California brings in new data privacy rules; Microsoft takes down bad guys; and a new cybercrime resolution from Russia

Microsoft made an announcement ahead of New Year celebrations this week, explaining that it had seized 50 web domains operated by Thallium, a threat group believed to be from North Korea.
A declassified US district court document from December 27 revealed ongoing work by Microsoft in taking down malicious domain infrastructure via its Digital Crimes Unit (DCU) and Threat Intelligence Center (MSTIC).
The tech giant had been tracking the nation-state actor for months, tracking its activities and gathering intelligence. It then used this intel to obtain a court order to seize the suspect sites.
“Like many cybercriminals and threat actors, Thallium typically attempts to trick victims through a technique known as spear phishing,” Microsoft said in its statement on Monday (December 30).
“By gathering information about the targeted individuals from social media, public personnel directories from organizations the individual is involved with and other public sources, Thallium is able to craft a personalized spear-phishing email in a way that gives the email credibility to the target.”
The seized sites are no longer operational. They were being used to conduct attacks on targets in the United States, Japan, and South Korea, Microsoft said.
And social media users were left perplexed before the new decade began, following the approval of a Russia-led proposal to combat cybercrime.
The resolution, which was placed before the General Assembly of the United Nations, will see the creation of an international committee of experts, tasked with drafting a new convention on countering crime in today’s digital realm. Critics argued the policy offered only a framework to stifle rather than combating cybercrime.
It was passed last Friday (December 27) by a vote 79-60, the AP reports.
US deputy ambassador Cherith Norman Chalet told the Assembly before the vote that “this resolution will undermine international cooperation to combat cybercrime at a time when enhanced coordination is essential.”
“There is no consensus among member states on the need or value of drafting a new treaty,” she said.
“It will only serve to stifle global efforts to combat cybercrime.”
An international treaty on cybercrime already exists in the shape of the 2001 Budapest Convention, which provides a framework to mitigating criminal activity online such as computer fraud, copyright abuse, and network security violations. Russia has notably opposed the treaty.
The news comes as the UN prepares to celebrate its 75th anniversary this year.
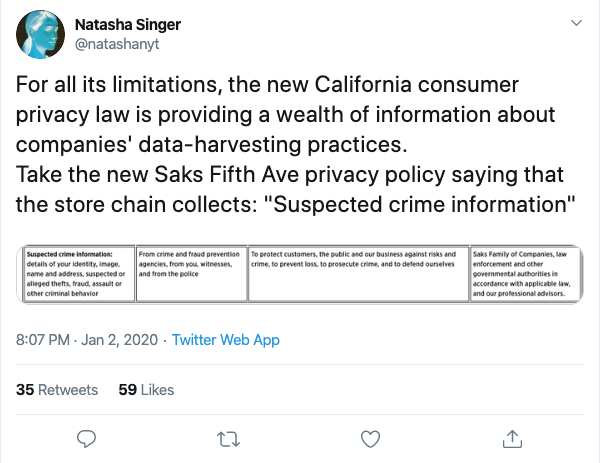
All eyes were on the sunshine state as the clock struck 12 on December 31, as California residents and global privacy advocates alike welcoming the arrival of better data protection.
The California Consumer Privacy Act (CCPA), an American answer to GDPR, came into effect on Wednesday (Jan 1) after much debate between legislatures and tech giants over what consumer rights in the age of Big Data should look like.
Larger businesses operating in California will now have to inform consumers how their personal data is being used, and provide an ability for individuals to opt-out of collection practices, with fines levied for non-compliance.
Financial incentives could also be offered in exchange for consumer data, Tech Crunch reports.
But it’s not all celebrations yet, as the US continues to discuss bringing in a federal privacy law that would render the California rules, the strictest in the country, obsolete.
A step forward, nonetheless.
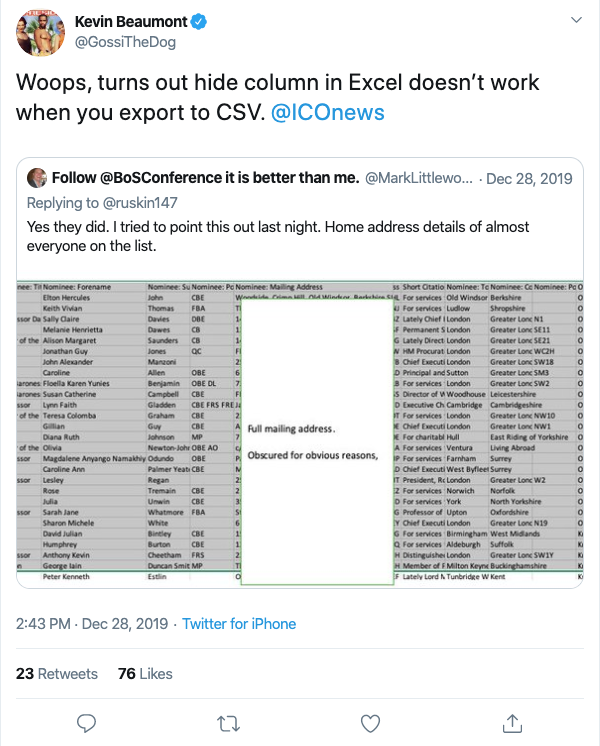
And finally; UK government suffered a bit of an embarrassment over the holidays after it was revealed that the Cabinet Office had accidentally published the home addresses of those found on the country’s annual New Year Honours list.
A total of 1,097 individuals were impacted in the mishap, including Sir Elton John, former Conservative leader Ian Duncan Smith, Olympic gold medallist Jade Jones, and a number of employees of the nation’s Ministry of Defence.
The personal details were publicly available for an hour, the BBC reports, and the Information Commissioner’s Office (ICO), the UK’s data watchdog, is said to be “making inquiries” over the security incident.