Top infosec trends in the social media spotlight this week

Apple, WhatsApp, and Privacy International have joined forces to criticize GCHQ’s plans to eavesdrop on encrypted chats via the so-called “ghost protocol”.
Tech companies joined with civil society organizations and security experts in calling on GCHQ to abandon its proposals in favor of focusing on “protecting privacy rights”.
The 50-plus signatories laid out their objections in an open letter, the spirit of which is more akin to constructive criticism than condemnation.
The seven-page letter highlights a concern that the proposed approach would break authentication, among other criticisms.
“The GCHQ’s ghost protocol creates serious threats to digital security: if implemented, it will undermine the authentication process that enables users to verify that they are communicating with the right people, introduce potential unintentional vulnerabilities,” the letter (PDF) said.
Eye of the beholder
Chinese artist Guo O Dong’s installation, ‘The Persistence of Chaos’ – a malware-packed laptop – sold through an online auction this week for over $1.3 million.
The Samsung PC, running Windows XP, was deliberately infected with six notorious strains of malicious code by the Banksy of botnets. The piece was isolated and air-gapped to prevent against the risk of it spreading of the malware it harbored.
Infosec Twitter was left non-plussed by the exercise, with no one holding their hand up to argue selling off a PC infected with Love Bug, MyDoom, SoBig, WannaCry, DarkTequila, and BlackEnergy – did anything to raise awareness about the huge disruption and cost associated with ransomware, trojan and other cyber-nasties.
Fair dinkum
A right old flap worthy of an antipodean version of The Thick of It took place in New Zealand this week.
The episode began when a copy of the Labour-led coalition government’s upcoming budget leaked, with the opposition National Party making political capital from the minor breach.
New Zealand’s treasury department’s initial accusations of a “deliberate and systematic” hack was embarrassingly withdrawn the day later after it admitted that a configuration error had exposed the sensitive data.
Another week, another mega-breach
A weakness in the website of First American Financial Corp may have exposed more than 885 million records related to mortgage deals going back to 2003.
Data exposed including all manner of sensitive information including social security numbers, bank account details, driving license scans, mortgage/tax records, and more, investigative reporter Brian Krebs reports.
Sayonara
Japan is moving to limit foreign ownership of firms in its IT and telecommunication sectors.
The proposed plan comes amidst the ongoing row about whether market leader Huawei’s 5G kit creates a systematic security risk, a topic that has taken center stage in the ongoing and escalating US/China trade dispute.
The announcement came on the same day visiting US President Donald Trump met Japanese Prime Minister Shinzo Abe for talks in Tokyo about trade and other issues, Reuters reports.
Japan’s SoftBank telecoms unit has selected Nokia and Ericsson as suppliers for its 5G network, in a snub to Chinese-owned market leader Huawei.
Switch up
On a more positive note, pictures of a keypad that changes its numbers after every entry sequence to stop over-the-shoulder snooping attracted interest over on Reddit this week.
The MIWA Random Tenkey technology does for bank ATMs what an online ‘virtual’ keypad offers for e-banking.
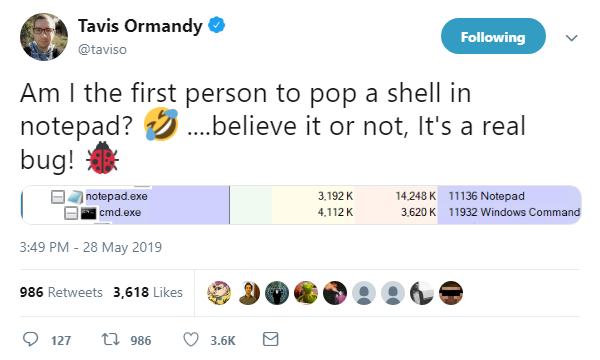
Elsewhere, famed bug hunter Tavis Ormandy earned plenty of kudos from his peers after he ‘popped a shell’ on Notepad.
Ormandy, a vulnerability researcher at Google, said he’d reported the memory corruption exploit that allowed the hack to Microsoft.
You had one job!
Finally, the Dutch Data Protection Authority was left red-faced this week after it failed to report itself on time over a minor data breach that was caused by own of its own employees.
The authority revealed media recipients’ addresses to each other in promoting (of all things) a GDPR awareness campaign.
A staffer made the common mistake of cc’ing journalists on the mailing list for the message, instead of using the ‘bcc’ field.
Compounding the error, the Dutch Data Protection Authority failed to lodge paperwork on the incident with itself within the required three-day deadline.