New security mechanism throws up outdated PHP warnings

WordPress 5.1 rolled out to users on Friday complete with Site Health, a new security mechanism designed to alert site owners when they are using outdated versions of PHP.
According to the developers of the world’s most popular CMS, when installing new plugins, Site Health will check to see if the add-on requires a version of PHP that’s incompatible with the site.
If so, WordPress will prevent web admins from installing the plugin.
According to Felix Arntz, a Google engineer and WordPress core committer, the move will help close the server-side capability gap while also improving the performance and security of the web.
“WordPress 5.1 will start showing notices to administrators of sites that run on long outdated PHP versions,” Arntz said in a recent technical blog post.
“This… paves the way to a more secure and performant web and, more specifically to WordPress, to a bump of the minimum required PHP version.”
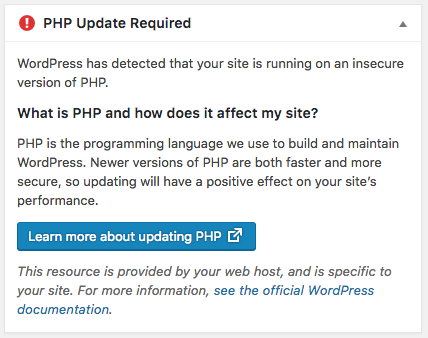
PHP is the general-purpose programming language that underpins all WordPress sites.
The popularity of PHP has resulted in it becoming a prime target for hackers, and WordPress said keeping PHP up to date is “just as important” as ensuring you are running the latest version of WordPress core, along with any themes and plugins.
From the outset, Site Health will alert users to any plugins that require PHP versions 5.5 and lower.
“While the lowest PHP version still receiving security updates is currently 7.1, the idea is to not go all the way there at the beginning to limit the support load,” Arntz said.
“This project benefits not just WordPress users, but also the surrounding PHP ecosystem as a whole,” said WordPress consultant Alain Schlesser. “Our hope is that this will prompt a lot of PHP updates across the web.”
In addition to Site Health, the latest version of WordPress includes performance improvements within the editor, improved taxonomy sanitization, and a new “doing it wrong” notice when registering API endpoints.
Web admins who have not yet updated to WordPress 5.1 can do so through their dashboard, or via the WordPress core download page.
RELATED Fresh exploit takes the shackles off disabled PHP functions






