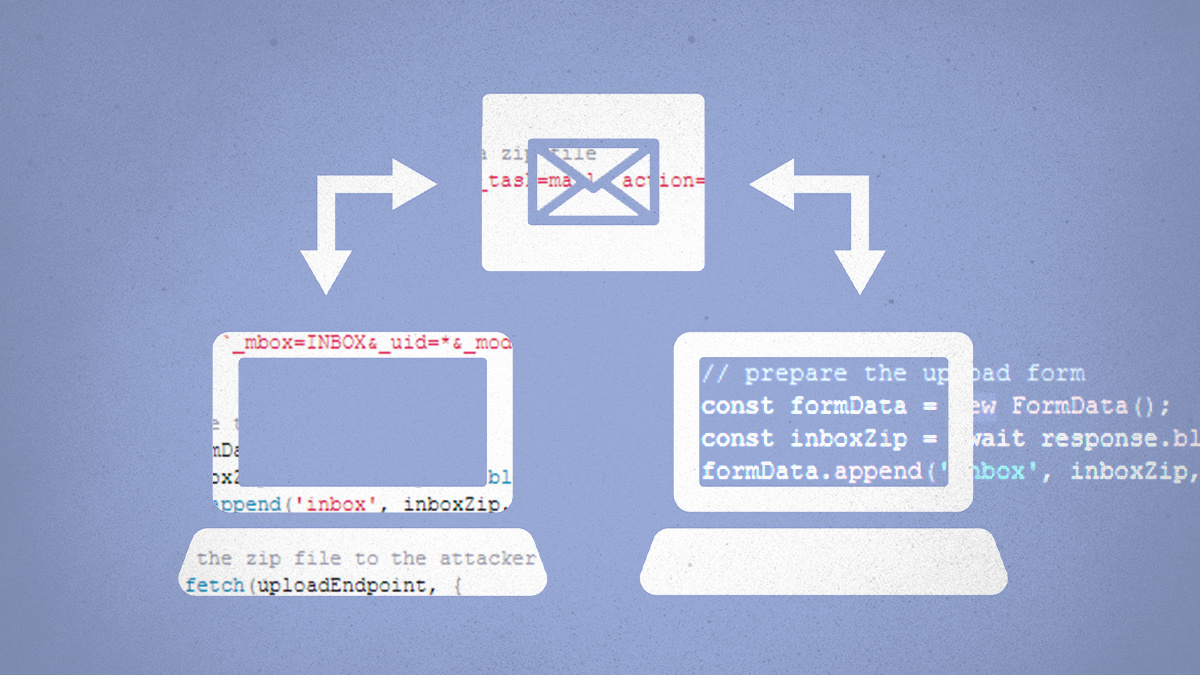
Msg spool attack threat
UPDATED Security researchers at Qualys have uncovered multiple security vulnerabilities in Exim, one of the most popular mail transfer agents.
During a full security audit of Exim, the researchers found 21 vulnerabilities. Eleven of the vulnerabilities were only exploitable locally, but the remaining 10 might lend themselves to remote exploitation.
Worse yet, several of these remotely exploitable issues could be chained together with local privilege escalation flaws to create a full remote code execution attack, Qualys warns.
Digital paper trail
The issues go back to at least the beginning of Exim’s Git history, in 2004, so all supported versions of the software need updating.
The vulnerabilities are tracked as CVE-2020-28007 through CVE-2020-28026, plus CVE-2021-27216.
Catch up on the latest vulnerability research
Qualys has demonstrated that three of the flaws pose an unauthenticated RCE risk – a severe class of vulnerability that requires no action from the victim and can result in full system takeover.
The trio of critical security flaws include CVE-2020-28020, an integer overflow in receive_msg(); CVE-2020-28018, a use-after-free flaw in tls-openssl.c; and CVE-2020-28021, a new-line injection into spool header file.
Details of the 21 flaws are covered in a technical blog post by Qualys. A landing page with a walkthrough video has also been released.
In response to questions from The Daily Swig , Qualys offered more details on the threat posed by the vulnerabilities
There is no need to chain vulnerabilities to achieve RCE. What needs to be chained is one RCE that yields an unprivileged access to the server, and one LPE [local privilege escalation] that transforms that unprivileged access into a privileged one (i.e. root access).
For example, we chained CVE-2020-28018 (an unauthenticated RCE) with CVE-2020-28008 (a LPE, Local Privilege Escalation) to obtain full root privileges in our demo video.
Server-side mayhem
Exim mail servers are popular in their category and handle a large volume of internet traffic, making them an attractive target for attackers.
RELATED Critical Exim bug impacts more than half of all email servers
Bharat Jogi, senior manager, vulnerability and threat research at Qualys, commented: “The 21 vulnerabilities we found are critical as attackers can remotely exploit them to gain complete root privileges on an Exim system – allowing compromises such as a remote attacker gaining full root privileges on the target server and executing commands to install programs, modify data, create new accounts, and change sensitive settings on the mail servers.text
“It’s imperative that users apply patches immediately,” Jogi concluded.
A recent survey by E-Soft found that three in five (60.7 %) of publicly accessible email servers ran Exim, way ahead of its closest rival Postfix. The Exim platform is particularly popular as a mail transfer agent package with universities, for example.
On May 17, security researchers released a proof-of-concept exploit for the Exim use-after-free flaw that leads to remote code execution.
This story was updated to add comment from Qualys. This story was updated again to include proof-of-concept details.
YOU MIGHT ALSO LIKE Pulse Connect Secure zero-day stars in critical patch batch






