Hacking password reset questions, thermal imaging, and rogue USB charging point attacks all featured in this week’s hacker jamboree

Riccardo Spolaor demonstrated how it might be possible to snaffle secrets from an Android device using a doctored power bank, as previously reported in The Daily Swig.
The attack relies on initially planting malicious software on a targeted device, and the data exfiltration rate is painfully slow. Nonetheless, it could be a potentially useful addition to the armory of nation-state-grade hackers.
Instead of just being wary of rogue Wi-Fi access points, travelers now have to be cautious about USB charging points at airports or hotels.
Why hack passwords when you can control the password reset question?
A larger scale potential attack against corporate Windows 10 networks was demonstrated by a duo of security researchers from Illusive Networks on Wednesday.
The exploit involved abusing the password reset questions feature in Windows 10 to gain domain-wide persistence on a network.
Some level of compromised access (specifically first obtaining domain admin privileges) is a prerequisite for the attack, but once that it is achieved hackers might be able to squat on a compromised network for years.
Instead of harvesting passwords or taking a similar approach the hack relies on changing the password reset questions across not just one, but multiple Windows 10 machines on a single domain.
This is a neat approach – not least because users are highly unlikely to change their security reset questions, which a hacker could modify across the board, changing them to something like ‘my first pet was a dog called Fluffy’.
Once the time is right, these password reset questions can then be used to remotely gain control of a local machine.
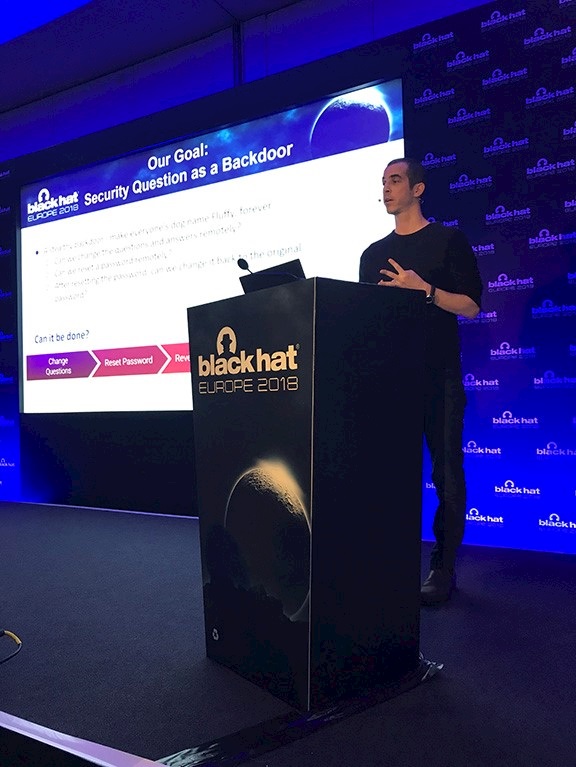
The hack omits any need to execute code on the targeted machine and might be remotely distributed to any Windows 10 machine in the network.
Only Windows 10 devices are vulnerable because the pwnage depends on a feature introduced by Microsoft in April, restricted to this operating system.
Researcher Tom Sela told The Daily Swig that Microsoft regards the hack as an abuse of the newly-introduced mechanism rather than an exploit, so it has no plans to patch it.
Sela and his colleague Baz, who notified Microsoft before their presentation, released their own mitigation tools at the same time they unveiled their research.
Thermanator
Entry codes on PIN pad devices could be spied on using thermal cameras, researchers at UC Irvine claimed based on earlier research.
Computer scientists at UC Irvine took this idea one step further by experimenting to see whether it might be possible to steal passwords by reading the thermal residue on keyboards.
A user's fingers leave thermal marks on keyboard keys that a snooper could record, later using the clip to figure out the characters the user entered.
That's the theory. In practice the approach is poor in determining the order in which keys are entered, plus a spy could be thrown if the same character, such as ‘T’, appears twice in the same password. That’s all once you've isolated character strings associated with password entry.
In enters Thermanator, a framework for password harvesting from keyboard thermal emanations, which is all a bit Mission Impossible.
In experiments, Thermanator allowed the researchers to figure out entire passwords within tens of seconds after entry, as well as greatly aiding attempts to obtain a password where only a partial thermal print is obtained.
The latter is effective even as late as 60 seconds after password entry.
Imaging only works where the keyboard is in close proximity to a thermal (FLIR) camera, something that might not be practical in a multi-user office setting or in a public space, according to the researchers.
For those nonetheless concerned that their keyboards are vulnerable to thermal side-channel attacks, a counter-measure already exists – use a metallic rather than plastic keyboard.
Metallic elements have greater conductivity to heat so thermal residues are not an issue with metallic keyboards, in practice.
Resonance
Thermal imaging might be impressive – but the main prize for sheer mis-appropriation of science during Black Hat Europe has to go to a talk by IBM researchers on attacking hardware systems using resonance.
Researcher Ivan Reedman demonstrated that by finding the resonant frequency of certain electronic sensors, programmable logic, and other devices, it is possible to subvert their normal operation as a component of a multi-stage attack.
The approach spans from ultrasonic attacks on microphones in voice-enabled IoT and mobile equipment, to high frequency electrical resonance inside certain programmable logic controllers.
“Chaining both these attacks and other hardware attacks together can allow software to bypass quite complex hardware security sub systems,” according to Reedman.
You can read more about the presentation here.






