Print spooler exploits were on full display at Black Hat 2020
A decade after the Stuxnet malware attack sabotaged Iran’s nuclear enrichment centrifuges, Microsoft has still not fully fixed all of the security vulnerabilities that were exploited by the virus.
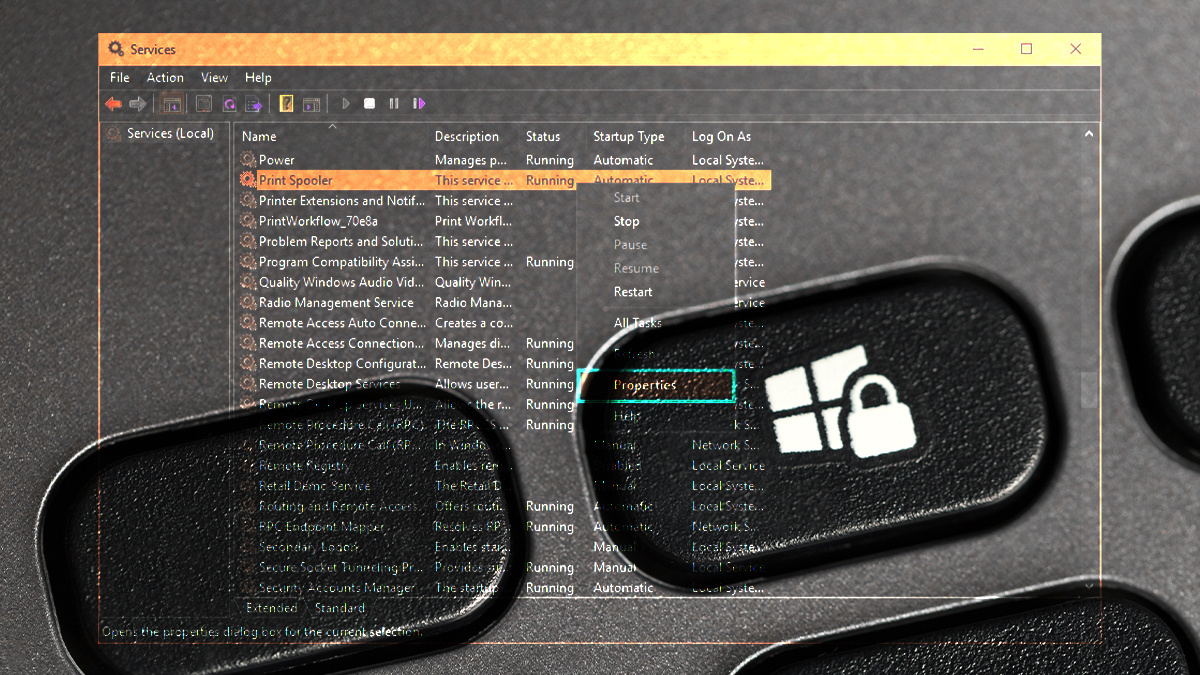
Revisiting their discovery at the virtual Black Hat USA 2020 today, a pair of security researchers said they were astounded to find that the flaws in the Windows print spooler component were still exploitable, using fresh techniques.
Peleg Hadar and Tomer Bar of SafeBreach Labs demonstrated how they achieved denial of service (DoS) via one of the flaws, and local privilege escalation (LPE) as SYSTEM, plus a hitherto unknown persistence technique in another – all within a Windows 10 environment.
Print spooler 101
The print spooler is the primary component of Windows’ printing interface. The executable retrieves and loads the Windows printer driver and schedules print jobs.
Hadar and Bar decided to probe the spooler because “it was the only mechanism which was exploited by Stuxnet and wasn’t re-exploited during the last decade”.
The component, which deploys several processes when printing, had barely changed in 20 years, they discovered. “We can only assume that it didn’t contain any known issues,” they told The Daily Swig.
DoS to SYSTEM access
The researchers decided to begin their research by fuzzing shadow (SHD) files within the spool (SPL) files because the format lacked official, up-to-date documentation. (They did eventually unearth some outdated SHD documentation.)
“We asked ourselves some questions,” they said in a white paper documenting the research. “What component is in charge of parsing this file? What does it contain? Is it encrypted? What impact can we have if we change this file?”
This decision was vindicated as it led them to the DoS vulnerability.
Fuzzing also revealed that the print-job creator’s SID was included in the SHD file, meaning “any user can craft an SHD file”, the researchers said.
“Since the Spooler runs as NT AUTHORITY\SYSTEM,” this prompted the assumption that if the print spooler enabled them to “print to a file, maybe we can ‘print’ a malicious file to System32 on behalf of NT AUTHORITY\SYSTEM”.
However, the first attempt was blocked by an RPC impersonation barrier. Undeterred, the research duo then found “a use-case in which the Print Spooler will be able to create and perform our print job using its own SYSTEM token”, and achieved “a privilege escalation from a limited user to NT AUTHORITY\SYSTEM and wrote an arbitrary DLL file in System32.
“As a bonus, multiple Windows services loaded our DLL (wbemcomn.dll) as they didn’t verify the signature and tried to load the DLL from an non-existing path, meaning we also got code execution.”
Into the wild
“Once an attacker gained a limited, unprivileged initial code execution on a Windows machine (for example, by using phishing) they will be able to escalate their privileges by using the vulnerabilities we found in the print spooler mechanism, or cause a denial of service,” the researchers told The Daily Swig ahead of their Black Hat presentation.
Hadar and Bar said they were “not aware of an in-the-wild exploitation of the vulnerabilities” before alerting Microsoft.
However, they “believe that the LPE vulnerability is easy to exploit by several commands”.
“We have seen a tweet of one of the vendors which mentioned an in-the-wild exploitation of CVE-2020-1048 after it was patched, but we can’t confirm it,” the researchers said.
Patch bypass
They reported the two unpatched vulnerabilities in January 2020, and Microsoft fixed the LPE flaw in May 2020 (CVE-2020-1048).
However, a month later in June they “found a way to bypass the patch and re-exploit the vulnerability on the latest Windows version.”
The vulnerability thus created (CVE-2020-1337) will be patched on August’s Patch Tuesday, after which the authors said they will release technical details.
There is no mention of a Dos flaw having been scheduled a fix – The Daily Swig has asked the researchers for clarification.
The LPE flaw is present in Windows releases between Windows 7 and 10 (32 and 64-bit). The DoS flaw is an even older bug, affecting releases dating back to Windows 2000.
Organizations can also minimize their risk by validating that their systems are up-to-date and fully patched, the researchers advised.
You can find the spooler source code and proof-of-concept on SafeLabs’ GitHub repository.
BLACK HAT BRIEFINGS New HTTP request smuggling variants levied against modern web servers






