Torrent client issues patch for RCE vulnerability that allows hackers to take full control of users’ devices.

uTorrent users are being urged to update their apps after a bug left them open to remote code execution.
The flaw was related to uTorrent’s remote feature for Windows, which gives users the option to manage torrents from a browser on another device.
JavaScript in a malicious web page can hijack the victim’s router, resulting in a DNS rebinding attack, forcing the hacker’s commands in the desktop app.
These commands include reading and copying torrents and downloads.
Another flaw meant that hackers could download an arbitrary .exe file into the computer’s startup folder, which would then run malware when the system was rebooted.
The vulnerabilities were found by Google Project Zero researcher Tavis Ormandy back in November.
He reported his findings to uTorrent’s parent company, BitTorrent, last year, but went public this week after the file-sharing service surpassed its 90-day patch deadline.
In his proof of concept write-up, Ormandy said: “You can just fetch the [authentication] secret and gain complete control of the service.
“This requires some simple DNS rebinding to attack remotely, but once you have the secret you can just change the directory torrents are saved to, and then download any file anywhere writable.”
The vulnerability is now fixed, according to BitTorrent, which has now issued a patch in a beta release. An official update will be issued in the coming days, according to the company.
Dave Rees, BitTorrent's vice president of engineering, said: “All users will be updated with the fix automatically over the following days.
“The nature of the exploit is such that an attacker could craft a URL that would cause actions to trigger in the client without the user’s consent (e.g. adding a torrent).”
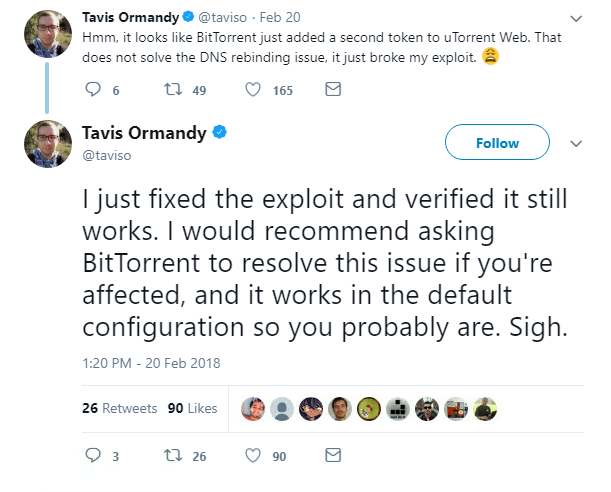
The patch involves adding a second authentication token to the web browser, although Ormandy claims this does not fix the DNS rebinding issue:
Users are now being directed by BitTorrent to version 3.5.3.44352 or higher of the desktop app and version 0.12.0.502 and higher of the web app.