Severity of code execution bug mitigated by ‘high uptake’ of previous patch

Zyxel has released patches for several of its firewall products following the discovery of two security vulnerabilities that left business networks open to exploitation.
First on the list is CVE-2022-2030, an authenticated directory traversal vulnerability in the Common Gateway Interface (GLI) programs of some Zyxel firewalls. This was caused by specific character sequences within an improperly sanitized URL.
The second flaw, CVE-2022-30526, is a local privilege escalation (LPE) vulnerability that was identified in the command-line interface (CLI) of some firewall versions.
Left unpatched, the flaw could allow a local attacker to execute some OS commands with root privileges in some directories on a vulnerable device.
Breaking the chain
The privilege escalation issue impacting Zyxel firewalls was discovered by security researchers from Rapid7. The vulnerability allows a low privileged user, such as nobody, to escalate to root on affected firewalls.
As explained in a technical blog post from Rapid7 on July 19, an attacker could establish shell access on the firewall by exploiting CVE-2022-30525 – a separate bug that was discovered by the same researchers and fixed by Zyxel earlier this year.
Read more of the latest infosec research news
Fortunately, the severity of this latest vulnerability has been mitigated by strong uptake of the previous fix.
Jake Baines, lead security researcher at Rapid7, told The Daily Swig: “CVE-2022-30526 is useless unless you are able to chain it with a vulnerability like CVE-2022-30525.”
He added: “We are happy to report that we’ve seen very high uptake on the patch for CVE-2022-30525, so Zyxel’s patch for CVE-2022-30526 is almost purely a defensive measure – at least until another remote code execution vulnerability is found in their firewalls. Then the patch will have paid off.”
The path traversal issue was discovered by Italian security researcher Maurizio Agazzini of HN Security.
“We agree with Zyxel to release further details of the vulnerability around mid-August in order to allow their customers to have the time to patch all systems,” Agazzini told us.
Firmware patches
The latest vulnerabilities affect various versions of several Zyxel firewalls, including USG Flex, ATP Series, VPN Series, and USG ZyWall.
The table below lists the vulnerable versions of each product line:
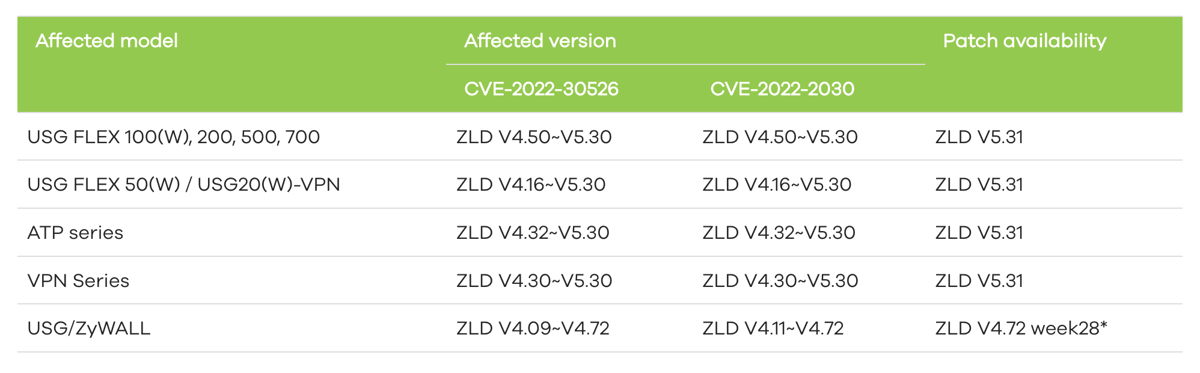
Firmware patches are now available. “Users are advised to install them for optimal protection,” Zyxel said.
Full details can be found in an accompanying security advisory.
YOU MIGHT ALSO LIKE WordPress plugin security audit unearths dozens of flaws impacting 60,000 websites






