CVE reports for fixed security issues, there’s not much we could further help [with] there.
“There’s no problem with somebody running a bounty program about PHP, even without talking to PHP developers if they prefer so, but you cannot expect the PHP community spend their (limited and volunteer) resources on it on demand when that third party needs it.
“So I would say ‘no longer involved’ is not entirely accurate description as we have never been involved to begin with, and the whole thing has been created and run independently from us.”
In-house bug tracker
PHP may be conspicuous by its absence, but the scripting language no longer appears anywhere in the Internet Bug Bounty’s documentation.
Fortunately for those researchers who have already disclosed PHP vulnerabilities via the HackerOne portal, Reed said the Internet Bug Bounty panel “has elected to pay bounties to all remaining open valid reports”.
From here on in, however, security vulnerabilities should instead be disclosed only through the official PHP bug tracker.
“We deal with vulnerability reports through bugs.php.net,” the PHP spokesperson said. “We triage the bugs, and we issue public CVEs about the fixed issues.”
They added: “We do not plan to run any [bug] bounty program, as we have neither money nor resources to do it.”
READ MORE German armed forces launch security vulnerability disclosure program






