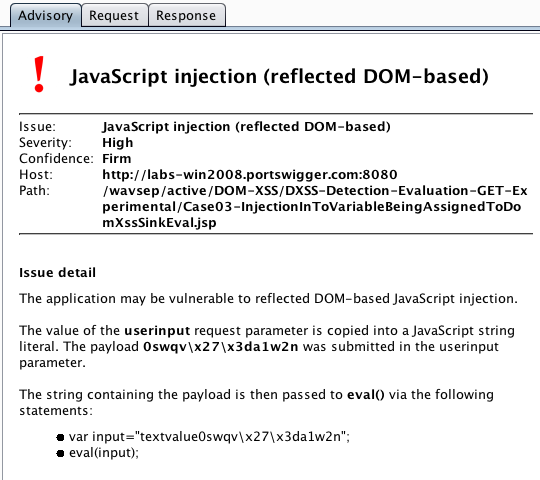
This release adds the capability to report reflected DOM-based and stored DOM-based vulnerabilities.
Burp already reports reflected XSS (where reflection of input allows direct execution of supplied JavaScript) and DOM-based XSS (where data is read from a controllable DOM location and processed in a way that allows execution of JavaScript). Burp now joins these steps together, to handle cases where:
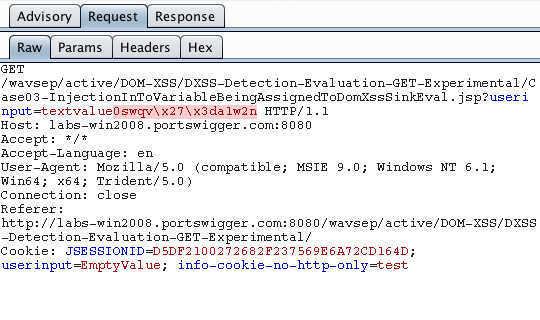
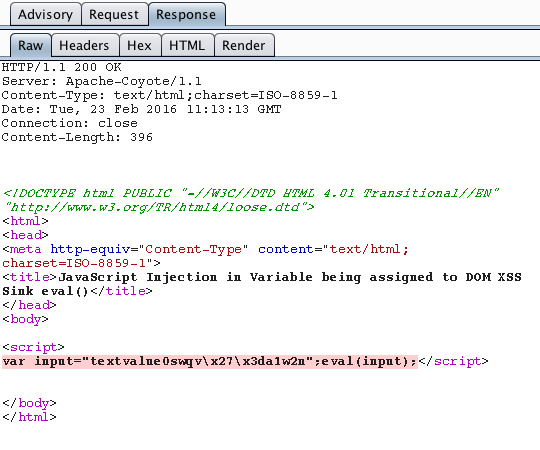
- The server returns reflected or stored input in the value of a JavaScript string.
- That string is processed in a way that allows execution of JavaScript code from within the string.
The new capability applies to all of the DOM-based vulnerability types that Burp can report, such as JavaScript injection, WebSocket hijacking and open redirection.