Attack on Taiwan seemingly a case of ‘when’ not ‘if’
Chris Krebs, the former director of the US Cybersecurity and Infrastructure Security Agency (CISA), says the infosec industry is “bearish in the short term, bullish in the long term” on the prospects for US national cyber-resilience.
The ex-director, now a founding partner of Krebs Stamos Group, told an audience at Black Hat USA that a likely Chinese attack on Taiwan meant organizations had to act now on making their digital infrastructure and supply chain resilient during the opening day of the annual conference, this year held both physically and virtually.
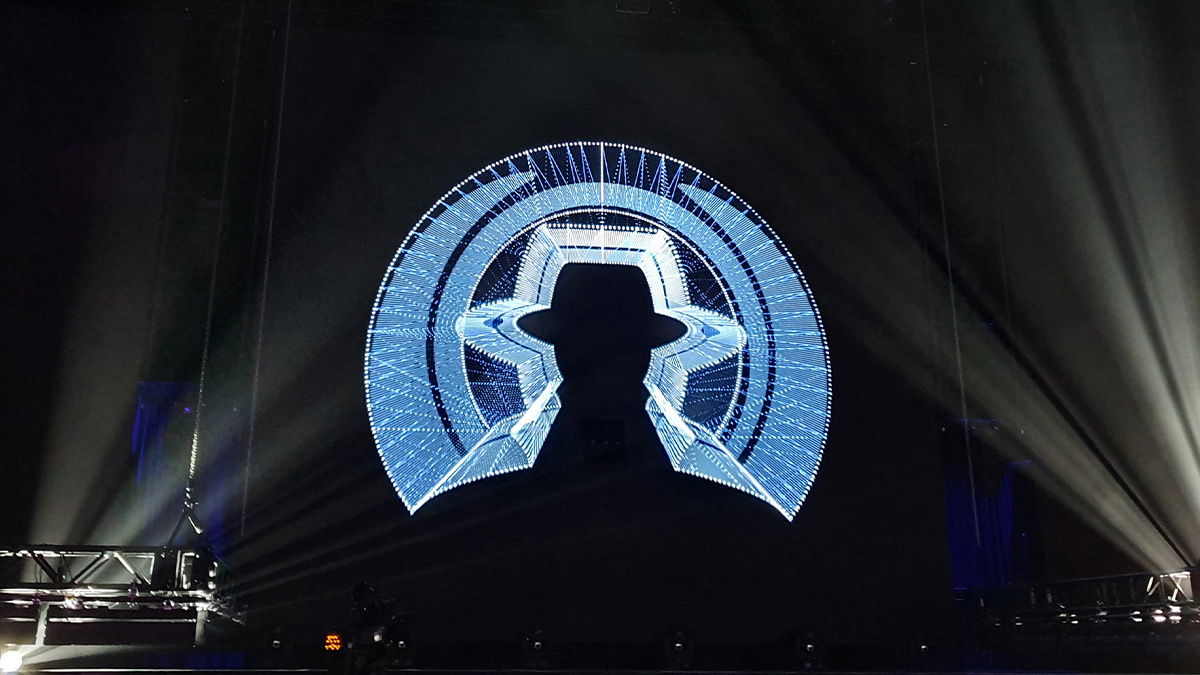
Krebs addressed attendees on the conference’s 25th edition as the opening keynote speaker.
Taiwan in dire straits
Earlier, Black Hat founder Jeff Moss introduced the talk by reflecting on how Russia’s invasion of Ukraine had awakened the infosec community to its power to help the government defend human rights and tackle “mis, dis, and mal information”.
Krebs, who served under President Donald Trump, said organizations, too, had an obligation to have principles and red lines in place before further geopolitical conflagrations erupted – for both ethical and self-interested motives.
Catch up with the latest cyber warfare news
US officials had indeed told him that they were "pretty confident" that the Taiwan tensions are "going to come to a head" at some point, as Krebs warned that organizations should “manage risk yesterday”, game out how it might affect their supply chain and IT operations, and physically segment their networks in Taiwan starting “now”.
Workforce shortage
Krebs noted that he found it “confounding” that the cybersecurity workforce continues to face workforce shortages. After all, the cybersecurity career was fun, lucrative, durable, fascinating, and – given that national security was at stake – meaningful, he said.
One key to addressing growing cyber-threats is providing more opportunities for young people to experience coding and to instil “critical thinking skills”, suggested Krebs.
 Chris Krebs at Black Hat USA: US Department of Defense has “incredible purchasing power – they must use it”
Chris Krebs at Black Hat USA: US Department of Defense has “incredible purchasing power – they must use it”
On a more positive note, he took hope from an increasingly tech-native workforce.
Another reason for cheer was found in the boardroom, with “a CEO that sees cyber risk as business risk is rare, but that is changing post-Colonial [Pipeline ransomware attack].”
Unthinkable complexity
The workforce gap is fuelled by, as Krebs described (PDF) it to a US congressional committee, society’s “pathological need to connect everything to the internet”, resulting in a ballooning attack surface.
The targets are increasingly complex too, to the point where even experts struggle to understand what Neuromancer author William Gibson prophetically called “the unthinkable complexity” of cyberspace.
Citizens, infosec professionals, and organizations alike must reckon with the fact that every country in the world – not just China, Russia, Iran, and North Korea – is seeing the internet as the “fifth domain”, through which they can surveil, destroy, and disrupt, observed Krebs.
Meanwhile, ransomware groups are capable of exploits that were sole preserve of nation states only few years ago, and that following NotPetya, the 2015 Ukraine power grid attack, and the SolarWInds hack, more novel, innovative attacks would inevitably arise, he warned. “We’ve fetishized the APT threat while cybercriminals have eaten our lunch,” said Krebs.
Krebs set out his prescriptions for how the cybersecurity industry and government should get ahead of the coming threats. Government, for instance, should leverage its role as consumer, enforcer, defender, and enabler. As a consumer, to take one example, he said: “The US Department of Defence the largest customer of big tech firms” with “incredible purchasing power – they have to use it.”
As for his former employer, CISA, he insisted that it is, and must continue to be, apolitical.
RECOMMENDED The best Black Hat and DEF CON talks of all time






