Ethical hackers and bug bounty hunters invited to test Department of Defense assets
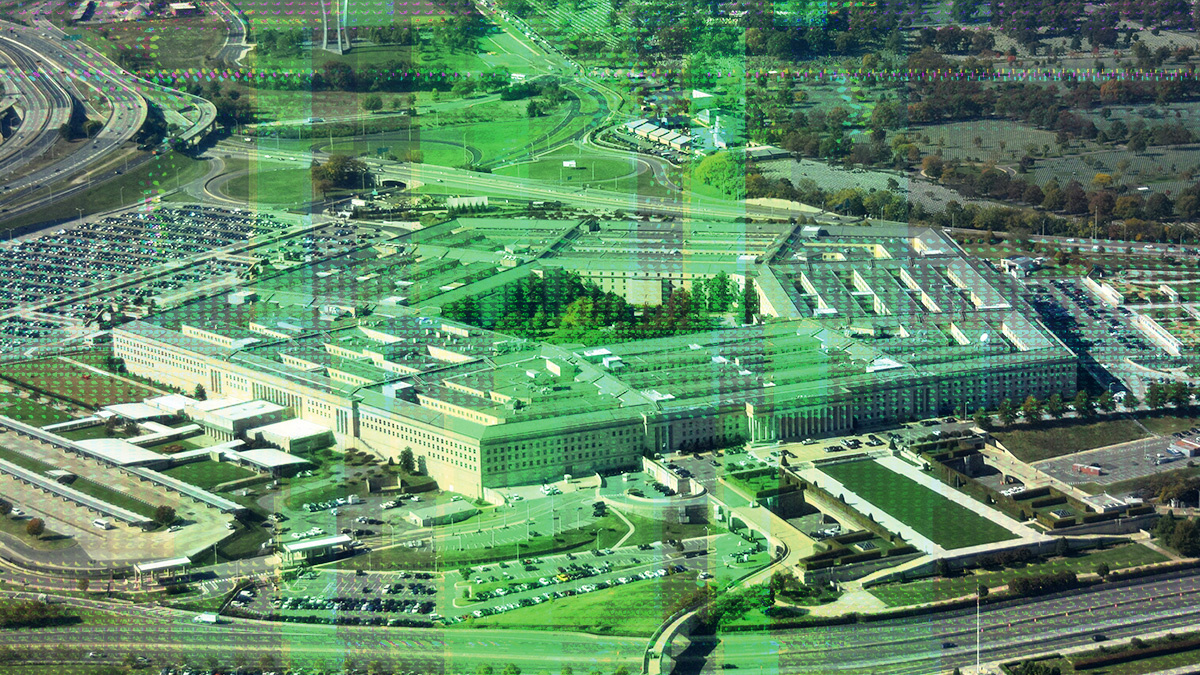
The US Department of Defense (DoD) is holding its third annual Hack The Pentagon challenge, it announced this week.
Hack The Pentagon was launched in 2016, opening the door for security researchers to look for vulnerabilities in some of its top assets.
Since its creation, the program has seen more than 600 ethical hackers and bug bounty hunters invited to find bugs in DoD resources, resulting in the disclosure of more than 700 issues so far.
Read more of the latest bug bounty news
In a statement posted to the US government website, the DoD confirmed it will be organizing a third iteration of the competition this year.
It also confirmed that it is looking for contractors to partner on the program.
“The DoD’s first Vulnerability Disclosure Policy (VDP) established a 24/7 pathway for security experts to safely disclose vulnerabilities on public-facing DoD websites and applications,” the US government website states.
“DDS [Defense Digital Service] has ongoing contracts with security firms HackerOne, Synack, and Bugcrowd to facilitate assessments for DoD components and military services against their respective assets.”
Going further
In 2021, the DoD expanded its VDP beyond its public-facing websites and web applications to encompass all publicly accessible information systems.
This brought into scope all public-facing DoD networks, radio frequency-based communication platforms, IoT devices, and industrial control systems, among other technologies.
BACKGROUND US government launches ‘Hack the DHS’ bug bounty program
Also 2021, the US Department of Homeland Security (DHS) also launched a bug bounty program, inviting selected security researchers to test for vulnerabilities in its systems.
Dubbed ‘Hack the DHS’, the program, held in 2022, included three different phases – a pen test, a live hacking event, and a detailed review process.
More than 450 vetted security researchers identified 122 vulnerabilities, of which 27 were subsequently determined to be critical, the DHS revealed, adding that it awarded a total of $125,600 for the bugs.
RECOMMENDED Tell us what you think – fill out this quick survey and be in with a chance of winning Burp Suite swag






