Top infosec trends in the social media spotlight this week

For far too long companies have been dodging their cyber defenses, preferring to implement reactive measures instead of saving consumer heartbreak whenever the inevitable data breach occurs.
But the tides appear to be turning toward a security-first practice, particularly with this week’s launch of the annual Ponemon Institute Cost of a Data Breach Study.
Released in partnership with IBM Security, the report found that the average cost of a data breach globally had risen 6.4% since last year – a total of $3.86 million.
It was the first time the study, now in its 13th year, took into account the damages associated with ‘mega breaches’ of up to one million to 50 million records lost – where a loss of business tended to deal the biggest blow to companies, sitting at approximately $118 million for an incident affecting 50 million records.
"The truth is there are many hidden expenses which must be taken into account, such as reputational damage, customer turnover, and operational costs.
“Knowing where the costs lie, and how to reduce them, can help companies invest their resources more strategically and lower the huge financial risks at stake," said Wendi Whitmore, Global Lead for IBM X-Force Incident Response and Intelligence Services (IRIS).
No stranger to bad press, Facebook was slapped with a £500,000 fine from the Information Commissioner’s Office (ICO) in the UK on Tuesday, following the highly publicized Cambridge Analytica scandal.
“A significant finding of the ICO investigation is the conclusion that Facebook has not been sufficiently transparent to enable users to understand how and why they might be targeted by a political party or campaign,” the ICO said, doling out the social media conglomerate with the maximum fine for the data misuse, which affected 87 million of its users.
The ICO added that Facebook had “failed” at preventing Cambridge Analytica, which has rebranded as a new company by the way, from allowing personal information to be manipulated for political profiteering.
But some, if not all, think it’s the ICO that has failed in holding the social media giant to account, saying that the potential fine is a mere blip in the radar of a company that makes £500,000 about every eight minutes.
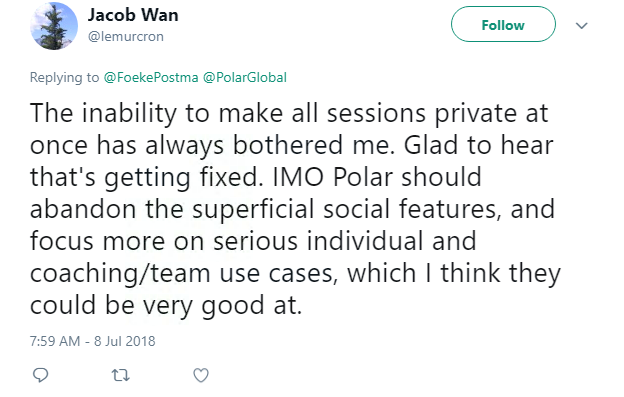
While Facebook wrestles with improving its privacy settings, another popular site’s lack of data protection caused some serious concern this week.
Polar Flow, a fitness app that records daily activity to create bespoke health plans, was forced to suspend its GPS location tracker after researchers found it was revealing sensitive information on the whereabouts of military personnel abroad.
As social media reminisced of Strava, another fitness app that inadvertently advertised the exercise routes of armed forces in Syria and Afghanistan, the Dutch Minister of Defence said apps like Polar should be removed immediately from the phones of its military.
Unlike Strava, Finnish-based Polar was noted to gather significantly more data in a way that was all too easy to access, including the home addresses of its users.
“It is important to understand that Polar has not leaked any data, and there has been no breach of private data,” the company said, explaining that it was a user’s choice whether they wanted to opt in to the location tracking feature or not – the app is private by default.
Meanwhile this week, proving to be an effortless resource for adversaries, UC Irvine’s Donald Bren School of Information and Computer Sciences managed to exploit the heat traces left on a keyboard for those up for deploying covert attack approaches.
These thermal residue-based keyboard attacks allow assailants to steal a user’s credentials by determining which keys were pressed after putting the lens of thermal imaging camera to them.
The group of academics found that passwords could be cracked “up to one minute after the victim enters them,” and that this sort of side-channel attack may enlist further support for a password-free future.