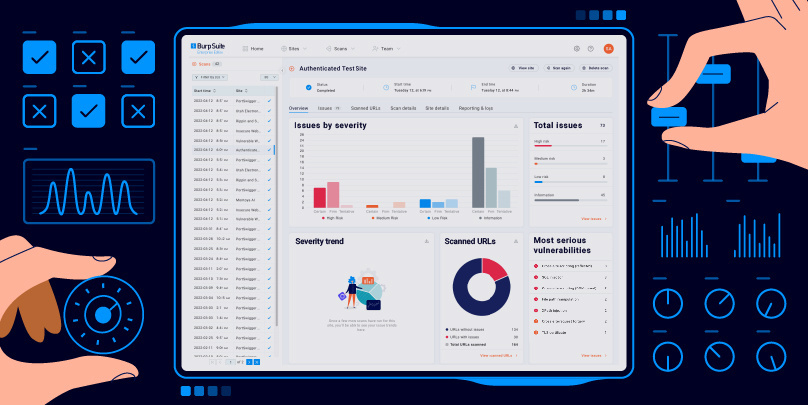
Burp Suite Enterprise Edition is the dynamic web vulnerability scanner that can help you to secure your whole portfolio. To help you achieve that, this article contains some advice on how to optimize your dynamic scanning for a range of requirements.
Ensure Burp Scanner has access to the resources it needs
By its nature, dynamic (DAST) scanning can be resource-intensive. Sometimes, new users mistakenly try to run scans on under-specced machines - or with the wrong setup - which can impede, or even halt Burp Scanner's progress. To avoid this, we recommend that you:
Tip: Burp Suite Enterprise Edition's built-in scan configurations can also assist in reducing scan durations. This is something to try adjusting, if you're seeing longer than expected scan times.
Minimize false positives by adjusting your scan configurations
While dynamic (DAST) scanning generally produces low amounts of false positives, Burp Scanner can (as with any automated tool) occasionally flag issues that turn out to be false. If you want to further improve your signal to noise ratio, you may find the following useful:
Fine-tune Burp Scanner for its target application
Web applications vary greatly in their design and complexity. Fortunately, Burp Scanner includes a range of settings allowing you to prepare it for almost any situation - including complex login sequences and heavily stateful functionality. To extend Burp Scanner's coverage, you may find the following useful:
We hope that this article has been useful. Of course, if you're experiencing a problem that can't be solved using any of the suggestions here, then we'll be happy to help. Please contact PortSwigger Technical Support (if possible, including copies of the logs mentioned in our troubleshooting guide), to help us support you.