Top infosec trends in the social media spotlight this week

Following last week’s announcement that Equifax had been slammed with a £500,000 ($380,000) fine by the UK Information Commissioner’s Office, Uber has become the latest Big Biz to settle for breach damages.
The ride-hailing firm admitted last year that a data breach in 2016 saw attackers run away with the personal information of around 57 million customers around the world. It was later revealed that Uber paid the hackers $100,000 to delete the data and remain quiet over the breach.
Now, following an investigation by the Federal Trade Commission, Uber will pay a record $148 million penalty to settle the incident. The company has also agreed to implement a more rigorous data security policy.
Over in Asia, an investigation into the recent cyber-attack against SingHealth – the largest healthcare group in Singapore – has revealed the organization had adopted poor security practices, including the failure to update its servers.
As previously reported in The Daily Swig, the attack earlier this year resulted in the personal information of around 1.5 million individuals being compromised – including that of Prime Minister Lee Hsien Loong.
Taking to the witness stand during the fifth day of public hearings yesterday, Tan Aik Chin, a senior manager at SingHealth’s National Cancer Centre (NCC), said a server that was exploited during the cyber-attack had not been updated since May 2017.
The hearings are expected to continue into next week.
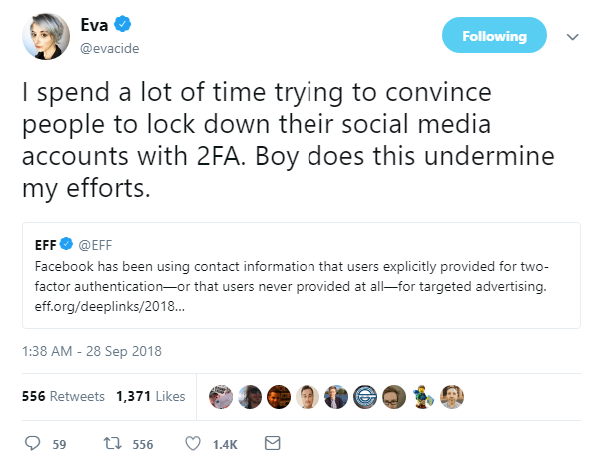
In other news, Facebook has once again found itself under pressure from privacy advocates, following the publication of a report that indicates the social media giant has been using the contact information that users provided for two-factor authentication (2FA) for targeted advertising.
The investigation, conducted by researchers at Northeastern University and Princeton University, found that when a user gives Facebook their number for security purposes – to set up 2FA or to receive login alerts – that phone number can find its way into the hands of advertisers within a matter of weeks.
On the surface, this latest revelation may not appear to be as serious as the Cambridge Analytica scandal. However, as the Electronic Frontier Foundation’s Eva Galperin notes, the mishandling of 2FA data does nothing for those tasked with educating consumers to the security benefits of multi-factor authentication.
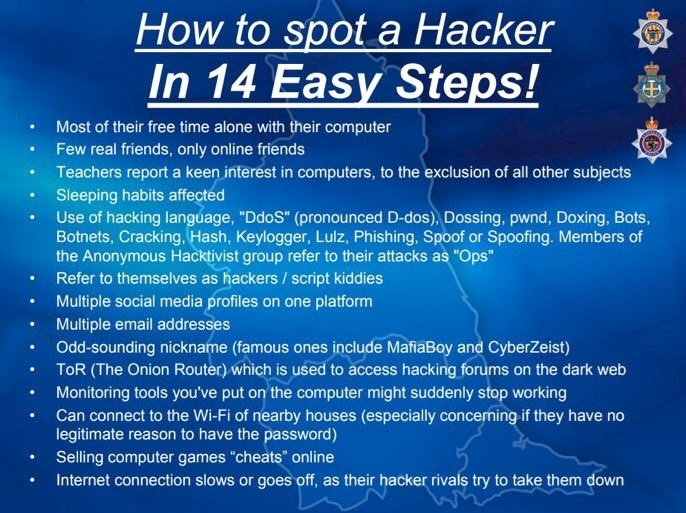
And finally, the Durham Constabulary social media team were called into action this week, after an image attributed to the regional British police force started doing the rounds on Twitter:
The original tweet has since been deleted, but screenshots of the ‘How to Spot a Hacker in 14 Easy Steps!’ slide continued to be shared in infosec circles – no doubt for its sheer cringeworthy value.
Among the red flags to watch out for in a potential hacker, the image suggests, are individuals with “few real friends”, “multiple email addresses”, and “odd-sounding nicknames”.
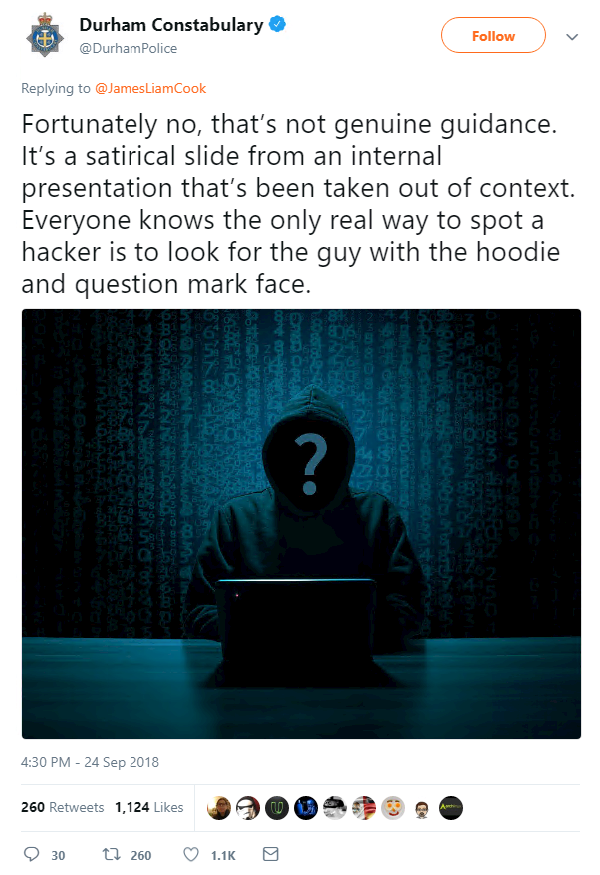
As the security community raised a collective groan, rather than continuing the debate on the nuances of the term ‘hacker’, Durham Constabulary countered with a crafty tweet of its own:
Well played, Durham, well played.