OSINT resource used to share C2 servers, payloads, and other IoCs

A platform for sharing and requesting indicators of compromise (IoCs) associated with different malware strains is the latest open source intelligence (OSINT) service launched by Abuse.ch.
Unveiling the platform in a blog post this week, Roman Hussy, the Swiss security expert behind Abuse.ch, says he envisages ThreatFox being used by “security researchers, threat analysts, CERT/CSIRT/SOC employees” and infosec enthusiasts to share threat intelligence with the infosec community, antivirus vendors, and threat intelligence providers.
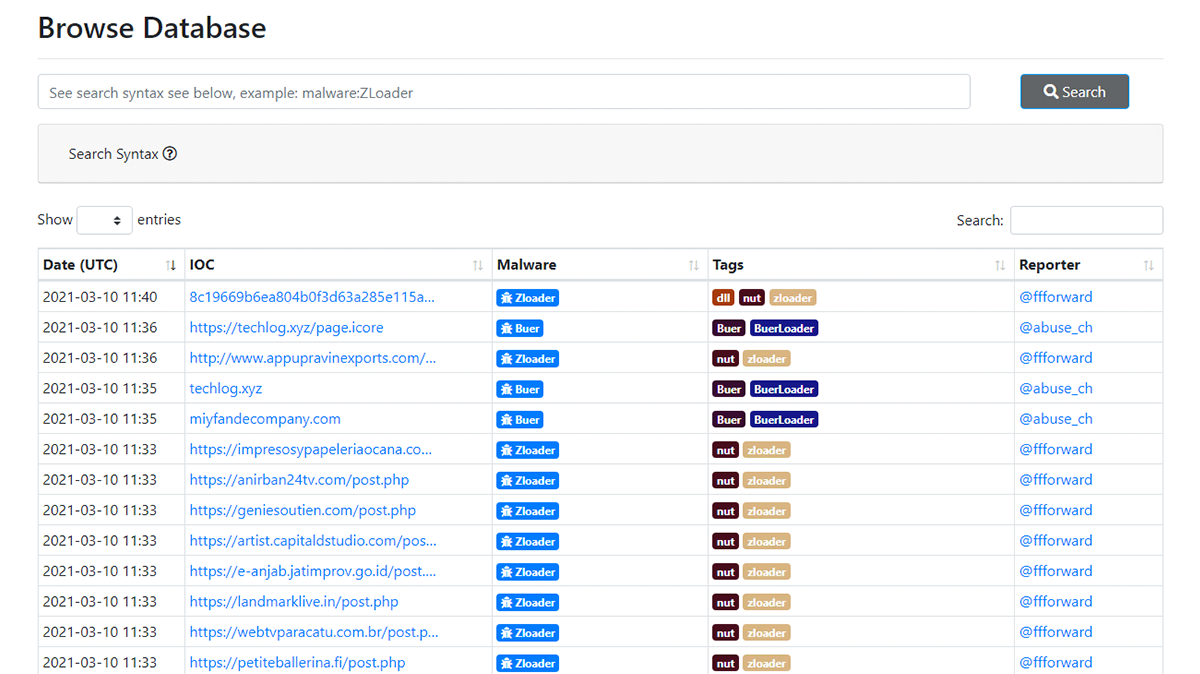
Contributors can share – anonymously if they prefer – domains, IP addresses, email addresses, and file hashes associated with malware, botnet command and control (C2) servers, payloads, and payload delivery mechanisms.
BACKGROUND OSINT: What is open source intelligence and how is it used?
Users can also browse existing IoCs to enhance their visibility of the threat landscape, submit requests for IoCs, or browse existing IoC requests.
As well as using the web interface, threat analysts can use the ThreatFox API to integrate the service into their security information and event management (SIEM) and other infrastructure.
 ThreatFox users can search for malware samples by hash, ClamAV signature, and more
ThreatFox users can search for malware samples by hash, ClamAV signature, and more
IoC taxonomy
Every IoC is associated with a malware family based on Malepdia’s malware-naming scheme.
ThreatFox contributors assign a confidence level between 0%-100% to reflect their level of conviction that an IoC, “if observed in a production environment, would indicate a compromise of your network with malware”.
They are encouraged to assign high scores only to IoCs they have manually vetted and to only share IoCs that are up to 10 days old.
Contributors can also add comments and external references such as links to white papers or social media posts.
RECOMMENDED Williams Racing aborts plans to unveil new F1 car via augmented reality app following hack
Trust system
Five ‘credits’ are awarded for each valid IoC, unless the IoC fulfils criteria for specific requests, for which requestors set rewards of up to 100 credits.
ThreatFox users who share high quality IoCs may in future be flagged as a ‘Trusted Reporter’, in which case subsequent submissions will be accepted without further vetting.
IoCs can be exported in MISP events, JSON, CSV, and Suricata IDS ruleset formats, among others.
A statistics page charts the number of IoCs submitted over time – more than 3,000 since submissions began in December 2020, at the time of writing – the most active malware families, IoCs by type, most popular tags, and a league table of the most prolific contributors.
Incident response time-saver
Hussy launched the registration-free ThreatFox service because existing equivalent platforms require registration to share or retrieve IoCs, meaning IoCs are often shared publicly on GitHub or Twitter.
This, he said, can throw up hurdles because “you need to invest a lot of time into searching for these IoCs and, even worse, automation is in many cases not easily possible (if not impossible)”.
“The goal of Abuse.ch always was to make threat intelligence [easily] accessible for everyone – for free, and without the need of a registration on a platform,” he said.
Catch up on the latest malware news
The ThreatFox website and API complement Abuse.ch’s malware sample sharing site MalwareBazaar, which was launched in 2020, and URLhaus, unveiled in 2018 as a means to share malware distribution sites.
Abuse.ch, a non-profit project that relies on community donations, also operates ‘I Got Phished’, a repository of information about phishing victims launched in 2020, the SSL Blacklist (SSLBL), established in 2014, and Feodo Tracker, a resource for sharing Feodo-associated botnet C2 servers launched in 2010.
The arrival of ThreatFox also follows the launch, by security researcher John Page in January, of Malvuln.com, a repository of code for exploiting security flaws in malware.
The Daily Swig has contacted Roman Hussy with further questions and we will update the article accordingly should we receive a reply.






