Open source tool allows researchers to trial their XSS payloads in polymorphic images
A new open source tool for testing the validity of polymorphic cross-site scripting (XSS) payloads across popular web-based image processing libraries was used to poke holes in Google Scholar. The hack netted security researchers $10,000 in the process.
A polymorphic image file is one that contains additional embedded code. This code could be in the file header, concatenated at the end of the image file, or within the image metadata.
Researchers have previously shown (PDF) how polymorphic images can be used to harbor web security exploits – in particular, JavaScript-based XSS payloads, which when rendered in a browser via a script tag can be used to compromise a visiting user.
The successful execution of image-based exploits is often far from straightforward, not least because the resizing process that takes place during image uploads can often break the payload.
Moreover, in an effort to thwart the efforts of attackers looking to smuggle malicious code within image files, web-based image processing libraries will often attempt to strip out any metadata and reprocess the picture upon upload.
However, security researchers from Doyensec have shown how these mitigations aren’t always watertight and how image files can be tweaked to ensure the polymorphic payload survives any processing.
Open source test suite
Doyensec last week officially rolled out a Standardized Image Processing Test Suite – an open source tool that allows security researchers to test their polymorphic image payloads locally.
The tool currently supports four popular image processing libraries: Intervention, Imagine, MiniMagick, and Sharp.
“The test suite is a first step towards exploring the differences between the most popular image processing libraries when converting a polymorphic image,” Doyensec’s Lorenzo Stella told The Daily Swig.
“Many secure image upload libraries already perform various checks such as validating the image file format, heuristically checking for unwanted bytes in its sections, or cleaning EXIF’s metadata.
“Our tool can facilitate the tedious work of discovering bypasses in security checks implemented by image upload services, hence we expect other researchers to leverage the tool during security testing efforts or bug bounties.”
Google Scholar, schooled
Demonstrating the capabilities of the image processing test suite, Stella focused his efforts on Google Scholar, the academic search engine.
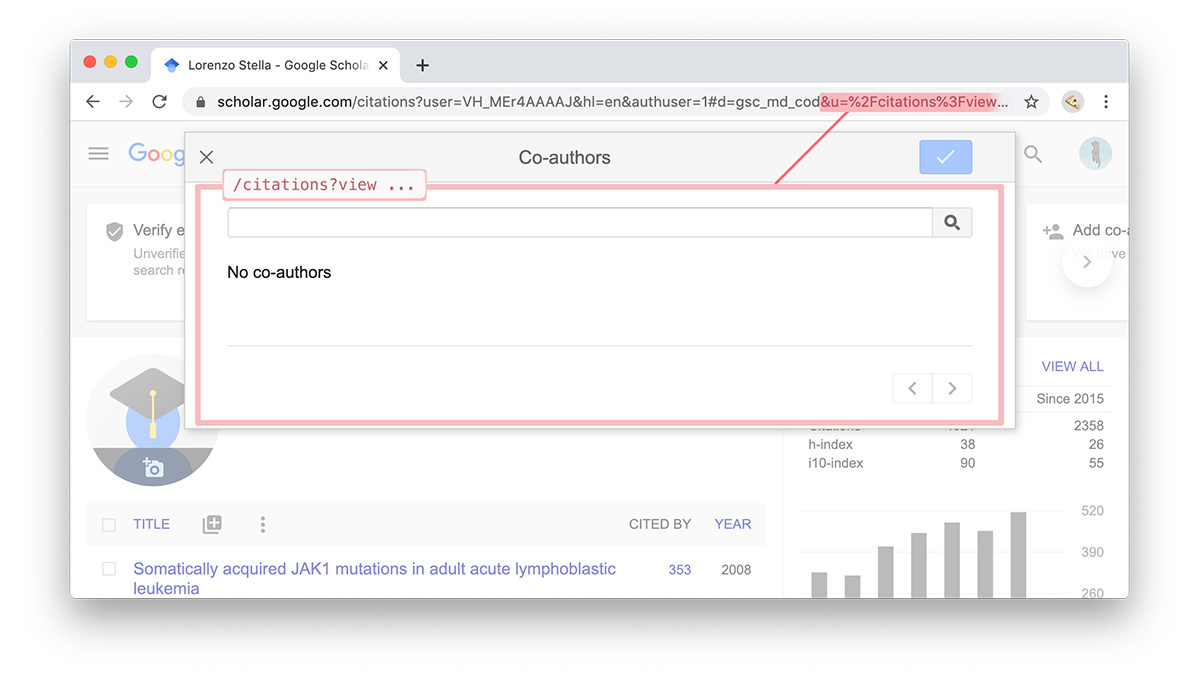
“The first payload I created was embedding an ‘onclick’ event trigger, while the second (‘mouseover’) was a more obvious PoC requested by the VRP [Google’s Vulnerability Reward Program] team for reproducibility purposes,” Stella explained.
Google awarded the researcher nearly $6,300 for his discovery and bumped this up by a further $3,100 after finding another XSS vulnerability using the same technique elsewhere.
Doyensec offered a full rundown of their Google Scholar exploits in a blog post.
READ MORE ParamSpider: New tool helps in the discovery of URL parameter vulnerabilities






