Malware, card skimmers, and phishing campaigns all threaten to ruin the romantic spirit

Valentine’s Day. A joyous occasion filled with cards, flowers, and chocolates, which can quickly be dampened by falling victim to a cyber-scam.
Dating website scams, which see lonely singles targeted for their cash, often make headlines. The Federal Trade Commission this week reported that more money was lost to romance scams in the US than any other type of fraud in 2018.
But while catfishing may be easier to spot thanks to some degree of public awareness, there are still hidden threats lurking online.
Malware, card skimmers, and phishing campaigns all threaten to ruin the holiday spirit today – here’s what to look out for:
E-cards
E-cards – digital greetings cards – are a thrifty but fun way to show someone you care on Valentine’s Day.
But even just opening a malicious email can trigger the download of nefarious software onto your computer.
These risks are often hidden in an image, such as one in an e-card, or in a suspicious link that can cause malware to be installed automatically.
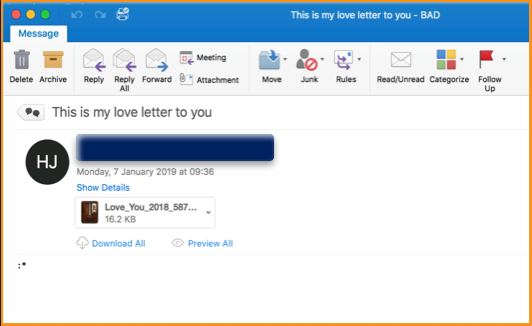
Today, Mimecast reported that the GandCrab ransomware is being spread via fake Valentine’s Day e-cards.
The emails contain a file which, when downloaded, encrypts the victim’s files and changes the file extensions.
It also deletes shadow copies which can be used to decrypt files without paying the ransom, leaving the victim with no choice but to pay out.
The risk of falling victim to ransomware campaigns such as GandCrab can be decreased by taking simple safety steps.
Always check the email address before opening any message containing an attachment, and look out for spoof email address masquerading as popular vendors.
You can check that an address is legit by searching online or by contacting the company via the contacts listed on their website.
Either way, it goes without saying that you should never open an email from a suspicious address.
Online shopping
If you’re shopping online this holiday season, don’t leave your wallet wide open to thieves.
Valentine’s Day is primetime for crooks looking to make money through selling fake goods or pilfering credit card details.
One way cybercriminals get their hands on card details is through the use of card skimmers, which can perform ‘form grabbing’.
A popular technique, Magecart, is an evolution of the now 18-year-old Cart32 shopping cart software backdoor and takes the form of malicious JavaScript injected onto a site’s payment page.
Once installed, the script collects all form data entered by a user – including their name, cards details, and CVV number – and uploads it to a remote server under the attacker’s control.
It has so far been blamed for a number of high-profile security breaches including British Airways, Ticketmaster, Newegg, and Vision Direct.
This data can be used to clone cards or buy goods online, granted the victim hasn’t noticed and cancelled their card already.
Unfortunately, there’s no way of knowing whether a legit website has been injected with malicious code, so it’s worth always keeping an your bank account for any suspicious activity.
But often card-skimmers are placed on fake websites that scammers promote to lure in their victims – so make sure that the sponsored link at the top of Google isn’t dubious.
Phishing
In the run-up to Valentine’s Day, you’re likely to have been bombarded with special offers landing in your email inbox or via SMS message.
Cyber-scammers take advantage of this trend with phishing emails or SMS – ‘smishing’ – messages packed with special offers – with added malicious links.
“Phishing threat actors are always looking to exploit major events in their scams and Valentine’s Day is one of these events,” Crane Hassold, senior director of threat research at Agari, told The Daily Swig.
“In the days leading up to Valentine’s Day, there is a reasonable expectation that e-cards will be sent from friends or family and various companies will be promoting sales via email.
“Scammers take advantage of this by crafting their malicious emails around the same themes to blend into the crowd.”
Be wary of emails that appear to be from companies you haven’t shopped with before, as they’re less likely to have your details, and scrutinize the email address.
Does the body text contain typos? Are the images not professional quality? If something looks suspicious, it probably is.
Hassold concluded: “From a protection and prevention standpoint, the same principles apply: be on the lookout for unexpected emails from unknown senders, don’t click on suspicious links or attachments, and stop and take a second to think about the content of an email before taking action.”






