Top infosec trends in the social media spotlight this week

This week delivered a dose of déjà vu to the tech community, as reports surfaced of yet another series of “critical” chip-level flaws – this time affecting CPUs manufactured solely by Intel rival, Advanced Micro Devices (AMD).
Two months after a team of researchers uncovered the Meltdown and Spectre vulnerabilities, Israeli cybersecurity research firm CTS-Labs has dropped a white paper outlining no less than 13 ’major’ flaws in AMD’s latest Zen processors.
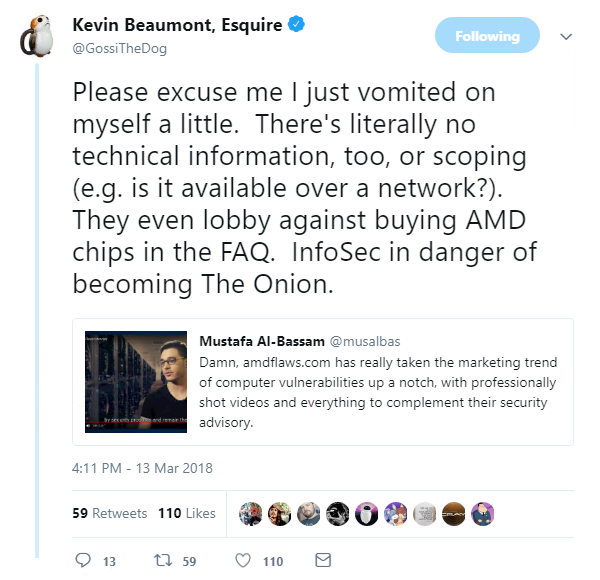
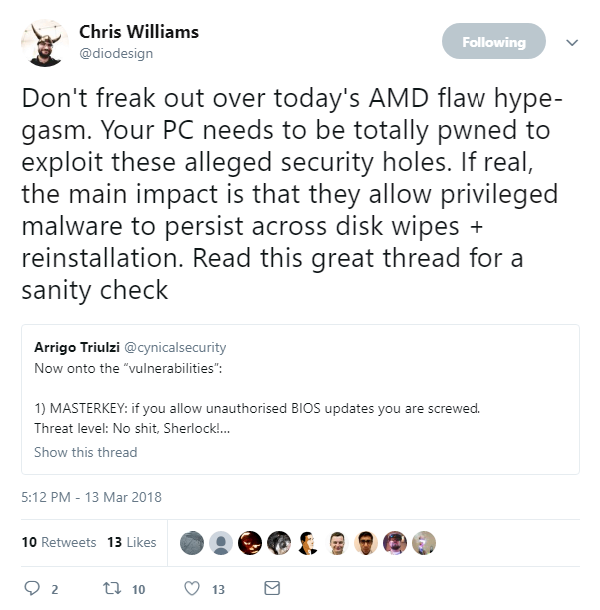
Although some outlets appeared to take Tuesday’s security alert at face value, suspicions surrounding the credibility (and motives) of CTS-Labs soon started to grow, with many industry experts decrying the distinct lack of technical details:
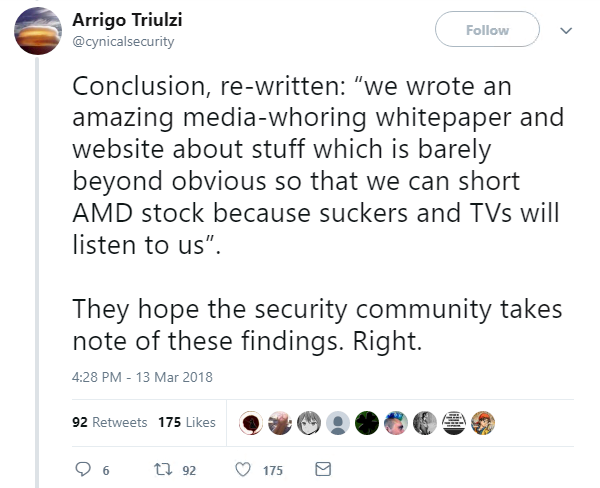
Seeking Alpha stock-watcher Chris Lau was among the first to urge caution over the claims, with the analyst stating: “The timing of a number of supposed vulnerabilities for [AMD] chips looks suspect.”
The floodgates soon opened up to a wave of derisory comments aimed at CTS-Labs’ unorthodox disclosure methodology and accusations of stock market manipulation:
The Daily Swig will be back on Monday with a full update on the AMD vulnerability incident. In the meantime, anyone looking to get up to speed with the controversies should check out this video blog from Gamers Nexus.
In other news, following reports earlier this month of the record-breaking DDoS amplification attacks against Github and a US service provider, new data indicates that domains owned by hundreds of prominent organizations – including Google, PlayStation and the National Rifle Association – have been targeted using the Memcached exploit.
New statistics from Chinese research company Qihoo 360 Netlab indicate that there were less than 50 DDoS amplification attacks per day prior to February 24. By March 7 this figure had risen to more than 2,000 attacks per day.
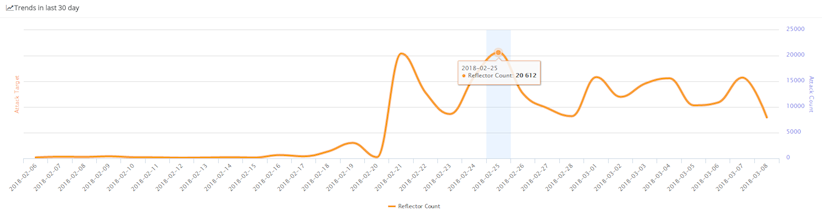
“In less than 10 days, Memcache DDoS attack has come out of nowhere and really captured lots of attentions within the security community,” said 360 Netlab.
“Overall, the current victims are mainly concentrated in the US, China, South Korea, Brazil, France, Germany, the UK, Canada, and the Netherlands.”
Elsewhere, Sir Tim Berners-Lee, the inventor of the world wide web, has called for the regulation of technology firms to prevent the web from being “weaponized at scale”.
In an open letter to the technology community, timed to coincide with the web’s 29th birthday on March 12, the British computer scientist and director of the World Wide Web Consortium stressed the need to close the digital divide and bring more voices to the debate on the web’s future.
“The fact that power is concentrated among so few companies has made it possible to weaponize the web at scale,” he said.
“Companies are aware of the problems and are making efforts to fix them. The responsibility… falls on companies that have been built to maximize profit more than to maximize social good. A legal or regulatory framework that accounts for social objectives may help ease those tensions.”
And in mobile news, Australia’s Department of Defense (DoD) has banned its employees from using WeChat, the popular instant messaging and social media app on their work phones, following security concerns:
Developed by Shenzhen-based Tencent Holdings, WeChat is by far the most popular messaging app in mainland China, and its global active user base was nearing the one billion mark as of the second quarter of 2017.
However, this has done little to allay the concerns of the DoD, which is understood to be conducting a security audit of the app following a rise in foreign espionage activities taking place Down Under.
Of course, this isn’t the first time we have seen foreign-owned software being banned by governments. In December, President Donald Trump signed new legislation that banned the use of Kaspersky Lab within the US government, amid concerns the Moscow-based antivirus firm was vulnerable to Kremlin influence.