A lesson in how to achieve maximum value for your discoveries
Two Italian security researchers have netted more than $46,000 in bounties for the discovery of an Akamai misconfiguration, despite receiving nothing from Akamai itself.
Akamai is one of the most widely used content delivery networks (CDNs) in the world, used by more than a thousand companies including Apple, Microsoft, Airbnb, and the US Department of Defense.
While hunting for bugs in a website using Akamai via bug bounty platform Whitejar, researchers Jacopo Tediosi and Francesco Mariani discovered a misconfiguration that allowed them to poison the cache with arbitrary content.
Read more of the latest bug bounty research
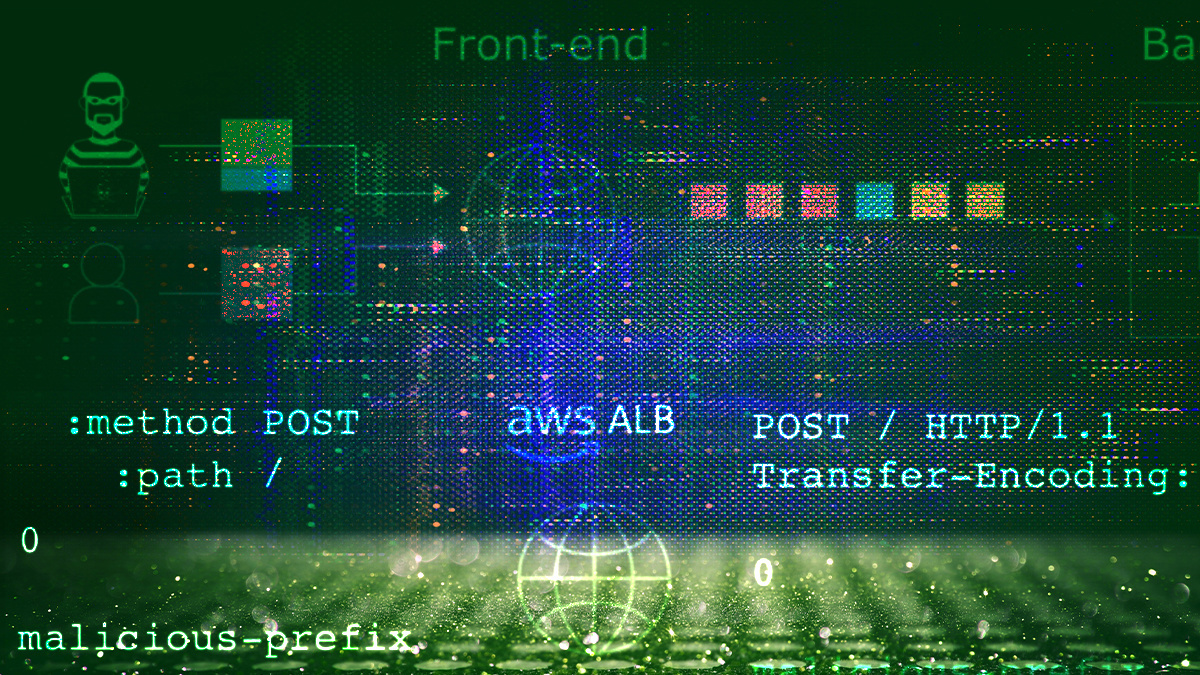
The vulnerability is a combination of common HTTP smuggling and hop-by-hop headers abuse techniques, the researchers said.
Special headers named ‘hop-by-hop’ are removed from proxies before forwarding requests to the next proxy or the destination.
However, specifying the Content-Length header as ‘hop-by-hop’ led Akamai Edge Nodes to remove it. This caused a desynchronization with subsequent nodes, which interpreted part of the HTTP request as a separate, second new request.
This second response was queued and was subsequently sent in response to requests from other clients or users, causing a HTTP smuggling vulnerability.
“An attacker could have inserted malicious arbitrary content into any domain served by the Akamai network, affecting their major customers such as the US Department of Defense, PayPal, Airbnb, Mastercard, PlayStation, Microsoft, Apple, etc,” Tediosi told The Daily Swig.
“This means that they could alter the appearance and behaviour of those websites as they wish. They could also make users’ browsers perform unintended actions on the original sites, as if the users were doing them.”
Fixes available
The company has since fixed the issue by preventing the specification of the Content-Length keyword within the Connection header value, although an advisory has not yet been published.
Tediosi and Mariani contacted Akamai on March 24 and arranged to coordinate disclosure, with a silent fix deployed on April 2. Unfortunately, they were told at the start of the process that the company doesn’t offer bug bounties or other rewards.
However, while Akamai was working on the patch the pair decided to try and pursue bounties from some of the company’s customers.
“It was the only way to get our work rewarded, as Akamai didn’t have a bug bounty program. I honestly didn’t want to use this solution, but it worked anyway and allowed us to stay ethical,” says Tediosi.
“It worries me a little that difficulties like these may tempt researchers not to report vulnerabilities they find, leaving security holes around the web, or even worse, selling them in black markets.”
The pair immediately received $5,000 from Whitejar for the original research. And while a number of bug bounty platforms and organizations – including Bugcrowd, Microsoft, and Apple – were unable to replicate the vulnerability, others were happy to pay up.
The bounties included $25,200 from PayPal, $14,875 from Airbnb, $4,000 from Hyatt Hotels, $750 from Valve, $450 from Zomato, and $100 from Goldman Sachs.
Tediosi says he believes that the use of hop-by-hop headers for smuggling may affect other implementations besides Akamai and deserves further research. In addition, he suggests, it may be possible to bypass Akamai’s fix.
RECOMMENDED Browser-powered desync: A new class of HTTP request smuggling attacks






