Top infosec trends in the social media spotlight this week

Blue is the color
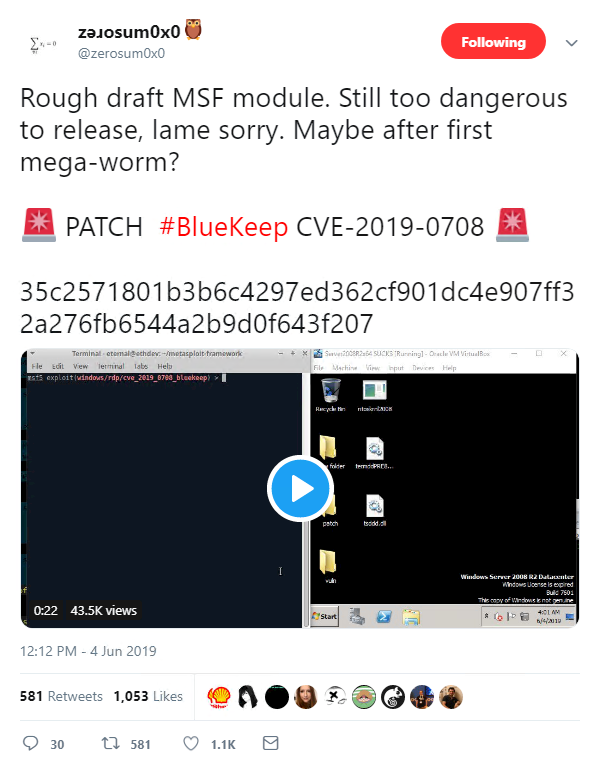
This week, the US National Security Agency (NSA) issued an advisory urging Windows admins and users to ensure they have installed the necessary patches to protect against CVE-2019-0708 – better known as ‘BlueKeep’.
BlueKeep fell into the security spotlight last month, as Microsoft provided details of a critical remote code execution (RCE) vulnerability in its Remote Desktop Services software.
According to the company, the “wormable” flaw requires no user interaction and can be exploited to remotely push malware onto vulnerable systems.
Despite a patch being made available, research published last week indicates that nearly a million machines were still vulnerable.
What’s more, highlighting the severity of the flaw, researchers have been busy developing proof-of-concept exploits that spell utter pwnage for unpatched Windows machines.
Fortunately, the exploit code remains under wraps.
“NSA urges everyone to invest the time and resources to know your network and run supported operating systems with the latest patches,” the security agency said.
“This is critical not just for NSA’s protection of national security systems but for all networks.”
BlueKeep is only exploitable on legacy Windows machines, but in the wake of devastating malware incidents such as WannaCry and NotPetya, it’s clear that natsec operatives at Fort Meade are getting twitchy.
And with this, Gizmodo takes the prize for best headline this week:
Healthcare breach-fest
It’s only June 7, but healthcare data breaches have already been coming in thick and fast this month.
Blood testing company Quest Diagnostics said nearly 12 million customers may have had their personally identifiable information compromised following a breach at a third-party billing services provider, American Medical Collection Agency (AMCA).
RELATED AccuDoc data incident highlights ‘growing calamity’ of third-party breaches
The security incident also affected LabCorp, another medical testing business, which said the personal and financial data of 7.7 million customers was exposed.
Healthcare firms Optum360 and OPKO Health were also said to be impacted by the breach.
All of this comes after the US Department of Health and Human Services (HHS) reported an “all-time record year” in healthcare breach enforcement activity, with organizations paying out more than $28 million in settlement fees in 2018.
GandCrab authors scuttle away... with $150m
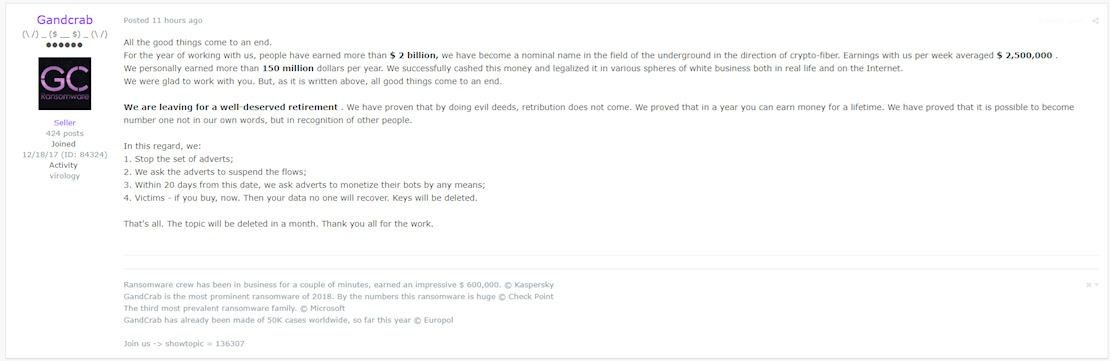
Criminals behind the notorious GandCrab ransomware strain have announced that they are rolling back their campaign and heading into retirement.
In a Russian forum post, a GandCrab member said the ransomware-as-a-service (RaaS) operation generated more than $2 billion in payments for the crew’s script kiddie customers.
“We personally earned more than 150 million dollars per year,” the post reads. “We successfully cashed this money and legalized it in various spheres of white business both in real life and on the Internet.”
GandCrab exploded onto the ransomware scene in January last year, catching the attention of global cybersecurity firms and law enforcement alike.
In October, Europol’s No More Ransom project issued a decryption tool for certain versions of GandCrab. By this point, however, the malware was already thought to have infected nearly 500,000 devices.
“We are leaving for a well-deserved retirement,” the forum post reads. “We have proven that by doing evil deeds, retribution does not come. We proved that in a year you can earn money for a lifetime. We have proved that it is possible to become number one not in our own words, but in recognition of other people.”
Apple: The last stand
And finally, all eyes were on Apple this week as it hosted the annual World Wide Developers Conference in San Jose.
During the event, the company previewed macOS Catalina – which will ship with a range of new security features – and unveiled new, privacy-focused login technology that’s designed throw web trackers off users’ scent.
These positive developments, however, were somewhat overshadowed by the company’s announcement that the ‘Pro Stand’ for its high-end Pro Display XDR screens would ship for a whopping $999.
Yes, that’s nine hundred and ninety-nine American dollars. For a monitor stand.
Perhaps unsurprisingly, the meme was strong with this one: