The new version of Burp employs heuristic rules to recognize most types of content commonly used in web applications. Information about response MIME types is used in various ways, for example:
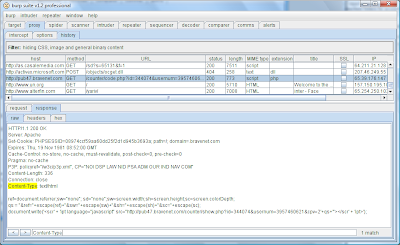
Applications typically include a Content-type header in their responses, which announces the MIME type of the content in the response body. However, it is good not to trust this header, because it is often wrong. Look at the following very common example. The response's Content-type header states that it contains HTML. However, in the MIME type column of the proxy history, the content is correctly identified as JavaScript. If we trusted the MIME type stated by the application, we would handle the response incorrectly, potentially missing some interesting vulnerabilities.