Two big data breaches; Google’s healthcare activities fall under the security microscope; and the best of #BadBugBountyPickupLines

Another week, another mega-breach: researcher Vinny Troia went public late last week with the news that 1.2 billion records were exposed by an unidentified Elasticsearch server.
The data – social media accounts, email addresses, and phone numbers – appears to have been collected mostly by data broker People Data Labs (PDL), although the server it was found on did not belong to PDL. It seems likely that a business partner failed to secure it.
Without doubt, 1.2 billion is a massive figure. However, as news of the incident hit the wires, some took issue with the term "data breach" and questioned the severity of the leak, while others criticized the "unnecessary" hype that surrounded the disclosure.
Troia’s announcement was followed on Monday by confirmation from T-Mobile that it had been hit by a data breach impacting a million customers.
The exposed data includes name, billing address, phone number, account number and rate, plan, and calling features, but not financial or password data. It suffered a similar breach in summer last year.
Customers are been encouraged to “confirm or update the personal identification number (PIN/passcode) on your T-Mobile account” in what’s described as encouraging people to take an additional security precaution.
In other news this week, Google’s Threat Analysis Group (TAG) has shared its analysis of state-sponsored hacking and disinformation campaigns.
TAG sent out more than 12,000 warnings over state-sponsored phishing attempts across 149 countries in the third quarter of this year, around the same as in 2017 and 2018.
Staying with Google, the US Office for Civil Rights is investigating whether the organization met HIPAA requirements on data privacy and security when working with the Ascension health system. Google says it did; others are not so sure.
There are also concerns over the company’s plans to buy Fitbit, giving it access to even more health information.
Privacy groups are calling on the Federal Trade Commission to block the $2.1 billion deal, and many users are apparently deleting their accounts.
For its part, Google has launched a video explainer of its digital health tools, including a new single interface for doctors making health records more accessible and easier to search. Ascension will be the first health system to use it.
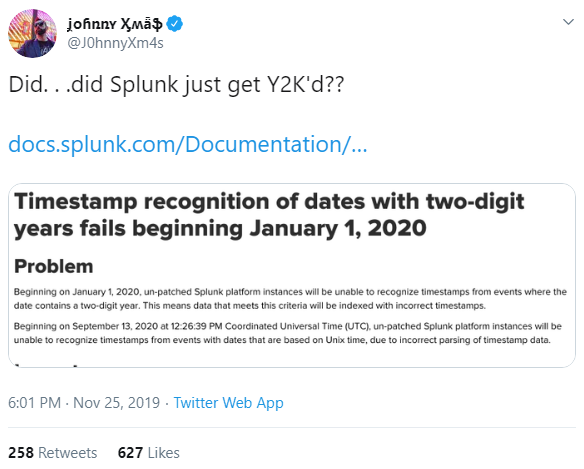
Elsewhere, Splunk users could be forgiven for thinking they’ve gone back in time 20 years: the data analytics platform has warned that timestamp recognition of dates with two-digit years will fail on January 1, 2020.
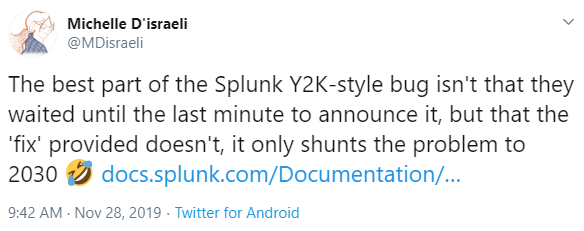
The problem, caused by a flawed file called datetime.xml, affects all unpatched Splunk platform instance types. Customers are urged to get on to it sharpish. However, says Michelle D’israeli, they’ll have to do it all over again in 10 years…
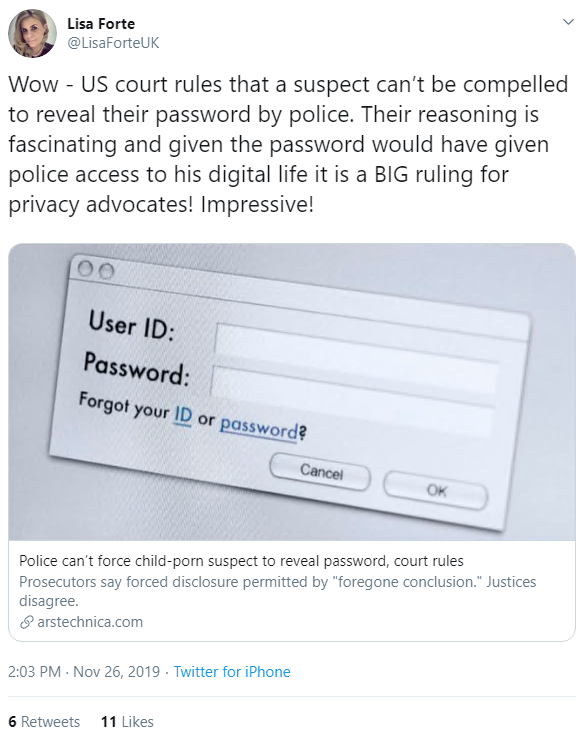
In legal news, the Pennsylvania Supreme Court has ruled that a suspect can’t be compelled to reveal his computer password.
Overturning a previous decision by a lower court, the judges decided that Joseph J. Davis, the accused in a child pornography case, was protected by the Fifth Amendment.
Security pros said the decision was a “big ruling for privacy advocates”.
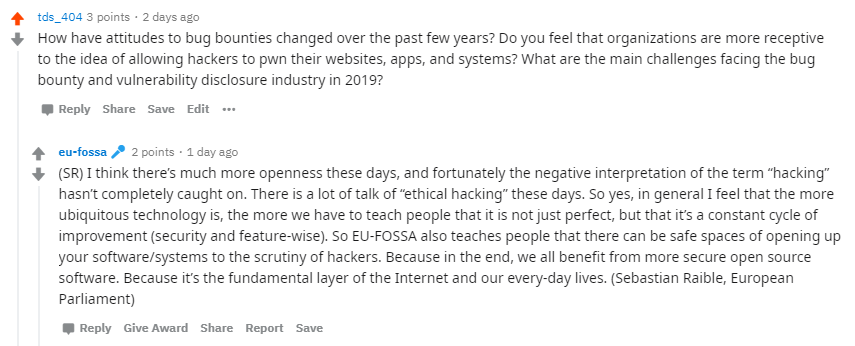
The team behind the EU-FOSSA open source bug bounty program held an ‘Ask Me Anything’ on Reddit yesterday.
EU-FOSSA was created in 2014 to help improve the security and accessibility of crucial internet technologies such as OpenSSL. This year, the program has commissioned 15 bug bounties and three hackathons.
Issues covered in the AMA included patents and standards, standard document formats, and EU funding for open source projects.
Fielding a question on changing attitudes to bug bounties, Sebastian Raible, former assistant to MEP Julia Reda – who created the program – said EU-FOSSA was in favor of opening up software and systems to the scrutiny of hackers.
Read the full AMA to find out more.
And on the subject of bug bounties, the hashtag #BadBugBountyPickupLines has been doing the rounds on Twitter.
Examples ranged from the sweet…
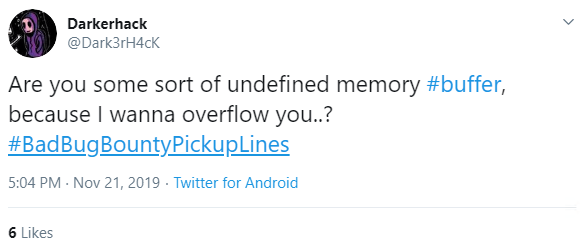
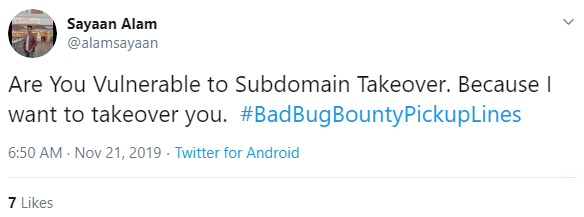
to the suggestive…
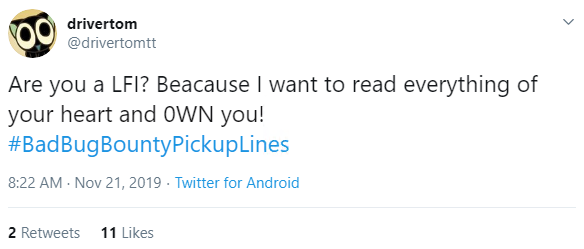
...and even sinister.