Optical retailer blindsided by malicious script

Complete credit card details of thousands of customers were exposed as the result of a breach at UK online contact lens retailer Vision Direct.
A malicious script on the site earlier this month meant that personal and financial information submitted to the site between “12.11am GMT 3rd November 2018 and 12.52pm GMT 8th November 2018” was compromised, a breach notice from Vision Direct put out on Sunday (November 18) explains.
“The personal information was compromised when it was being entered into the site and includes full name, billing address, email address, password, telephone number, and payment card information, including card number, expiry date, and CVV,” it warns.
Data submitted prior to November 3 is thought to be safe because hackers only succeeded in planting a malicious script, rather than breaking into Vision Direct’s database or the systems of its payment partners.
“All payment card data is stored with our payment providers and so stored payment card information was not affected by the breach,” Vision Direct added.
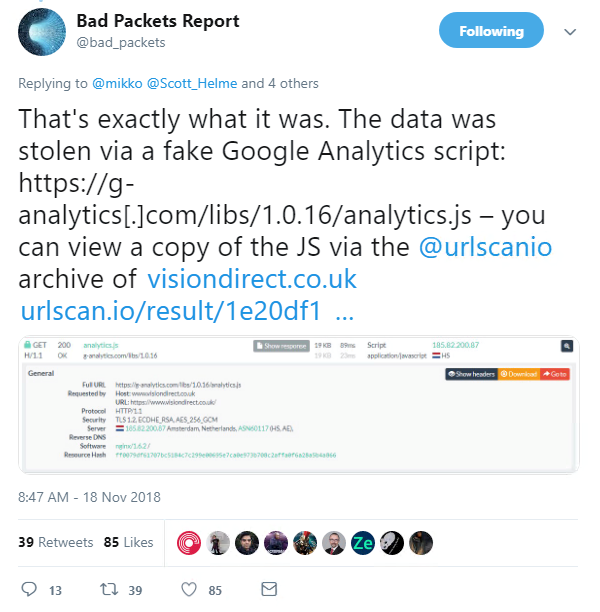
Security researcher Troy Mursch fingered a fake Google Analytics script as the main agent of the heist. The hostile JavaScript was unpicked weeks ago, back in early September, by security researcher Willem de Groot.
Vision Direct told the BBC that it was hit by a variant of this so-called ‘Shoplift’ attack that slipped past its defences, despite a recent patching by its web platform provider.
The retailer estimates that 6,600 customers have had their financial data exposed, while a further 9,700 individuals had their personal data lifted.
Affected UK customers will likely by indemnified against potential direct losses by their credit card issuer, but that still leaves the fretful nuisance of requesting new credit cards and resetting passwords, to say nothing of the heightened risk of identity theft they face as a result of the incident.
Start-up bank Revolut proactively identified 80 customers potentially affected by the breach before issuing them with new cards.
A spokeswoman for UK data protection watchdogs at the Information Commissioner’s Office said it wasn’t handling the incident since Vision Direct is owned by a French company.
Vision Direct is yet to respond to queries on its response to the breach from The Daily Swig.