Right-clicking many parts of Burp produces a context menu that can be used to perform various actions. Using the context menu effectively is essential to drive Burp's core workflow. In this article we demonstrate some of the most common use cases for the context menu. Burp's full documentation contains more information regarding Burp's context menu commands.
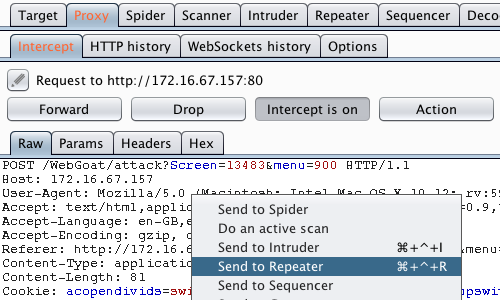
The ability to send requests between tools forms the core of Burp's user-driven workflow.
The Scan / send to ... function allows you to send any message, or a selected portion of the message, to other Burp tools, to perform further attacks or analysis.
The screenshot demonstrates how you could send an item from Burp Proxy to the Repeater tab.
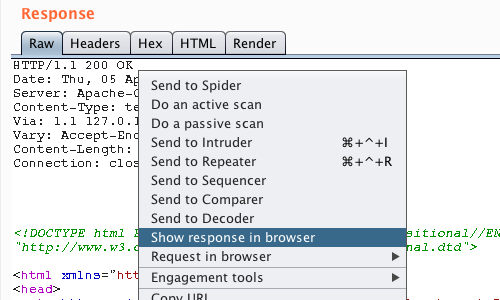
Having sent a request to Burp Repeater and used the Repeater functionality, you may wish to render the response in your browser.
The "Show response in browser" function gives you a unique URL that you can paste into your browser to render the response.
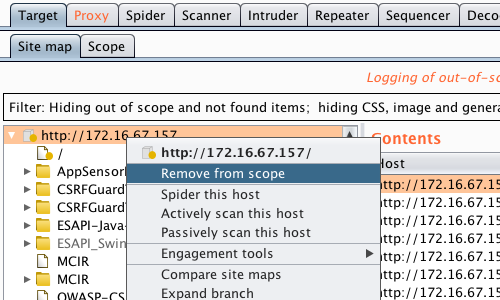
The context menu in the Target > Site map allows you to add and remove items from Burp Suite's scope.
Additionally, you can spider and scan full hosts.
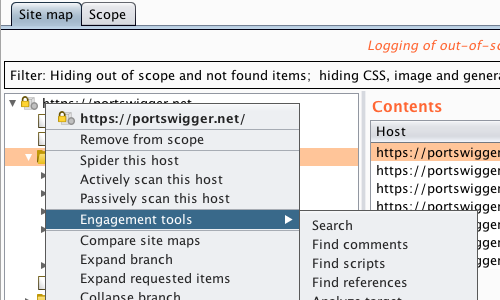
Burp's Engagement tools can be accessed via the context menu.
These tools are designed to enhance the testing process. The tools automate search and reconnaissance tasks to make your testing faster and more efficient.
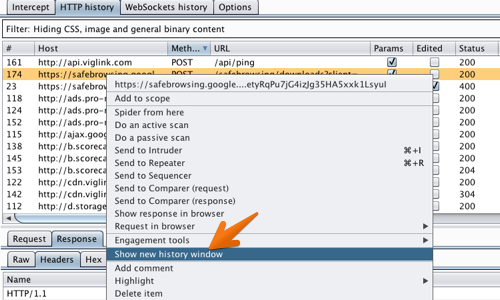
You can open additional views of the Proxy history using the context menu, to apply different filters or help test access controls.


